Compare commits
31 Commits
6225809bf6
...
main
| Author | SHA1 | Date | |
|---|---|---|---|
|
|
461135ee9d | ||
|
|
0e0ca39f0a | ||
|
|
87a5182ac6 | ||
|
|
b94eef4848 | ||
|
|
37707302bb | ||
|
|
dbdc8f528b | ||
|
|
04cda8c4ca | ||
|
|
a7640075cb | ||
|
|
31139ae077 | ||
|
|
604b48ca70 | ||
|
|
1577e5e731 | ||
|
|
3f4479157b | ||
|
|
cd8705ad9e | ||
|
|
24153a40b4 | ||
|
|
d5e1774aad | ||
|
|
cbca8c0233 | ||
|
|
2e0a28b28d | ||
|
|
e1ed310a2e | ||
|
|
f37253b471 | ||
|
|
4823eefff6 | ||
|
|
94bfe0b0f1 | ||
|
|
2f33f6a9a3 | ||
|
|
c663850ee2 | ||
|
|
9c506ec0c1 | ||
|
|
29d77747fb | ||
|
|
59526193d5 | ||
|
|
69174f2157 | ||
|
|
1221e03ac3 | ||
|
|
70bdce97aa | ||
|
|
51c64ac563 | ||
|
|
eb476b26ce |
301
.gitignore
vendored
301
.gitignore
vendored
@@ -1,149 +1,152 @@
|
|||||||
# Logs
|
# Logs
|
||||||
logs
|
logs
|
||||||
*.log
|
*.log
|
||||||
npm-debug.log*
|
npm-debug.log*
|
||||||
yarn-debug.log*
|
yarn-debug.log*
|
||||||
yarn-error.log*
|
yarn-error.log*
|
||||||
lerna-debug.log*
|
lerna-debug.log*
|
||||||
.pnpm-debug.log*
|
.pnpm-debug.log*
|
||||||
|
|
||||||
# Diagnostic reports (https://nodejs.org/api/report.html)
|
# Diagnostic reports (https://nodejs.org/api/report.html)
|
||||||
report.[0-9]*.[0-9]*.[0-9]*.[0-9]*.json
|
report.[0-9]*.[0-9]*.[0-9]*.[0-9]*.json
|
||||||
|
|
||||||
# Runtime data
|
# Runtime data
|
||||||
pids
|
pids
|
||||||
*.pid
|
*.pid
|
||||||
*.seed
|
*.seed
|
||||||
*.pid.lock
|
*.pid.lock
|
||||||
|
|
||||||
# Directory for instrumented libs generated by jscoverage/JSCover
|
# Directory for instrumented libs generated by jscoverage/JSCover
|
||||||
lib-cov
|
lib-cov
|
||||||
|
|
||||||
# Coverage directory used by tools like istanbul
|
# Coverage directory used by tools like istanbul
|
||||||
coverage
|
coverage
|
||||||
*.lcov
|
*.lcov
|
||||||
|
|
||||||
# nyc test coverage
|
# nyc test coverage
|
||||||
.nyc_output
|
.nyc_output
|
||||||
|
|
||||||
# Grunt intermediate storage (https://gruntjs.com/creating-plugins#storing-task-files)
|
# Grunt intermediate storage (https://gruntjs.com/creating-plugins#storing-task-files)
|
||||||
.grunt
|
.grunt
|
||||||
|
|
||||||
# Bower dependency directory (https://bower.io/)
|
# Bower dependency directory (https://bower.io/)
|
||||||
bower_components
|
bower_components
|
||||||
|
|
||||||
# node-waf configuration
|
# node-waf configuration
|
||||||
.lock-wscript
|
.lock-wscript
|
||||||
|
|
||||||
# Compiled binary addons (https://nodejs.org/api/addons.html)
|
# Compiled binary addons (https://nodejs.org/api/addons.html)
|
||||||
build/Release
|
build/Release
|
||||||
|
|
||||||
# Dependency directories
|
# Dependency directories
|
||||||
node_modules/
|
node_modules/
|
||||||
jspm_packages/
|
jspm_packages/
|
||||||
|
|
||||||
# Snowpack dependency directory (https://snowpack.dev/)
|
# Snowpack dependency directory (https://snowpack.dev/)
|
||||||
web_modules/
|
web_modules/
|
||||||
|
|
||||||
# TypeScript cache
|
# TypeScript cache
|
||||||
*.tsbuildinfo
|
*.tsbuildinfo
|
||||||
|
|
||||||
# Optional npm cache directory
|
# Optional npm cache directory
|
||||||
.npm
|
.npm
|
||||||
|
|
||||||
# Optional eslint cache
|
# Optional eslint cache
|
||||||
.eslintcache
|
.eslintcache
|
||||||
|
|
||||||
# Optional stylelint cache
|
# Optional stylelint cache
|
||||||
.stylelintcache
|
.stylelintcache
|
||||||
|
|
||||||
# Microbundle cache
|
# Microbundle cache
|
||||||
.rpt2_cache/
|
.rpt2_cache/
|
||||||
.rts2_cache_cjs/
|
.rts2_cache_cjs/
|
||||||
.rts2_cache_es/
|
.rts2_cache_es/
|
||||||
.rts2_cache_umd/
|
.rts2_cache_umd/
|
||||||
|
|
||||||
# Optional REPL history
|
# Optional REPL history
|
||||||
.node_repl_history
|
.node_repl_history
|
||||||
|
|
||||||
# Output of 'npm pack'
|
# Output of 'npm pack'
|
||||||
*.tgz
|
*.tgz
|
||||||
|
|
||||||
# Yarn Integrity file
|
# Yarn Integrity file
|
||||||
.yarn-integrity
|
.yarn-integrity
|
||||||
|
|
||||||
# dotenv environment variable files
|
# dotenv environment variable files
|
||||||
.env
|
.env
|
||||||
.env.development.local
|
.env.development.local
|
||||||
.env.test.local
|
.env.test.local
|
||||||
.env.production.local
|
.env.production.local
|
||||||
.env.local
|
.env.local
|
||||||
|
|
||||||
# parcel-bundler cache (https://parceljs.org/)
|
# parcel-bundler cache (https://parceljs.org/)
|
||||||
.cache
|
.cache
|
||||||
.parcel-cache
|
.parcel-cache
|
||||||
|
|
||||||
# Next.js build output
|
# Next.js build output
|
||||||
.next
|
.next
|
||||||
out
|
out
|
||||||
|
|
||||||
# Nuxt.js build / generate output
|
# Nuxt.js build / generate output
|
||||||
.nuxt
|
.nuxt
|
||||||
dist
|
dist
|
||||||
|
|
||||||
# Gatsby files
|
# Gatsby files
|
||||||
.cache/
|
.cache/
|
||||||
# Comment in the public line in if your project uses Gatsby and not Next.js
|
# Comment in the public line in if your project uses Gatsby and not Next.js
|
||||||
# https://nextjs.org/blog/next-9-1#public-directory-support
|
# https://nextjs.org/blog/next-9-1#public-directory-support
|
||||||
# public
|
# public
|
||||||
|
|
||||||
# vuepress build output
|
# vuepress build output
|
||||||
.vuepress/dist
|
.vuepress/dist
|
||||||
|
|
||||||
# vuepress v2.x temp and cache directory
|
# vuepress v2.x temp and cache directory
|
||||||
.temp
|
.temp
|
||||||
.cache
|
.cache
|
||||||
|
|
||||||
# Docusaurus cache and generated files
|
# Docusaurus cache and generated files
|
||||||
.docusaurus
|
.docusaurus
|
||||||
|
|
||||||
# Serverless directories
|
# Serverless directories
|
||||||
.serverless/
|
.serverless/
|
||||||
|
|
||||||
# FuseBox cache
|
# FuseBox cache
|
||||||
.fusebox/
|
.fusebox/
|
||||||
|
|
||||||
# DynamoDB Local files
|
# DynamoDB Local files
|
||||||
.dynamodb/
|
.dynamodb/
|
||||||
|
|
||||||
# TernJS port file
|
# TernJS port file
|
||||||
.tern-port
|
.tern-port
|
||||||
|
|
||||||
# Stores VSCode versions used for testing VSCode extensions
|
# Stores VSCode versions used for testing VSCode extensions
|
||||||
.vscode-test
|
.vscode-test
|
||||||
|
|
||||||
# yarn v2
|
# yarn v2
|
||||||
.yarn/cache
|
.yarn/cache
|
||||||
.yarn/unplugged
|
.yarn/unplugged
|
||||||
.yarn/build-state.yml
|
.yarn/build-state.yml
|
||||||
.yarn/install-state.gz
|
.yarn/install-state.gz
|
||||||
.pnp.*
|
.pnp.*
|
||||||
|
|
||||||
# vscode
|
# vscode
|
||||||
.vscode
|
.vscode
|
||||||
|
|
||||||
# analytics
|
# analytics
|
||||||
analyze/
|
analyze/
|
||||||
|
|
||||||
# heapsnapshot
|
# heapsnapshot
|
||||||
*.heapsnapshot
|
*.heapsnapshot
|
||||||
|
|
||||||
# turbo
|
# turbo
|
||||||
.turbo/
|
.turbo/
|
||||||
|
|
||||||
# pagefind postbuild
|
# pagefind postbuild
|
||||||
public/_pagefind/
|
public/_pagefind/
|
||||||
public/sitemap.xml
|
public/sitemap.xml
|
||||||
|
|
||||||
# npm package lock file for different platforms
|
# npm package lock file for different platforms
|
||||||
package-lock.json
|
package-lock.json
|
||||||
|
|
||||||
|
# generated
|
||||||
|
mcp-worker/generated
|
||||||
79
README.md
79
README.md
@@ -1,38 +1,53 @@
|
|||||||
# NoteNextra
|
# NoteNextra
|
||||||
|
|
||||||
Static note sharing site with minimum care
|
Static note sharing site with minimum care
|
||||||
|
|
||||||
This site is powered by
|
This site is powered by
|
||||||
|
|
||||||
- [Next.js](https://nextjs.org/)
|
- [Next.js](https://nextjs.org/)
|
||||||
- [Nextra](https://nextra.site/)
|
- [Nextra](https://nextra.site/)
|
||||||
- [Tailwind CSS](https://tailwindcss.com/)
|
- [Tailwind CSS](https://tailwindcss.com/)
|
||||||
- [Vercel](https://vercel.com/)
|
- [Vercel](https://vercel.com/)
|
||||||
|
|
||||||
## Deployment
|
## Deployment
|
||||||
|
|
||||||
### Deploying to Vercel
|
### Deploying to Vercel
|
||||||
|
|
||||||
[](https://vercel.com/new/clone?repository-url=https%3A%2F%2Fgithub.com%2FTrance-0%2FNotechondria)
|
[](https://vercel.com/new/clone?repository-url=https%3A%2F%2Fgithub.com%2FTrance-0%2FNotechondria)
|
||||||
|
|
||||||
_Warning: This project is not suitable for free Vercel plan. There is insufficient memory for the build process._
|
_Warning: This project is not suitable for free Vercel plan. There is insufficient memory for the build process._
|
||||||
|
|
||||||
### Deploying to Cloudflare Pages
|
### Deploying to Cloudflare Pages
|
||||||
|
|
||||||
[](https://deploy.workers.cloudflare.com/?url=https://github.com/Trance-0/Notechondria)
|
[](https://deploy.workers.cloudflare.com/?url=https://github.com/Trance-0/Notechondria)
|
||||||
|
|
||||||
### Deploying as separated docker services
|
### Deploying as separated docker services
|
||||||
|
|
||||||
Considering the memory usage for this project, it is better to deploy it as separated docker services.
|
Considering the memory usage for this project, it is better to deploy it as separated docker services.
|
||||||
|
|
||||||
```bash
|
```bash
|
||||||
docker-compose up -d -f docker/docker-compose.yaml
|
docker-compose up -d -f docker/docker-compose.yaml
|
||||||
```
|
```
|
||||||
|
|
||||||
### Snippets
|
### Snippets
|
||||||
|
|
||||||
Update dependencies
|
Update dependencies
|
||||||
|
|
||||||
```bash
|
```bash
|
||||||
npx npm-check-updates -u
|
npx npm-check-updates -u
|
||||||
```
|
```
|
||||||
|
|
||||||
|
### MCP access to notes
|
||||||
|
|
||||||
|
This repository includes a minimal MCP server that exposes the existing `content/` notes as a knowledge base for AI tools over stdio.
|
||||||
|
|
||||||
|
```bash
|
||||||
|
npm install
|
||||||
|
npm run mcp:notes
|
||||||
|
```
|
||||||
|
|
||||||
|
The server exposes:
|
||||||
|
|
||||||
|
- `list_notes`
|
||||||
|
- `read_note`
|
||||||
|
- `search_notes`
|
||||||
|
|||||||
770
content/CSE4303/CSE4303_E1.md
Normal file
770
content/CSE4303/CSE4303_E1.md
Normal file
@@ -0,0 +1,770 @@
|
|||||||
|
# CSE4303 Introduction to Computer Security (Exam Review)
|
||||||
|
|
||||||
|
## Details
|
||||||
|
|
||||||
|
Time and location
|
||||||
|
|
||||||
|
– In class exam – Thursday, 3/5 at 11:30 AM
|
||||||
|
– What is allowed:
|
||||||
|
- One 8.5" X 11" paper of notes, single-sided only, typed or hand-written
|
||||||
|
|
||||||
|
Topics covered:
|
||||||
|
|
||||||
|
– Security fundamentals
|
||||||
|
– TCP/IP network stack
|
||||||
|
– Crypto fundamentals
|
||||||
|
– Symmetric key cryptography
|
||||||
|
– Hash functions
|
||||||
|
– Asymmetric key cryptography
|
||||||
|
|
||||||
|
## Security fundamentals
|
||||||
|
|
||||||
|
### Defining security
|
||||||
|
|
||||||
|
- Understand principles of security analysis
|
||||||
|
- The security of a system, application, or protocol is always relative to
|
||||||
|
- A set of desired properties
|
||||||
|
- An adversary with specific capabilities ("threat model")
|
||||||
|
|
||||||
|
### Key security concepts
|
||||||
|
|
||||||
|
C.I.A. triad:
|
||||||
|
|
||||||
|
- Integrity: Prevent unauthorized modification of data, and/or detect if modification occurred.
|
||||||
|
- ARP poisoning (ARP spoofing)
|
||||||
|
- Authentication codes
|
||||||
|
- Confidentiality: Prevent unauthorized parties from learning the contents of data (in transit or at rest).
|
||||||
|
- Packet sniffing / eavesdropping
|
||||||
|
- Data encryption
|
||||||
|
- Availability: Ensure systems and data are accessible to authorized users when needed.
|
||||||
|
- Denial-of-Service (DoS) / Distributed DoS (DDoS)
|
||||||
|
- Rate limiting + traffic filtering (often with DDoS protection/CDN)
|
||||||
|
|
||||||
|
Other security goals:
|
||||||
|
|
||||||
|
- Authenticity: identity of an entity (issuer of info/message) is verified
|
||||||
|
- Anonymity: identity of an entity remains unknown
|
||||||
|
- Non-repudiation: messages can't be denied or taken back (e.g. online transaction commitments)
|
||||||
|
|
||||||
|
### Modeling attacks
|
||||||
|
|
||||||
|
Common components:
|
||||||
|
|
||||||
|
- System being attacked (usually a model, with assumptions and abstractions)
|
||||||
|
- Threat model
|
||||||
|
- Attack surface: what can be attacked
|
||||||
|
- Open ports and exposed services
|
||||||
|
- Public APIs and their parameters
|
||||||
|
- Web endpoints, forms, cookies
|
||||||
|
- File system permissions
|
||||||
|
- Hardware interfaces (USB, JTAG)
|
||||||
|
- User roles and privilege boundaries
|
||||||
|
- Attack vector: how the attacker attacks
|
||||||
|
- SQL injection via POST /login
|
||||||
|
- Phishing to steal credentials, then SSH login
|
||||||
|
- Buffer overflow in a network daemon
|
||||||
|
- Cross-site scripting through a comment field
|
||||||
|
- Supply-chain poisoning of a dependency
|
||||||
|
- Vulnerability: what the attacker can do
|
||||||
|
- Exploit: how the attacker exploits the vulnerability
|
||||||
|
- Damage: what the attacker can do
|
||||||
|
- Mitigation: mitigate vulnerability
|
||||||
|
- Defense: close vulnerability gap
|
||||||
|
|
||||||
|
Importance of correct modeling
|
||||||
|
|
||||||
|
- Attack-surface awareness guides defenses
|
||||||
|
- E.g. pre-Covid-19 vs. post-Covid attack surface of company servers
|
||||||
|
- Match resources to expected threat actors
|
||||||
|
- "Script kiddie": individual or group running off-the-shelf attacks
|
||||||
|
- Caveat: off-the-shelf attacks can still be quite powerful! Metasploit, Shodan, dark web market.
|
||||||
|
- "Insider attack": employee with access to internal machines/networks
|
||||||
|
- "Advanced Persistent Threat (APT)": nation-state level resources and patience
|
||||||
|
- All these threats have different motivations, require different defenses/responses!
|
||||||
|
- Reevaluate often
|
||||||
|
- Threat capabilities change over time
|
||||||
|
|
||||||
|
### TCP/IP network stack
|
||||||
|
|
||||||
|
Local and interdomain routing
|
||||||
|
|
||||||
|
- TCP/IP for routing and messaging
|
||||||
|
- BGP for routing announcements
|
||||||
|
|
||||||
|
Domain Name System
|
||||||
|
|
||||||
|
- Find IP address from symbolic name (cse.wustl.edu)
|
||||||
|
|
||||||
|
#### Layer Summary
|
||||||
|
|
||||||
|
Application: the actual sending message
|
||||||
|
Transport (TCP, UDP): segment
|
||||||
|
Network (IP): packet
|
||||||
|
Data Link (Ethernet): frame
|
||||||
|
|
||||||
|
### Types of Addresses in Internet
|
||||||
|
|
||||||
|
- Media Access Control (MAC) addresses in the network access layer
|
||||||
|
- Associated w/ network interface card (NIC)
|
||||||
|
- 00-50-56-C0-00-01
|
||||||
|
- IP addresses for the network layer
|
||||||
|
- IPv4 (32 bit) vs IPv6 (128 bit)
|
||||||
|
- 128.1.1.3 vs fe80::fc38:6673:f04d:b37b%4
|
||||||
|
- IP addresses + ports for the transport layer
|
||||||
|
- E.g., 10.0.0.2:8080
|
||||||
|
- Domain names for the application/human layer
|
||||||
|
- E.g., www.wustl.edu
|
||||||
|
|
||||||
|
#### Routing and Translation of Addresses
|
||||||
|
|
||||||
|
(All of them are attack surfaces)
|
||||||
|
|
||||||
|
- Translation between IP addresses and MAC addresses
|
||||||
|
- Address Resolution Protocol (ARP) for IPv4
|
||||||
|
- Neighbor Discovery Protocol (NDP) for IPv6
|
||||||
|
- Routing with IP addresses
|
||||||
|
- TCP, UDP for connections, IP for routing packets
|
||||||
|
- Border Gateway Protocol for routing table updates
|
||||||
|
- Translation between IP addresses and domain names
|
||||||
|
- Domain Name System (DNS)
|
||||||
|
|
||||||
|
### Summary for security
|
||||||
|
|
||||||
|
- Confidentiality
|
||||||
|
- Packet sniffing
|
||||||
|
- Integrity
|
||||||
|
- ARP poisoning
|
||||||
|
- Availability
|
||||||
|
- Denial of service attacks
|
||||||
|
- Common
|
||||||
|
- Address translation poisoning attacks (DNS, ARP)
|
||||||
|
- Packet spoofing
|
||||||
|
- Core protocols not designed for security
|
||||||
|
- Eavesdropping, packet injection, route stealing, DNS poisoning
|
||||||
|
- Patched over time to prevent basic attacks
|
||||||
|
- More secure variants exist:
|
||||||
|
- IP $\to$ IPsec (IPsec is )
|
||||||
|
- DNS $\to$ DNSsec
|
||||||
|
- BGP $\to$ sBGP
|
||||||
|
|
||||||
|
## Crypto fundamentals
|
||||||
|
|
||||||
|
- Well-defined statement about difficulty of compromising a system
|
||||||
|
- ...with clear implicit or explicit assumptions about:
|
||||||
|
- Parameters of the system
|
||||||
|
- Threat model
|
||||||
|
- Attack surfaces
|
||||||
|
- Example: "A one-time pad cipher is secure against any cryptanalysis, including a brute-force attack, assuming:
|
||||||
|
- the key is the same length as the plaintext,
|
||||||
|
- the key is truly random, and
|
||||||
|
- the key is never re-used."
|
||||||
|
|
||||||
|
### Common roles in cryptography
|
||||||
|
|
||||||
|
Alice and Bob: Sender and receiver
|
||||||
|
|
||||||
|
Eve: Adversary that can see but not create any packets
|
||||||
|
|
||||||
|
Mallory: Man in the middle, can create and modify packets
|
||||||
|
|
||||||
|
The message M is called the **plaintext**.
|
||||||
|
|
||||||
|
Alice will convert plaintext M to an encrypted form using an
|
||||||
|
encryption algorithm E that outputs a **ciphertext** C for M.
|
||||||
|
|
||||||
|
#### Cryptography goals
|
||||||
|
|
||||||
|
Confidentiality:
|
||||||
|
|
||||||
|
- Mallory and Eve cannot recover original message from ciphertext
|
||||||
|
|
||||||
|
Integrity:
|
||||||
|
|
||||||
|
- Mallory cannot modify message from Alice to Bob without detection by Bob
|
||||||
|
|
||||||
|
#### Threat models
|
||||||
|
|
||||||
|
- Attacker may have (with increasing power):
|
||||||
|
- a) collection of ciphertexts (ciphertext-only attack)
|
||||||
|
- b) collection of plaintext/ciphertext pairs (known plaintext attack: KPA)
|
||||||
|
- c) collection of plaintext/ciphertext pairs for plaintexts selected by the attacker (chosen plaintext attack: CPA)
|
||||||
|
- d) collection of plaintext/ciphertext pairs for ciphertexts selected by the attacker (chosen ciphertext attack: CCA/CCA2)
|
||||||
|
|
||||||
|
### Symmetric key cryptography
|
||||||
|
|
||||||
|
#### Classical cryptography
|
||||||
|
|
||||||
|
Techniques: substitution and transposition
|
||||||
|
|
||||||
|
- Substitution: 1:1 mapping of alphabet onto itself
|
||||||
|
- Transposition: permutation of elements (i.e. rearrange letters)
|
||||||
|
|
||||||
|
- Caesar cipher: rotate each letter by k positions (k is fixed)
|
||||||
|
- Vigenère cipher: If length of key is known, split letters into groups based on index within key and do frequency analysis within groups
|
||||||
|
|
||||||
|
> The three steps in cryptography:
|
||||||
|
>
|
||||||
|
> - Precisely specify threat model
|
||||||
|
> - Propose a construction
|
||||||
|
> - Prove that breaking construction under threat mode will solve an underlying hard problem
|
||||||
|
|
||||||
|
#### Perfect secrecy
|
||||||
|
|
||||||
|
Ciphertext attack reveal no "info" about plaintext under ciphertext only attack
|
||||||
|
|
||||||
|
Def: A cipher $(E, D)$ over $(K, M, C)$ has perfect secrecy if
|
||||||
|
|
||||||
|
- $\forall m_0, m_1 \in M$ $(|m_0| = |m_1|)$ and $\forall c \in C$,
|
||||||
|
- $\Pr[E(k, m_0) = c] = \Pr[E(k, m_1) = c]$ where $k \leftarrow K$
|
||||||
|
|
||||||
|
#### XOR One-time pad (perfect secrecy)
|
||||||
|
|
||||||
|
Assumptions:
|
||||||
|
|
||||||
|
- Key is as long as message
|
||||||
|
- Key is random
|
||||||
|
- Key is never re-used
|
||||||
|
|
||||||
|
In practice, relax this assumption gets "Stream ciphers"
|
||||||
|
|
||||||
|
### Stream cipher
|
||||||
|
|
||||||
|
- Use pseudorandom generator as keystream for xore encryption (security is guaranteed by pseudorandom generator)
|
||||||
|
|
||||||
|
Security abstraction:
|
||||||
|
|
||||||
|
1. XOR transfers randomness of keystream to randomness of CT regardless of PT’s content
|
||||||
|
2. Security depends on G being "practically" indistinguishable from random string and "practically" unpredictable
|
||||||
|
3. Idea: shouldn’t be able to predict next bit of generator given all bits seen so far
|
||||||
|
|
||||||
|
#### Semantic security
|
||||||
|
|
||||||
|
- $(E, D)$ has semantic secrecy if $\forall m_0, m_1 \in M$ $(|m_0| = |m_1|)$,
|
||||||
|
- $\{E(k, m_0)\} \approx_p \{E(k, m_1)\}$ where $k \leftarrow K$
|
||||||
|
- ...and the adversary exhibits $m_0, m_1 \in M$ explicitly
|
||||||
|
|
||||||
|
The advantage of adversary is defined as the probability of distinguishing $E(k, m_0)$ from $E(k, m_1)$.
|
||||||
|
|
||||||
|
#### Weakness for stream ciphers
|
||||||
|
|
||||||
|
- Week pseudorandom generator
|
||||||
|
- Key re-use
|
||||||
|
- Predicable effect of modifying ciphertext or decrypted plaintext.
|
||||||
|
|
||||||
|
### Block cipher
|
||||||
|
|
||||||
|
View cipher as a Pseudo-Random Permutation (PRP)
|
||||||
|
|
||||||
|
#### Pseudorandom permutation
|
||||||
|
|
||||||
|
- PRP defined over $(K, X)$:
|
||||||
|
- $E: K \times X \to X$
|
||||||
|
- such that:
|
||||||
|
1. There exists an "efficient" deterministic algorithm to evaluate $E(k, x)$.
|
||||||
|
2. The function $E(k, \cdot)$ is one-to-one.
|
||||||
|
3. There exists an "efficient" inversion algorithm $D(k, y)$.
|
||||||
|
|
||||||
|
- i.e. a PRF that is an invertible one-to-one mapping from message space to message space
|
||||||
|
|
||||||
|
#### Security of block ciphers
|
||||||
|
|
||||||
|
Intuition: a PRP is secure if: a random function in $Perms[X]$ is indistinguishable from a random function in $SF$ (real random permutation function)
|
||||||
|
|
||||||
|
The adversarial game is to let adversary decide $x$, then we choose random key $k$ and give $E(k,x)$ and real random permutation $Perm(X)$ to let adversary decide which is which.
|
||||||
|
|
||||||
|
#### Block cipher constructions: Feistel network
|
||||||
|
|
||||||
|
Forward network:
|
||||||
|
|
||||||
|
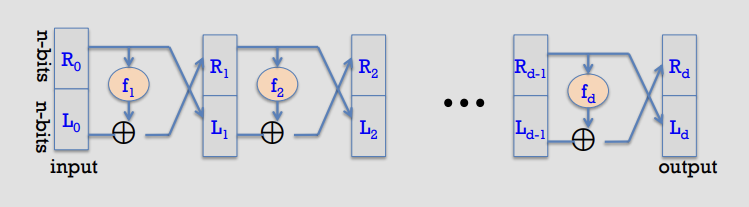
|
||||||
|
|
||||||
|
- Forward (round $i$): given $(L_{i-1}, R_{i-1}) \in \{0,1\}^n \times \{0,1\}^n$,
|
||||||
|
- $L_i = R_{i-1}$
|
||||||
|
- $R_i = L_{i-1} \oplus f_i(R_{i-1})$
|
||||||
|
|
||||||
|
- Proof (construct the inverse):
|
||||||
|
- Suppose we are given the output of round $i$, namely $(L_i, R_i)$.
|
||||||
|
- Recover the previous right half immediately:
|
||||||
|
- $R_{i-1} = L_i$
|
||||||
|
- Then recover the previous left half by undoing the XOR:
|
||||||
|
- $L_{i-1} = R_i \oplus f_i(R_{i-1}) = R_i \oplus f_i(L_i)$
|
||||||
|
- Therefore each round map is invertible, with inverse transformation:
|
||||||
|
- $R_{i-1} = L_i$
|
||||||
|
- $L_{i-1} = f_i(L_i) \oplus R_i$
|
||||||
|
- Applying this inverse for $i=d,d-1,\ldots,1$ recovers $(L_0,R_0)$ from $(L_d,R_d)$, so the whole Feistel network $F$ is invertible.
|
||||||
|
|
||||||
|
- Notation sketch (each wire is $n$ bits):
|
||||||
|
- Input: $(L_0, R_0)$
|
||||||
|
- Rounds:
|
||||||
|
- $L_1 = R_0,\ \ R_1 = L_0 \oplus f_1(R_0)$
|
||||||
|
- $L_2 = R_1,\ \ R_2 = L_1 \oplus f_2(R_1)$
|
||||||
|
- $\cdots$
|
||||||
|
- $L_d = R_{d-1},\ \ R_d = L_{d-1} \oplus f_d(R_{d-1})$
|
||||||
|
- Output: $(L_d, R_d)$
|
||||||
|
|
||||||
|
#### Block ciphers: block modes: ECB
|
||||||
|
|
||||||
|
New attacker model for multi-use keys (e.g. multiple blocks): CPA (Chosen Plaintext)-capable, not just CT-only
|
||||||
|
|
||||||
|
- Attacker sees many PT/CT pairs for same key
|
||||||
|
- Conservative model: attacker submits arbitrary PT (hence "C"PA)
|
||||||
|
- Cipher goal: maintain semantic security against CPA
|
||||||
|
|
||||||
|
#### CPA indistinguishability game
|
||||||
|
|
||||||
|
- Updated adversarial game for a CPA attacker:
|
||||||
|
- Let $E = (E, D)$ be a cipher defined over $(K, M, C)$. For $b \in \{0,1\}$ define $\operatorname{EXP}(b)$ as:
|
||||||
|
|
||||||
|
- Experiment $\operatorname{EXP}(b)$:
|
||||||
|
- Challenger samples $k \leftarrow K$.
|
||||||
|
- For each query $i = 1,\ldots,q$:
|
||||||
|
- Adversary outputs messages $m_{i,0}, m_{i,1} \in M$ such that $|m_{i,0}| = |m_{i,1}|$.
|
||||||
|
- Challenger returns $c_i \leftarrow E(k, m_{i,b})$.
|
||||||
|
|
||||||
|
- Encryption-oracle access (CPA):
|
||||||
|
- If the adversary wants $c = E(k, m)$, it queries with $m_{j,0} = m_{j,1} = m$ (so the response is $E(k,m)$ regardless of $b$).
|
||||||
|
|
||||||
|
#### Semantic security under CPA
|
||||||
|
|
||||||
|
- Def: $E$ is semantically secure under CPA if for all "efficient" adversaries $A$,
|
||||||
|
- $\operatorname{Adv}^{\operatorname{CPA}}[A,E] = \left|\Pr[\operatorname{EXP}(0)=1] - \Pr[\operatorname{EXP}(1)=1]\right|$
|
||||||
|
- is negligible.
|
||||||
|
|
||||||
|
### Summary for symmetric encrption
|
||||||
|
|
||||||
|
1. Stream ciphers
|
||||||
|
- Rely on secure PRG
|
||||||
|
- No key re-use
|
||||||
|
- Fast, low-mem, less robust
|
||||||
|
2. Block ciphers
|
||||||
|
- Rely on secure PRP
|
||||||
|
- Allow key re-use (usually only across blocks, not sessions)
|
||||||
|
- Provide authenticated encryption in some modes (e.g. GCM)
|
||||||
|
- Slower, higher-mem, more robust
|
||||||
|
- Used in practice for most crypto tasks (including secure network channels)
|
||||||
|
|
||||||
|
## Hash functions
|
||||||
|
|
||||||
|
### Hash function security properties
|
||||||
|
|
||||||
|
- Given a function $h:X \to Y$, we say that $h$ is:
|
||||||
|
|
||||||
|
- 1. Preimage resistant (one-way) if:
|
||||||
|
- given $y \in Y$ it is computationally infeasible to find a value $x \in X$ s.t. $h(x) = y$
|
||||||
|
|
||||||
|
- 2. 2nd preimage resistant (weak collision resistant) if:
|
||||||
|
- given a specific $x \in X$ it is computationally infeasible to find a value $x' \in X$ s.t. $x' \ne x$ and $h(x') = h(x)$
|
||||||
|
|
||||||
|
- 3. Collision resistant (strong collision resistant) if:
|
||||||
|
- it is computationally infeasible to find any two distinct values $x', x \in X$ s.t. $h(x') = h(x)$
|
||||||
|
|
||||||
|
### Collision resistance: adversarial definition
|
||||||
|
|
||||||
|
- Let $H: M \to T$ be a hash function ($|M| \gg |T|$).
|
||||||
|
- A function $H$ is collision resistant if for all (explicit) "efficient" algorithms $A$,
|
||||||
|
- $\operatorname{Adv}^{\operatorname{CR}}[A,H] = Pr[$A outputs a collision for $H$ $]$
|
||||||
|
- is negligible
|
||||||
|
|
||||||
|
### Hash function integrity applications
|
||||||
|
|
||||||
|
1. Delayed knowledge verification
|
||||||
|
2. Password storage
|
||||||
|
3. Trusted timestamping / blockchains
|
||||||
|
4. Integrity check on software
|
||||||
|
|
||||||
|
#### File integrity with secure read-only space
|
||||||
|
|
||||||
|
- When user downloads package, can verify that contents are valid
|
||||||
|
- $H$ collision resistant $\Rightarrow$ attacker cannot modify package without detection
|
||||||
|
- No encryption needed (public verifiability) if publisher has secure read-only space (e.g. trusted website, social media account)
|
||||||
|
|
||||||
|
#### Symmetric-crypto message authentication
|
||||||
|
|
||||||
|
- Context: Assume no secure RO space (insecure channel only)
|
||||||
|
- Need means of message authentication
|
||||||
|
- Idea: add tag to message
|
||||||
|
- System: Message Authentication Code (MAC)
|
||||||
|
- Def: a MAC $I=(S,V)$ defined over $(K,M,T)$ is a pair of algorithms:
|
||||||
|
- $S(k,m)$ outputs $t \in T$ // "Sign"
|
||||||
|
- $V(k,m,t)$ outputs `yes' or `no' // "Verify"
|
||||||
|
|
||||||
|
- Symmetric-crypto message authentication:
|
||||||
|
- Alice and Bob share secret key $k$
|
||||||
|
- Generate tag: $\text{tag} \leftarrow S(k,m)$
|
||||||
|
- Verify tag: $V(k,m,\text{tag}) = \texttt{yes}?$
|
||||||
|
|
||||||
|
#### MAC security model
|
||||||
|
|
||||||
|
- For a MAC $I=(S,V)$ and adversary $A$, define a MAC game as:
|
||||||
|
- Def: $I=(S,V)$ is a secure MAC if for all "efficient" $A$,
|
||||||
|
- $\operatorname{Adv}^{\operatorname{MAC}}[A,I] = \Pr[\text{Chal. outputs }1]$
|
||||||
|
- is negligible
|
||||||
|
|
||||||
|
- MAC game (sketch):
|
||||||
|
- Challenger samples $k \leftarrow K$
|
||||||
|
- Adversary makes queries $m_1,\ldots,m_q \in M$
|
||||||
|
- For each $i$, challenger returns $t_i \leftarrow S(k,m_i)$
|
||||||
|
- Adversary outputs a candidate forgery $(m,t)$
|
||||||
|
- Challenger outputs $b=1$ if:
|
||||||
|
- $V(k,m,t)=\texttt{yes}$ and
|
||||||
|
- $(m,t) \notin \{(m_1,t_1),\ldots,(m_q,t_q)\}$
|
||||||
|
- Otherwise challenger outputs $b=0$
|
||||||
|
|
||||||
|
- MAC security example: secure PRF not sufficient
|
||||||
|
- Suppose $F: K \times X \to Y$ is a secure PRF with $Y=\{0,1\}^{10}$.
|
||||||
|
- Is the derived MAC $I_F$ a secure MAC system?
|
||||||
|
- No: tags are too short, anyone can guess the tag for any message
|
||||||
|
|
||||||
|
#### MACs from PRFs: sufficient security condition
|
||||||
|
|
||||||
|
- Thm: If $F: K \times X \to Y$ is a secure PRF and $1/|Y|$ is negligible (i.e. $|Y|$ is large), then $I_F$ is a secure MAC.
|
||||||
|
- In particular, for every efficient MAC adversary $A$ attacking $I_F$, there exists an efficient PRF adversary $B$ attacking $F$ such that:
|
||||||
|
- $\operatorname{Adv}^{\operatorname{MAC}}[A, I_F] \le \operatorname{Adv}^{\operatorname{PRF}}[B, F] + 1/|Y|$
|
||||||
|
- Therefore $I_F$ is secure as long as $|Y|$ is large, e.g. $|Y| = 2^{80}$.
|
||||||
|
|
||||||
|
#### MACs from collision resistance
|
||||||
|
|
||||||
|
- Let $I=(S,V)$ be a MAC for short messages over $(K,M,T)$ (e.g. AES).
|
||||||
|
- Let $H: M_{\text{big}} \to M$.
|
||||||
|
- Def: $I_{\text{big}}=(S_{\text{big}},V_{\text{big}})$ over $(K,M_{\text{big}},T)$ as:
|
||||||
|
- $S_{\text{big}}(k,m) = S(k, H(m))$
|
||||||
|
- $V_{\text{big}}(k,m,t) = V(k, H(m), t)$
|
||||||
|
- Thm: If $I$ is a secure MAC and $H$ is collision resistant, then $I_{\text{big}}$ is a secure MAC.
|
||||||
|
- Example: $S(k,m) = \operatorname{AES2\text{-}block\text{-}cbc}(k, \operatorname{SHA\text{-}256}(m))$ is a secure MAC.
|
||||||
|
|
||||||
|
#### Using HMACs for confidentiality + integrity
|
||||||
|
|
||||||
|
- Confidentiality:
|
||||||
|
- Semantic security under a CPA
|
||||||
|
- Encryption secure against eavesdropping only
|
||||||
|
- Integrity:
|
||||||
|
- Existential unforgeability under a CPA
|
||||||
|
- CBC-MAC, HMAC
|
||||||
|
- Hash functions
|
||||||
|
- Confidentiality + integrity:
|
||||||
|
- CCA security
|
||||||
|
- Secure against tampering
|
||||||
|
- Method: Authenticated Encryption (AE)
|
||||||
|
- Encryption + MAC, in correct form
|
||||||
|
|
||||||
|
#### Authenticated Encryption: security defs
|
||||||
|
|
||||||
|
- An authenticated encryption system $(E,D)$ is a cipher where:
|
||||||
|
- $E: K \times M \times N \to C$
|
||||||
|
- $D: K \times C \times N \to M \cup$ cipher text rejected
|
||||||
|
- Security: the system must provide
|
||||||
|
- semantic security under a CPA attack, and
|
||||||
|
- ciphertext integrity: attacker cannot create new ciphertexts that decrypt properly
|
||||||
|
|
||||||
|
#### Ciphertext integrity
|
||||||
|
|
||||||
|
- Let $(E,D)$ be a cipher with message space $M$.
|
||||||
|
- Def: $(E,D)$ has ciphertext integrity if for all "efficient" $A$,
|
||||||
|
- $\operatorname{Adv}^{\operatorname{CI}}[A,E] = \Pr[\text{Chal. outputs }1]$
|
||||||
|
- is negligible
|
||||||
|
|
||||||
|
- Security model: ciphertext integrity (sketch):
|
||||||
|
- Challenger samples $k \leftarrow K$
|
||||||
|
- Adversary makes encryption queries $m_1,\ldots,m_q \in M$
|
||||||
|
- For each $i$, challenger returns $c_i \leftarrow E(k,m_i)$
|
||||||
|
- Adversary outputs a ciphertext $c$
|
||||||
|
- Challenger outputs $b=1$ if:
|
||||||
|
- $D(k,c) \ne \bot$ and
|
||||||
|
- $c \notin \{c_1,\ldots,c_q\}$
|
||||||
|
- Otherwise challenger outputs $b=0$
|
||||||
|
|
||||||
|
#### Authenticated encryption implies CCA security
|
||||||
|
|
||||||
|
- Thm: Let $(E,D)$ be a cipher that provides AE. Then $(E,D)$ is CCA secure.
|
||||||
|
- In particular, for any $q$-query efficient adversary $A$, there exist efficient $B_1,B_2$ such that:
|
||||||
|
- $\operatorname{Adv}^{\operatorname{CCA}}[A,E] \le 2q \cdot \operatorname{Adv}^{\operatorname{CI}}[B_1,E] + \operatorname{Adv}^{\operatorname{CPA}}[B_2,E]$
|
||||||
|
- Interpretation: CCA advantage is $\le O(\text{CT-integrity advantage}) + \text{CPA advantage}$.
|
||||||
|
|
||||||
|
- AE implication: authenticity
|
||||||
|
- Attacker cannot fool Bob into thinking a message was sent from Alice
|
||||||
|
- If attacker cannot create a valid ciphertext $c \notin \{c_1,\ldots,c_q\}$, then whenever $D(k,c) \ne \bot$ Bob knows the message is from someone who knows $k$ (but it could be a replay)
|
||||||
|
|
||||||
|
- DS construction example: signing a certificate
|
||||||
|
|
||||||
|
### Comparison: integrity/authentication approaches
|
||||||
|
|
||||||
|
- 1) Collision resistant hashing: need a read-only public space
|
||||||
|
- Allows public verification if the hash is published in a small read-only public space
|
||||||
|
- 2) MACs: must compute a new MAC for every client/user
|
||||||
|
- Must manage a long-term secret key per user to verify MACs (depending on application)
|
||||||
|
- Typically useful when one party signs, one verifies
|
||||||
|
- 3) Digital signatures: must manage a long-term secret key
|
||||||
|
- E.g. vendor's signature on software is shipped with software
|
||||||
|
- Allows software to be downloaded from an untrusted distribution site
|
||||||
|
- Public-key verification/rejection works, provided public key distribution is trustworthy
|
||||||
|
- Typically useful when one party signs, many verify
|
||||||
|
|
||||||
|
## Asymmetric key cryptography
|
||||||
|
|
||||||
|
### Asymmetric crypto overview
|
||||||
|
|
||||||
|
- Parties: sender, recipient, attacker (eavesdropping)
|
||||||
|
- Goal: sender encrypts a plaintext to a ciphertext using a public key; recipient decrypts using a private key.
|
||||||
|
|
||||||
|
#### Public-key encryption system
|
||||||
|
|
||||||
|
- Def: a public-key encryption system is a triple of algorithms $(G, E, D)$:
|
||||||
|
- $G()$: randomized algorithm that outputs a key pair $(pk, sk)$
|
||||||
|
- $E(pk, m)$: randomized algorithm that takes $m \in M$ and outputs $c \in C$
|
||||||
|
- $D(sk, c)$: deterministic algorithm that takes $c \in C$ and outputs $m \in M$ or $\bot$
|
||||||
|
- Consistency: for all $(pk, sk)$ output by $G$, for all $m \in M$,
|
||||||
|
- $D(sk, E(pk, m)) = m$
|
||||||
|
|
||||||
|
#### Trapdoor function
|
||||||
|
|
||||||
|
- Def: a trapdoor function $X \to Y$ is a triple of efficient algorithms $(G, F, F^{-1})$:
|
||||||
|
- $G()$: randomized algorithm that outputs a key pair $(pk, sk)$
|
||||||
|
- $F(pk, \cdot)$: deterministic algorithm that defines a function $X \to Y$
|
||||||
|
- $F^{-1}(sk, \cdot)$: defines a function $Y \to X$ that inverts $F(pk, \cdot)$
|
||||||
|
- More precisely: for all $(pk, sk)$ output by $G$, for all $x \in X$,
|
||||||
|
- $F^{-1}(sk, F(pk, x)) = x$
|
||||||
|
|
||||||
|
#### Symmetric vs. asymmetric security: attacker models
|
||||||
|
|
||||||
|
- Symmetric ciphers: two security notions for a passive attacker
|
||||||
|
- One-time security (stream ciphers: ciphertext-only)
|
||||||
|
- Many-time security (block ciphers: CPA)
|
||||||
|
- One-time security $\Rightarrow$ many-time security
|
||||||
|
- Example: ECB mode is one-time secure but not many-time secure
|
||||||
|
- Public-key encryption: single notion for a passive attacker
|
||||||
|
- Attacker can encrypt by themselves using the public key
|
||||||
|
- Therefore one-time security $\Rightarrow$ many-time security (CPA)
|
||||||
|
- Implication: public-key encryption must be randomized
|
||||||
|
- Analogous to secure block modes for block ciphers
|
||||||
|
|
||||||
|
### Semantic security of asymmetric crypto (IND-CPA)
|
||||||
|
|
||||||
|
#### IND-CPA game for public-key encryption
|
||||||
|
|
||||||
|
- For $b \in \{0,1\}$ define experiments $\operatorname{EXP}(0)$ and $\operatorname{EXP}(1)$:
|
||||||
|
|
||||||
|
- Experiment $\operatorname{EXP}(b)$:
|
||||||
|
- Challenger runs $(pk, sk) \leftarrow G()$
|
||||||
|
- Challenger sends $pk$ to adversary $A$
|
||||||
|
- Adversary outputs $m_0, m_1 \in M$ such that $|m_0| = |m_1|$
|
||||||
|
- Challenger returns $c \leftarrow E(pk, m_b)$
|
||||||
|
- Adversary outputs a bit $b' \in \{0,1\}$ (often modeled as outputting 1 if it "guesses $b=1$")
|
||||||
|
|
||||||
|
#### Semantic security (IND-CPA)
|
||||||
|
|
||||||
|
- Def: $E = (G, E, D)$ is semantically secure (a.k.a. IND-CPA) if for all efficient adversaries $A$,
|
||||||
|
- $\operatorname{Adv}^{\operatorname{SS}}[A, E] = \left|\Pr[\operatorname{EXP}(0)=1] - \Pr[\operatorname{EXP}(1)=1]\right|$
|
||||||
|
- is negligible
|
||||||
|
- Note: inherently multiple-round because the attacker can always encrypt on their own using $pk$ (CPA power is "built in").
|
||||||
|
|
||||||
|
### RSA cryptosystem: overview
|
||||||
|
|
||||||
|
- Setup:
|
||||||
|
- $n = pq$, with $p$ and $q$ primes
|
||||||
|
- Choose $e$ relatively prime to $\phi(n) = (p-1)(q-1)$
|
||||||
|
- Choose $d$ as the inverse of $e$ in $\mathbb{Z}_{\phi(n)}$
|
||||||
|
- Keys:
|
||||||
|
- Public key: $K_E = (n, e)$
|
||||||
|
- Private key: $K_D = d$
|
||||||
|
- Encryption:
|
||||||
|
- Plaintext $M \in \mathbb{Z}_n$
|
||||||
|
- $C = M^e \bmod n$
|
||||||
|
- Decryption:
|
||||||
|
- $M = C^d \bmod n$
|
||||||
|
|
||||||
|
- Example:
|
||||||
|
- Setup:
|
||||||
|
- $p = 7$, $q = 17$
|
||||||
|
- $n = 7 \cdot 17 = 119$
|
||||||
|
- $\phi(n) = 6 \cdot 16 = 96$
|
||||||
|
- $e = 5$
|
||||||
|
- $d = 77$
|
||||||
|
- Keys:
|
||||||
|
- public key: $(119, 5)$
|
||||||
|
- private key: $77$
|
||||||
|
- Encryption:
|
||||||
|
- $M = 19$
|
||||||
|
- $C = 19^5 \bmod 119 = 66$
|
||||||
|
- Decryption:
|
||||||
|
- $M = 66^{77} \bmod 119 = 19$
|
||||||
|
|
||||||
|
- Security intuition:
|
||||||
|
- To invert RSA without $d$, attacker must compute $x$ from $c = x^e \pmod n$.
|
||||||
|
- Best known approach:
|
||||||
|
- Step 1: factor $n$ (hard)
|
||||||
|
- Step 2: compute $e$-th roots modulo $p$ and $q$ (easy once factored)
|
||||||
|
- Notes (as commonly stated in lectures):
|
||||||
|
- 1024-bit RSA is within reach; 2048-bit is recommended usage
|
||||||
|
|
||||||
|
### Diffie-Hellman key exchange (informal)
|
||||||
|
|
||||||
|
- Fix a large prime $p$ (e.g., 2000 bits)
|
||||||
|
- Fix an integer $g \in \{1,\ldots,p\}$
|
||||||
|
|
||||||
|
- Protocol:
|
||||||
|
- Alice chooses random $a \in \{1,\ldots,p-1\}$ and sends $A = g^a \bmod p$
|
||||||
|
- Bob chooses random $b \in \{1,\ldots,p-1\}$ and sends $B = g^b \bmod p$
|
||||||
|
- Shared key:
|
||||||
|
- Alice computes $k_{AB} = B^a \bmod p = g^{ab} \bmod p$
|
||||||
|
- Bob computes $k_{AB} = A^b \bmod p = g^{ab} \bmod p$
|
||||||
|
|
||||||
|
- Hardness assumptions:
|
||||||
|
- Discrete log problem: given $p, g, y = g^x \bmod p$, find $x$
|
||||||
|
- Diffie-Hellman function: $\operatorname{DH}_g(g^a, g^b) = g^{ab} \bmod p$
|
||||||
|
|
||||||
|
#### Diffie-Hellman: security notes
|
||||||
|
|
||||||
|
- As described, the protocol is insecure against active attacks:
|
||||||
|
- A man-in-the-middle (MiTM) can insert themselves and create 2 separate secure sessions
|
||||||
|
- Fix idea: need a way to bind identity to a public key
|
||||||
|
- In practice: web of trust (e.g., GPG) or Public Key Infrastructure (PKI)
|
||||||
|
|
||||||
|
### Implementing trapdoor functions securely
|
||||||
|
|
||||||
|
- Never encrypt by applying $F$ directly to plaintext:
|
||||||
|
- Deterministic: cannot be semantically secure
|
||||||
|
- Many attacks exist for concrete TDFs
|
||||||
|
- Same plaintext blocks yield same ciphertext blocks
|
||||||
|
|
||||||
|
- Naive (insecure) sketch:
|
||||||
|
- $E(pk, m)$: output $c \leftarrow F(pk, m)$
|
||||||
|
- $D(sk, c)$: output $F^{-1}(sk, c)$
|
||||||
|
|
||||||
|
### Public-key encryption from TDFs
|
||||||
|
|
||||||
|
- Components:
|
||||||
|
- $(G, F, F^{-1})$: secure TDF $X \to Y$
|
||||||
|
- $(E_s, D_s)$: symmetric authenticated encryption over $(K, M, C)$
|
||||||
|
- $H: X \to K$: a hash function
|
||||||
|
|
||||||
|
- Construction of $(G, E, D)$ (with $G$ same as in the TDF):
|
||||||
|
- $E(pk, m)$:
|
||||||
|
- sample $x \leftarrow X$, compute $y \leftarrow F(pk, x)$
|
||||||
|
- derive $k \leftarrow H(x)$, compute $c \leftarrow E_s(k, m)$
|
||||||
|
- output $(y, c)$
|
||||||
|
- $D(sk, (y, c))$:
|
||||||
|
- compute $x \leftarrow F^{-1}(sk, y)$
|
||||||
|
- derive $k \leftarrow H(x)$, compute $m \leftarrow D_s(k, c)$
|
||||||
|
- output $m$
|
||||||
|
|
||||||
|
- Visual intuition:
|
||||||
|
- header: $y = F(pk, x)$
|
||||||
|
- body: $c = E_s(H(x), m)$
|
||||||
|
|
||||||
|
- Security theorem (lecture-style statement):
|
||||||
|
- If $(G, F, F^{-1})$ is a secure TDF, $(E_s, D_s)$ provides authenticated encryption, and $H$ is modeled as a random oracle, then $(G, E, D)$ is CCA-secure in the random oracle model (often denoted CCA-RO).
|
||||||
|
- Extension exists to reach full CCA (outside the RO idealization).
|
||||||
|
|
||||||
|
### Wrapup: symmetric vs. asymmetric systems
|
||||||
|
|
||||||
|
- Symmetric: faster, but key distribution is hard
|
||||||
|
- Asymmetric: slower, but key distribution/management is easier
|
||||||
|
- Application: secure web sessions (e.g., online shopping)
|
||||||
|
- Use symmetric-key encrypted sessions for bulk traffic
|
||||||
|
- Exchange symmetric keys using an asymmetric scheme
|
||||||
|
- Authenticate public keys (PKI or web of trust)
|
||||||
|
|
||||||
|
### Key exchange: summary
|
||||||
|
|
||||||
|
- Symmetric-key encryption challenges:
|
||||||
|
- Key storage: one per user pair, $O(n^2)$ total for $n$ users
|
||||||
|
- Key exchange: how to do it over a non-secure channel?
|
||||||
|
|
||||||
|
- Possible solutions:
|
||||||
|
|
||||||
|
- 1) Trusted Third Party (TTP)
|
||||||
|
- All users establish separate secret keys with the TTP
|
||||||
|
- TTP helps manage user-user keys (storage and secure channel)
|
||||||
|
- Applicability:
|
||||||
|
- Works for local domains
|
||||||
|
- Popular implementation: Kerberos for Single Sign On (SSO)
|
||||||
|
- Challenges:
|
||||||
|
- Scale: central authentication server is not suitable for the entire Internet
|
||||||
|
- Latency: requires online response from central server for every user-user session
|
||||||
|
|
||||||
|
- 2) Public/private keys with certificates
|
||||||
|
- All users have a single stable public key (helps with key storage and exchange)
|
||||||
|
- Users exchange per-session symmetric keys via a secure channel using public/private keys
|
||||||
|
- Trusting public keys: binding is validated by a third-party authority (Certificate Authority, CA)
|
||||||
|
- Why better than TTP? CAs can validate statically by issuing certificates, then be uninvolved
|
||||||
|
- CA/certificate process covered in a future lecture
|
||||||
|
|
||||||
|
## Appendix for additional algorithms and methods
|
||||||
|
|
||||||
|
### Feistel network (used by several items below)
|
||||||
|
|
||||||
|
A **Feistel network** splits a block into left/right halves and iterates rounds of the form $(L_{i+1},R_{i+1})=(R_i, L_i\oplus F(R_i,K_i))$, so decryption reuses the same structure with subkeys in reverse order.
|
||||||
|
|
||||||
|
Feistel-based here: **DES, 3DES, CAMELLIA, SEED, GOST 28147-89 (and thus GOST89MAC uses a Feistel block cipher internally).**
|
||||||
|
|
||||||
|
### Key exchange and authentication selectors (not symmetric encryption, not MAC)
|
||||||
|
|
||||||
|
These describe *how keys are negotiated- and/or *how the peer is authenticated*, not whether payload is a block/stream cipher.
|
||||||
|
|
||||||
|
#### RSA / DH / ECDH families
|
||||||
|
|
||||||
|
- **kRSA, RSA** — (key exchange) the premaster secret is sent encrypted under the server’s RSA public key (classic TLS RSA KX).
|
||||||
|
- **aRSA, aECDSA, aDSS, aGOST, aGOST01** — (authentication) the server identity is proven via a certificate signature scheme (RSA / ECDSA / DSA / GOST).
|
||||||
|
- **kDHr, kDHd, kDH** — (key exchange) *static- DH key agreement using DH certificates (obsolete/removed in newer OpenSSL).
|
||||||
|
- **kDHE, kEDH, DH / DHE, EDH / ECDHE, EECDH / kEECDH, kECDHE, ECDH** — (key exchange) *ephemeral- (EC)DH derives a fresh shared secret each handshake; "authenticated" variants bind it to a cert/signature.
|
||||||
|
- **aDH** — (authentication selector) indicates DH-authenticated suites (DH certs; also removed in newer OpenSSL).
|
||||||
|
|
||||||
|
#### PSK family
|
||||||
|
|
||||||
|
- **PSK** — (keying model) uses a pre-shared secret as the authentication/secret basis.
|
||||||
|
- **kPSK, kECDHEPSK, kDHEPSK, kRSAPSK** — (key exchange) PSK combined with (EC)DHE or RSA to derive/transport session keys.
|
||||||
|
- **aPSK** — (authentication) PSK itself authenticates endpoints (except RSA_PSK where cert auth may be involved).
|
||||||
|
|
||||||
|
---
|
||||||
|
|
||||||
|
### Symmetric encryption / AEAD (this is where "block vs stream" applies)
|
||||||
|
|
||||||
|
#### AES family
|
||||||
|
|
||||||
|
- **AES128 / AES256 / AES** — **encryption/decryption**; **block cipher**; core algorithm: AES is an SPN (substitution–permutation network) of repeated SubBytes/ShiftRows/MixColumns/AddRoundKey rounds.
|
||||||
|
- **AES-GCM** — **both encryption + message authentication (AEAD)**; **both** (AES block cipher used in counter mode + auth); core algorithm: encrypt with AES-CTR and authenticate with GHASH over ciphertext/AAD to produce a tag.
|
||||||
|
- **AES-ECB**: Functionality is encryption/decryption (confidentiality only) using a block cipher mode; core algorithm encrypts each 128-bit plaintext block independently under the same key, which deterministically leaks patterns because equal plaintext blocks map to equal ciphertext blocks.
|
||||||
|
- **AES-CBC**: Functionality is encryption/decryption (confidentiality only) using a block cipher mode; core algorithm XORs each plaintext block with the previous ciphertext block (starting from a fresh unpredictable IV) before AES-encrypting, which hides repetitions but requires correct IV handling and padding for non-multiple-of-block messages.
|
||||||
|
- **AES-OFB** — **encryption**; both (stream-like); repeatedly AES-encrypts an internal state to generate a keystream and XORs it with plaintext, where the state evolves independently of the plaintext/ciphertext.
|
||||||
|
- **AESCCM / AESCCM8** — **both encryption + message authentication (AEAD)**; **both**; core algorithm: compute CBC-MAC then encrypt with CTR mode, with 16-byte vs 8-byte tag length variants.
|
||||||
|
|
||||||
|
#### ARIA family
|
||||||
|
|
||||||
|
- **ARIA128 / ARIA256 / ARIA** — **encryption/decryption**; **block cipher**; core algorithm: ARIA is an SPN-style block cipher with byte-wise substitutions and diffusion layers across rounds.
|
||||||
|
|
||||||
|
#### CAMELLIA family
|
||||||
|
|
||||||
|
- **CAMELLIA128 / CAMELLIA256 / CAMELLIA** — **encryption/decryption**; **block cipher**; core algorithm: Camellia is a **Feistel network** with round functions plus extra FL/FL$^{-1}$ layers for nonlinearity and diffusion. *(Feistel: yes)*
|
||||||
|
|
||||||
|
#### ChaCha20
|
||||||
|
|
||||||
|
- **CHACHA20** — **encryption/decryption**; **stream cipher**; core algorithm: ChaCha20 generates a keystream via repeated ARX (add-rotate-xor) quarter-rounds on a 512-bit state and XORs it with plaintext.
|
||||||
|
|
||||||
|
#### DES / 3DES
|
||||||
|
|
||||||
|
- **DES** — **encryption/decryption**; **block cipher**; core algorithm: DES is a 16-round **Feistel network** using expansion, S-boxes, and permutations. *(Feistel: yes)*
|
||||||
|
- **3DES** — **encryption/decryption**; **block cipher**; core algorithm: applies DES three times (EDE or EEE) to increase effective security while retaining the **Feistel** DES core. *(Feistel: yes)*
|
||||||
|
|
||||||
|
#### RC4
|
||||||
|
|
||||||
|
- **RC4** — **encryption/decryption**; **stream cipher**; core algorithm: maintains a 256-byte permutation and produces a keystream byte-by-byte that is XORed with plaintext.
|
||||||
|
|
||||||
|
#### RC2 / IDEA / SEED
|
||||||
|
|
||||||
|
- **RC2** — **encryption/decryption**; **block cipher**; core algorithm: mixes key-dependent operations (adds, XORs, rotates) across rounds with "mix" and "mash" steps (not Feistel).
|
||||||
|
- **IDEA** — **encryption/decryption**; **block cipher**; core algorithm: combines modular addition, modular multiplication, and XOR in a Lai–Massey-like structure to achieve diffusion/nonlinearity (not Feistel).
|
||||||
|
- **SEED** — **encryption/decryption**; **block cipher**; core algorithm: a 16-round **Feistel network** with nonlinear S-box-based round functions. *(Feistel: yes)*
|
||||||
|
|
||||||
|
---
|
||||||
|
|
||||||
|
### Hash / MAC / digest selectors (message authentication side)
|
||||||
|
|
||||||
|
These are not "ciphers" but are used for integrity/authentication (often as HMAC, PRF, signatures).
|
||||||
|
|
||||||
|
- **MD5** — **message authentication component** (typically via HMAC, historically); **cipher method: N/A**; core algorithm: iterated Merkle–Damgård hash compressing 512-bit blocks into a 128-bit digest (now considered broken for collision resistance).
|
||||||
|
- **SHA1, SHA** — **message authentication component** (typically HMAC-SHA1 historically); **N/A**; core algorithm: Merkle–Damgård hash producing 160-bit output via 80-step compression (collisions known).
|
||||||
|
- **SHA256 / SHA384** — **message authentication component** (HMAC / TLS PRF / signatures); **N/A**; core algorithm: SHA-2 family Merkle–Damgård hashes with different word sizes/output lengths (256-bit vs 384-bit).
|
||||||
|
- **GOST94** — **message authentication component** (HMAC based on GOST R 34.11-94); **N/A**; core algorithm: builds an HMAC tag by hashing inner/outer padded key with the message using the GOST hash.
|
||||||
|
- **GOST89MAC** — **message authentication**; **block-cipher-based MAC (so "block" internally)**; core algorithm: computes a MAC using the GOST 28147-89 block cipher in a MAC mode (cipher-based chaining). *(Feistel internally via GOST 28147-89)*
|
||||||
|
|
||||||
|
> Latest version of cheatsheet distilled from this note.
|
||||||
156
content/CSE4303/CSE4303_L14.md
Normal file
156
content/CSE4303/CSE4303_L14.md
Normal file
@@ -0,0 +1,156 @@
|
|||||||
|
# CSE4303 Introduction to Computer Security (Lecture 14)
|
||||||
|
|
||||||
|
## Cryptography applications
|
||||||
|
|
||||||
|
### Crypto summary
|
||||||
|
|
||||||
|
- Cryptographic goals
|
||||||
|
- Confidentiality
|
||||||
|
- Symmetric-key ciphers
|
||||||
|
- Block ciphers
|
||||||
|
- Stream ciphers
|
||||||
|
- Public-key ciphers
|
||||||
|
- Data integrity
|
||||||
|
- Arbitrary length hash functions
|
||||||
|
- Message Authentication Codes (MACs)
|
||||||
|
- Digital signatures
|
||||||
|
- Authentication
|
||||||
|
- Entity authentication
|
||||||
|
- Authentication primitives
|
||||||
|
- Message authentication
|
||||||
|
- MACs
|
||||||
|
- Digital signatures
|
||||||
|
- Non-repudiation
|
||||||
|
- Digital signatures
|
||||||
|
|
||||||
|
### Overview
|
||||||
|
|
||||||
|
- Digital certificates
|
||||||
|
- PKI
|
||||||
|
- Intentional MITMs
|
||||||
|
- Other uses
|
||||||
|
- Authentication (...of users, not data)
|
||||||
|
- SSH keys
|
||||||
|
- Time-based One-Time Password (TOTP)
|
||||||
|
- Ransomware
|
||||||
|
- Post-Quantum (PQ) crypto
|
||||||
|
- Zero-Knowledge (ZK) proofs
|
||||||
|
- Homomorphic encryption
|
||||||
|
|
||||||
|
### Recall: key-exchange challenge
|
||||||
|
|
||||||
|
- No matter the cipher, **algorithm** is known but **key** must remain secret
|
||||||
|
- (Security principle: open design)
|
||||||
|
- Symmetric-key system: entire key remains secret
|
||||||
|
- Public-key scheme: private keys remain secret
|
||||||
|
- Q: before secure channel established, how to **reliably exchange** symmetric keys? How to reliably exchange public keys?
|
||||||
|
- Symmetric keys: via public/private keys
|
||||||
|
- Public keys: web of trust (e.g. GPG), what else?
|
||||||
|
|
||||||
|
As presented, the protocol is insecure against active attacks
|
||||||
|
|
||||||
|
MiTM can insert and create 2 separate secure sessions
|
||||||
|
|
||||||
|
### Public-key distribution: digital certificates
|
||||||
|
|
||||||
|
- Common public-key object
|
||||||
|
- Goal: bind identity to public key
|
||||||
|
- Contents:
|
||||||
|
- ID/key tuple
|
||||||
|
- Digital signature of some trusted signing authority: provides integrity/authenticity "guarantees" (under proper assumptions)
|
||||||
|
- Implementation:
|
||||||
|
- Can be chained: e.g. certificate for key of interest signed by Certificate Authority $CA_N$, cert for $CA_N$'s key signed by $CA_{N-1}$, ..., certificate for $CA_2$'s key signed by $CA_1$ (root CA), root CA's key pre-loaded in OS
|
||||||
|
- Allows for a hierarchy
|
||||||
|
- Requires entity to gain trust of signing authority and obtain certificate
|
||||||
|
|
||||||
|
### Defeating MITM using Digital Certificates
|
||||||
|
|
||||||
|
- Alice goes to a **trusted party** to get a certificate.
|
||||||
|
- After verifying Alice's identity, the trusted party issues a certificate **signed by them** with Alice's name and her public key.
|
||||||
|
- Alice sends the entire certificate to Bob.
|
||||||
|
- Bob verifies the certificate using the trusted party's public key (i.e. he checks the **signature** on the cert).
|
||||||
|
- Bob now knows the **true owner** of a public key.
|
||||||
|
|
||||||
|
### Public key infrastructure
|
||||||
|
|
||||||
|
- Certificate Authority (CA): a trusted party responsible for verifying the identity of users and binding the verified identity to public keys by issuing signed certificates to them
|
||||||
|
- Digital Certificate: a document certifying that the public key included inside does belong to the identity described in the document (signed by CA)
|
||||||
|
- Standard governing certs: X.509
|
||||||
|
|
||||||
|
### HTTPS layers of trust
|
||||||
|
|
||||||
|
- Data
|
||||||
|
- Trust data b/c it's encrypted by session key
|
||||||
|
- Session Key
|
||||||
|
- Trust session key b/c it was exchanged via public-key scheme
|
||||||
|
- Public Key
|
||||||
|
- Trust public key b/c it's in a certificate
|
||||||
|
- Certificate
|
||||||
|
- Trust certificate b/c it's signed by chain of CAs, ending with root CA
|
||||||
|
- Certificate Authorities
|
||||||
|
- Trust root CA's sig b/c it's embedded in browser/OS
|
||||||
|
- Browser/OS ...
|
||||||
|
- Trust browser/OS b/c
|
||||||
|
- we trust whoever installed the browser/OS
|
||||||
|
- and we trust the hardware that runs the OS
|
||||||
|
- (note: mechanisms for justifying these trusts exist too)
|
||||||
|
- Hardware
|
||||||
|
|
||||||
|
#### Application: PKI for public-key distribution
|
||||||
|
|
||||||
|
- Q: How are encrypted communications usually sent across a network? (e.g. https traffic)
|
||||||
|
- A: Multi-part strategy
|
||||||
|
- 1. Use symmetric-key cipher for encrypting traffic (speed advantage)
|
||||||
|
- 2. Use public-key cipher for exchanging symmetric key values (authenticity, consistency)
|
||||||
|
- 3. Use public-key infrastructure (PKI) to certify public keys (using certificates)
|
||||||
|
- Full details and data traces: First Few Milliseconds of a TLS 1.2 Connection (2017)
|
||||||
|
- [demo: ciphers currently used to encrypt session in Firefox, Chrome]
|
||||||
|
- [demo: root CAs currently trusted]
|
||||||
|
- How to mitigate attacks?
|
||||||
|
- Revocation cert
|
||||||
|
- Real attacks
|
||||||
|
- DigiNotar attacked 2011: issued fraudulent certs for, e.g., google.com
|
||||||
|
- WoSign 2016: issued certs to domains rather than subdomains
|
||||||
|
|
||||||
|
#### Legitimate (?) MITMs in PKI: private root certs
|
||||||
|
|
||||||
|
- Recent trend: entity (company/ISP/govt) installs root cert on user's system (as requirement for access), and possibly accompanying app
|
||||||
|
- Entity intercepts all secure sessions from user and MITMs them using root cert
|
||||||
|
- Entity then has access to all user's traffic
|
||||||
|
- Possibly legitimate uses:
|
||||||
|
- Enforce web usage policies: e.g. no gaming/social networking during work
|
||||||
|
- Enhance security: scan traffic for malware, phishing, etc. and respond
|
||||||
|
- Possibly illegitimate uses:
|
||||||
|
- Record user's traffic, browsing habits, personal data
|
||||||
|
- Sell data to third party
|
||||||
|
- Censor content
|
||||||
|
- More info:
|
||||||
|
- How to tell whether your https session is being MITM'ed
|
||||||
|
- Certificate hash lookup page
|
||||||
|
- Kazakhstan's ongoing MITM saga
|
||||||
|
|
||||||
|
#### Related privacy question: visibility
|
||||||
|
|
||||||
|
- Question: should govt agencies (including law enforcement) have access to encrypted communications?
|
||||||
|
- One "yes" argument: helps catch criminals, prevent terrorist attacks, etc.
|
||||||
|
- One "no" argument: invades privacy, gives too much eavesdropping power
|
||||||
|
- Relevant history / case studies:
|
||||||
|
- Munitions restrictions on crypto circa late 1990's: DES
|
||||||
|
- Phil Zimmerman and PGP: e-mail encryption, govt attempts to suppress
|
||||||
|
- Edward Snowden revelations 2013: fears of privacy abuse are well-founded
|
||||||
|
- RSA Sec's use of NIST-recommended PRNG w/ECC: was apparently an NSA backdoor
|
||||||
|
- Syed Farook ("San Bernardino shooter") case 2015: FBI pressure on Apple to unlock user's iPhone
|
||||||
|
- Apple resisted
|
||||||
|
- Never resolved legally: FBI found 3rd party to grant access
|
||||||
|
- GCHQ "ghost protocol" proposal 2018
|
||||||
|
- Don't weaken encryption, but secretly add government to encrypted conversation at will
|
||||||
|
- Add extra private key to encrypted convos; suppress notifications about new user being added to convo
|
||||||
|
- Condemned by big tech companies June 2019
|
||||||
|
- Question: should private companies have access to encrypted communications, or just metadata, or neither?
|
||||||
|
- Relevant history / case studies:
|
||||||
|
- Zoom end-to-end encryption [Dec 2022 status]
|
||||||
|
- Note: without E2EE, Zoom holds keys but never decrypts conversations
|
||||||
|
- Facebook/WhatsApp terms of service update 2021 [Wired mag article]
|
||||||
|
- Note: WhatsApp still has E2EE for messages, but shares metadata
|
||||||
|
|
||||||
|
|
||||||
72
content/CSE4303/CSE4303_L15.md
Normal file
72
content/CSE4303/CSE4303_L15.md
Normal file
@@ -0,0 +1,72 @@
|
|||||||
|
# CSE4303 Introduction to Computer Security (Lecture 15)
|
||||||
|
|
||||||
|
## Cryptography applications
|
||||||
|
|
||||||
|
### Authentication (...of users, not data)
|
||||||
|
|
||||||
|
- Traditional authentication: password-based, single-factor
|
||||||
|
- Disadvantage: convenience often chosen over security
|
||||||
|
- Weak passwords
|
||||||
|
- Password re-use: one password compromised ==> many accounts compromised
|
||||||
|
- Attack: "credential stuffing" (testing single stolen password against many accounts)
|
||||||
|
|
||||||
|
#### SSH keys
|
||||||
|
|
||||||
|
- Idea: relieve burden of secure passwords
|
||||||
|
- Use public/private-key auth instead (can be automated!)
|
||||||
|
- Use secure password once to exchange public key
|
||||||
|
- Protocol: challenge/response to verify possession of keys
|
||||||
|
|
||||||
|
#### Case Study: SSH
|
||||||
|
|
||||||
|
- SSH can use public-key based authentication to authenticate users
|
||||||
|
- Generate a pair of public and private keys: `ssh-keygen -t rsa`
|
||||||
|
- private key: `/home/seed/.ssh/id_rsa`
|
||||||
|
- public key: `/home/seed/.ssh/id_rsa.pub`
|
||||||
|
- Register public key with server:
|
||||||
|
- Send the public key file to the remote server using a secure channel
|
||||||
|
- Add public key to the authorization file `~/.ssh/authorized_keys`
|
||||||
|
- Server can use key to authenticate clients
|
||||||
|
|
||||||
|
#### Time-based One-Time Password (TOTP)
|
||||||
|
|
||||||
|
- Goal: provide secure 2nd factor for authentication
|
||||||
|
- Idea:
|
||||||
|
- Generate one-time (single-use) password for each login attempt
|
||||||
|
- Compute one-time password using secure HMAC with current time as a parameter
|
||||||
|
- Key used for HMAC: exchanged once at setup
|
||||||
|
- Protocol: open standard published by OATH, IETF
|
||||||
|
- HMAC-based One-Time Password (HOTP)
|
||||||
|
- e.g. $TOTP(k) = HOTP(k, C_t)$, where $C_t$ is absolute measure of current time interval
|
||||||
|
- Num digits taken from output: 6 to 10
|
||||||
|
|
||||||
|
### Ransomware
|
||||||
|
|
||||||
|
- Idea: attacker encrypts victim's data with symmetric cipher, requires ransom payment to decrypt (or provide key)
|
||||||
|
- System model: any data store (company database, municipal database, user's hard drive, etc.)
|
||||||
|
- Threat model: attacker who has already compromised victim's system
|
||||||
|
- Vuln: lack of backups (or prohibitive time to restore); whatever vuln allowed attacker into system
|
||||||
|
- Surface: exposed data, and surface of original compromise
|
||||||
|
- Vector: encrypt data store and erase or replace original data store
|
||||||
|
- Mitigation/defense: keep up-to-date backups (possibly "air-gapped") in separate location; practice restoring from backups
|
||||||
|
- Enabler: anonymity of Bitcoin payments
|
||||||
|
- Recent-ish examples:
|
||||||
|
- Baltimore 2019 (didn't pay, est. $18 million to fix)
|
||||||
|
- Atlanta 2018 (~$9 million to fix)
|
||||||
|
- Lake City & Riviera City, Florida 2019 (did pay, $500,000+ apiece)
|
||||||
|
- Many others since these
|
||||||
|
- One of the top projected trends in cybersecurity in 2021 (e.g. by CSO online)
|
||||||
|
|
||||||
|
### Post-Quantum (PQ) crypto
|
||||||
|
|
||||||
|
- Fundamentally different computation paradigm than "classical" von Neumann or dataflow models
|
||||||
|
- Relies on properties of quantum physics to solve problems efficiently
|
||||||
|
- Superposition: state of quantum bit ("qubit") expressed by probability model over continuous range of values (vs. classic bit: 0 or 1 only)
|
||||||
|
- Like being able to operate on all possible bit combos of a register simultaneously, instead of operating on only one among all possibilities
|
||||||
|
- Entanglement: operating on one qubit affects others
|
||||||
|
|
||||||
|
|
||||||
|
|
||||||
|
### Zero-Knowledge (ZK) proofs
|
||||||
|
|
||||||
|
### Homomorphic encryption
|
||||||
160
content/CSE4303/CSE4303_L16.md
Normal file
160
content/CSE4303/CSE4303_L16.md
Normal file
@@ -0,0 +1,160 @@
|
|||||||
|
# CSE4303 Introduction to Computer Security (Lecture 16)
|
||||||
|
|
||||||
|
## System security
|
||||||
|
|
||||||
|
- Why system security / platform security?
|
||||||
|
- All code runs on some physical machine!
|
||||||
|
- The cloud is not a cloud
|
||||||
|
- Web pages are just data and code copied from a server that also manages the transfer
|
||||||
|
- Why Linux?
|
||||||
|
- Majority of web servers run Linux (esp. Cloud); popular in embedded, mobile devices
|
||||||
|
|
||||||
|
### Operating system background
|
||||||
|
|
||||||
|
Context: computing stack
|
||||||
|
|
||||||
|
| Layer | Description |
|
||||||
|
| --- | --- |
|
||||||
|
| Application | Web browser, user apps, DNS |
|
||||||
|
| OS:libs | Memory allocations, compiler/linker|
|
||||||
|
| OS:kernel | Process control, networking, file system, access control|
|
||||||
|
| OS:drivers | Manage hardware|
|
||||||
|
| (Firmware) | Minimal hardware management (if no full OS)|
|
||||||
|
|Hardware | Processor, cahce, RAM, disk, USB ports|
|
||||||
|
|
||||||
|
#### Operating systems
|
||||||
|
|
||||||
|
- Operating System:
|
||||||
|
- Provides easier to use and high level **abstractions** for resources such as address space for memory and files for disk blocks.
|
||||||
|
- Provides **controlled access** to hardware resources.
|
||||||
|
- Provides **isolation** between different processes and between the processes running untrusted/application code and the trusted operating system.
|
||||||
|
|
||||||
|
- Need for trusting an operating system
|
||||||
|
- Why do we need to trust the operating system? (AKA a Trusted Computing Base or TCB)
|
||||||
|
- What requirements must it meet to be trusted?
|
||||||
|
|
||||||
|
- TCB Requirements:
|
||||||
|
- 1. Tamper-proof
|
||||||
|
- 2. Complete mediation (reference monitor)
|
||||||
|
- 3. Correct
|
||||||
|
|
||||||
|
Isolating OS from Untrusted User Code
|
||||||
|
|
||||||
|
- How do we meet the first requirement of a TCB (e.g., isolation or tamper-proofness)?
|
||||||
|
- Hardware support for memory protection
|
||||||
|
- Processor execution modes (system AND user modes, execution rings)
|
||||||
|
- Privileged instructions which can only be executed in system mode
|
||||||
|
- System calls used to transfer control between user and system code
|
||||||
|
|
||||||
|
|
||||||
|
System Calls: Going from User to OS Code
|
||||||
|
|
||||||
|
- System calls used to transfer control between user and system code
|
||||||
|
- Such calls come through "call gates" and return back to user code.
|
||||||
|
- The processor execution mode or privilege ring changes when call and return happen.
|
||||||
|
- x86 `sysenter` / `sysexit` instructions
|
||||||
|
|
||||||
|
Isolating User Processes from Each Other
|
||||||
|
|
||||||
|
- How do we meet the user/user isolation and separation?
|
||||||
|
- OS uses hardware support for memory protection to ensure this.
|
||||||
|
|
||||||
|
Virtualization
|
||||||
|
|
||||||
|
- OS is large and complex, even different operating systems may be desired by different customers
|
||||||
|
- Compromise of an OS impacts all applications
|
||||||
|
|
||||||
|
Complete Mediation: The TCB
|
||||||
|
|
||||||
|
- Make sure that no protected resource (e.g., memory page or file) could be accessed without going through the TCB
|
||||||
|
- TCB acts as a reference monitor that cannot be bypassed
|
||||||
|
- Privileged instructions
|
||||||
|
|
||||||
|
Limiting the Damage oa a Hacked OS
|
||||||
|
|
||||||
|
Use: Hypervisor, virtual machines, guest OS and applications
|
||||||
|
|
||||||
|
Compromise of OS in VM1 only impacts applications running on VM1
|
||||||
|
|
||||||
|
### Secure boot and Root of Trust (RoT)
|
||||||
|
|
||||||
|
Goal: create chain of trust back to hardware-stored cryptographic keys
|
||||||
|
|
||||||
|
#### Secure enclave: overview (Intel SGX)
|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|
Goal: keep sensitive data within hardware-isolated encrypted environment
|
||||||
|
|
||||||
|
### Access control
|
||||||
|
|
||||||
|
Controlling Accesses to Resources
|
||||||
|
|
||||||
|
- TCB (reference monitor) sees a request for a resource, how does it decide whether it should be granted?
|
||||||
|
- Example: Should John's process making a request to read a certain file be allowed to do so?
|
||||||
|
|
||||||
|
- Authentication establishes the source of a request (e.g., John's UID)
|
||||||
|
- Authorization (or access control) answers the question if a certain source of a request (User ID) is allowed to read the file
|
||||||
|
- Subject who owns a resource (creates it) should be able to control access to it (sometimes this is not true)
|
||||||
|
|
||||||
|
- Access control
|
||||||
|
- Basically, it is about who is allowed to access what.
|
||||||
|
- Two parts
|
||||||
|
- Part I - Policy: decide who should have access to certain resources (access control policy)
|
||||||
|
- Part II - Enforcement: only accesses defined by the access control policy are granted.
|
||||||
|
- Complete mediation is essential for successful enforcement
|
||||||
|
|
||||||
|
Discretionary Access Control
|
||||||
|
|
||||||
|
- In discretionary access control (DAC), owner of a resource decides how it can be shared
|
||||||
|
- Owner can choose to give read or write access to other users
|
||||||
|
- Two problems with DAC:
|
||||||
|
- You cannot control if someone you share a file with will not further share the data contained in it
|
||||||
|
- Cannot control "information flow"
|
||||||
|
- In many organizations, a user does not get to decide how certain type of data can be shared
|
||||||
|
- Typically the employer may mandate how to share various types of sensitive data
|
||||||
|
- Mandatory Access Control (MAC) helps address these problems
|
||||||
|
|
||||||
|
Mandatory Access Control (MAC) Models
|
||||||
|
|
||||||
|
- User works in a company and the company decides how data should be shared
|
||||||
|
- Hospital owns patient records and limits their sharing
|
||||||
|
- Regulatory requirements may limit sharing
|
||||||
|
- HIPAA for health information
|
||||||
|
|
||||||
|
#### Example: Linux system controls
|
||||||
|
|
||||||
|
Unix file access control list
|
||||||
|
|
||||||
|
- Each file has owner and group
|
||||||
|
- Permissions set by owner
|
||||||
|
- Read, write, execute
|
||||||
|
- Owner, group, other
|
||||||
|
- Represented by vector of four octal values
|
||||||
|
- Only owner, root can change permissions
|
||||||
|
- This privilege cannot be delegated or shared
|
||||||
|
- Setid bits -- Discuss in a few slides
|
||||||
|
|
||||||
|
Process effective user id (EUID)
|
||||||
|
|
||||||
|
- Each process has three IDs (+ more under Linux)
|
||||||
|
- Real user ID (RUID)
|
||||||
|
- Same as the user ID of parent (unless changed)
|
||||||
|
- Used to determine which user started the process
|
||||||
|
- Effective user ID (EUID)
|
||||||
|
- From set user ID bit on the file being executed, or sys call
|
||||||
|
- Determines the permissions for process
|
||||||
|
- File access and port binding
|
||||||
|
- Saved user ID (SUID)
|
||||||
|
- So previous EUID can be restored
|
||||||
|
- Real group ID, effective group ID used similarly
|
||||||
|
|
||||||
|
#### Weaknesses in Unix isolation, privileges
|
||||||
|
|
||||||
|
- Shared resources
|
||||||
|
- Since any process can create files in `/tmp` directory, an untrusted process may create files that are used by arbitrary system processes
|
||||||
|
- Time-of-Check-to-Time-of-Use (TOCTTOU), i.e. race conditions
|
||||||
|
- Typically, a root process uses system call to determine if initiating user has permission to a particular file, e.g. `/tmp/X`.
|
||||||
|
- After access is authorized and before the file open, user may change the file `/tmp/X` to a symbolic link to a target file `/etc/shadow`.
|
||||||
|
|
||||||
|
### Hazard: race conditions
|
||||||
@@ -3,6 +3,7 @@ export default {
|
|||||||
"---":{
|
"---":{
|
||||||
type: 'separator'
|
type: 'separator'
|
||||||
},
|
},
|
||||||
|
CSE4303_E1: "Exam review",
|
||||||
CSE4303_L1: "Introduction to Computer Security (Lecture 1)",
|
CSE4303_L1: "Introduction to Computer Security (Lecture 1)",
|
||||||
CSE4303_L2: "Introduction to Computer Security (Lecture 2)",
|
CSE4303_L2: "Introduction to Computer Security (Lecture 2)",
|
||||||
CSE4303_L3: "Introduction to Computer Security (Lecture 3)",
|
CSE4303_L3: "Introduction to Computer Security (Lecture 3)",
|
||||||
@@ -17,4 +18,7 @@ export default {
|
|||||||
CSE4303_L11: "Introduction to Computer Security (Lecture 11)",
|
CSE4303_L11: "Introduction to Computer Security (Lecture 11)",
|
||||||
CSE4303_L12: "Introduction to Computer Security (Lecture 12)",
|
CSE4303_L12: "Introduction to Computer Security (Lecture 12)",
|
||||||
CSE4303_L13: "Introduction to Computer Security (Lecture 13)",
|
CSE4303_L13: "Introduction to Computer Security (Lecture 13)",
|
||||||
|
CSE4303_L14: "Introduction to Computer Security (Lecture 14)",
|
||||||
|
CSE4303_L15: "Introduction to Computer Security (Lecture 15)",
|
||||||
|
CSE4303_L16: "Introduction to Computer Security (Lecture 16)"
|
||||||
}
|
}
|
||||||
|
|||||||
@@ -78,6 +78,27 @@ An $m$-dimensional **manifold** is a topological space $X$ that is
|
|||||||
2. Second countable: With a countable basis
|
2. Second countable: With a countable basis
|
||||||
3. Local euclidean: Each point of $x$ of $X$ has a neighborhood that is homeomorphic to an open subset of $\mathbb{R}^m$.
|
3. Local euclidean: Each point of $x$ of $X$ has a neighborhood that is homeomorphic to an open subset of $\mathbb{R}^m$.
|
||||||
|
|
||||||
|
<details>
|
||||||
|
<summary>Example of space that is not a manifold but satisfies part of the definition</summary>
|
||||||
|
|
||||||
|
Non-hausdorff:
|
||||||
|
|
||||||
|
Consider the set with two origin $\mathbb{R}\setminus\{0\}$. with $\{p,q\}$, and the topology defined over all the open intervals that don't contain the origin, with set of the form $(-a,0)\cup \{p\}\cup (0,a)$ for $a\in \mathbb{R}$ and $(-a,0)\cup \{q\}\cup (0,a)$.
|
||||||
|
|
||||||
|
---
|
||||||
|
|
||||||
|
Non-second-countable:
|
||||||
|
|
||||||
|
Consider the long line $\mathbb{R}\times [0,1)$
|
||||||
|
|
||||||
|
---
|
||||||
|
|
||||||
|
Non-local-euclidean:
|
||||||
|
|
||||||
|
Any 1-dimensional CW complex (graph) that has a vertex with 3 or more edges connected to it will be Hausdorff and second-countable, but not locally Euclidean at those vertices.
|
||||||
|
|
||||||
|
</details>
|
||||||
|
|
||||||
#### Whitney's Embedding Theorem
|
#### Whitney's Embedding Theorem
|
||||||
|
|
||||||
If $X$ is a compact $m$-manifold, then $X$ can be imbedded in $\mathbb{R}^N$ for some positive integer $N$.
|
If $X$ is a compact $m$-manifold, then $X$ can be imbedded in $\mathbb{R}^N$ for some positive integer $N$.
|
||||||
@@ -97,6 +118,12 @@ Let $\{U_i\}_{i=1}^n$ be a finite open cover of a normal space $X$ (Every pair o
|
|||||||
|
|
||||||
Then there exists a partition of unity dominated by $\{U_i\}_{i=1}^n$.
|
Then there exists a partition of unity dominated by $\{U_i\}_{i=1}^n$.
|
||||||
|
|
||||||
|
#### Definition of paracompact space
|
||||||
|
|
||||||
|
Locally finite: $\forall x\in X$, $\exists$ open $x\in U$ such that $U$ only intersects finitely many open sets in $\mathcal{B}$.
|
||||||
|
|
||||||
|
A space $X$ is paracompact if every open cover $A$ of $X$ has a **locally finite** refinement $\mathcal{B}$ of $A$ that covers $X$.
|
||||||
|
|
||||||
### Homotopy
|
### Homotopy
|
||||||
|
|
||||||
#### Definition of homotopy equivalent spaces
|
#### Definition of homotopy equivalent spaces
|
||||||
@@ -128,7 +155,6 @@ Two pathes $f$ and $f'$ are path homotopic if
|
|||||||
|
|
||||||
The $\simeq$, $\simeq_p$ are both equivalence relations.
|
The $\simeq$, $\simeq_p$ are both equivalence relations.
|
||||||
|
|
||||||
|
|
||||||
#### Definition for product of paths
|
#### Definition for product of paths
|
||||||
|
|
||||||
Given $f$ a path in $X$ from $x_0$ to $x_1$ and $g$ a path in $X$ from $x_1$ to $x_2$.
|
Given $f$ a path in $X$ from $x_0$ to $x_1$ and $g$ a path in $X$ from $x_1$ to $x_2$.
|
||||||
@@ -137,9 +163,9 @@ Define the product $f*g$ of $f$ and $g$ to be the map $h:[0,1]\to X$.
|
|||||||
|
|
||||||
#### Definition for equivalent classes of paths
|
#### Definition for equivalent classes of paths
|
||||||
|
|
||||||
$\Pi_1(X,x)$ is the equivalent classes of paths starting and ending at $x$.
|
$pi_1(X,x)$ is the equivalent classes of paths starting and ending at $x$.
|
||||||
|
|
||||||
On $\Pi_1(X,x)$,, we define $\forall [f],[g],[f]*[g]=[f*g]$.
|
On $pi_1(X,x)$,, we define $\forall [f],[g],[f]*[g]=[f*g]$.
|
||||||
|
|
||||||
$$
|
$$
|
||||||
[f]\coloneqq \{f_i:[0,1]\to X|f_0(0)=f(0),f_i(1)=f(1)\}
|
[f]\coloneqq \{f_i:[0,1]\to X|f_0(0)=f(0),f_i(1)=f(1)\}
|
||||||
@@ -165,6 +191,12 @@ $$
|
|||||||
|
|
||||||
### Covering space
|
### Covering space
|
||||||
|
|
||||||
|
#### Definition of partition into slice
|
||||||
|
|
||||||
|
Let $p:E\to B$ be a continuous surjective map. The open set $U\subseteq B$ is said to be evenly covered by $p$ if it's inverse image $p^{-1}(U)$ can be written as the union of **disjoint open sets** $V_\alpha$ in $E$. Such that for each $\alpha$, the restriction of $p$ to $V_\alpha$ is a homeomorphism of $V_\alpha$ onto $U$.
|
||||||
|
|
||||||
|
The collection of $\{V_\alpha\}$ is called a **partition** $p^{-1}(U)$ into slice.
|
||||||
|
|
||||||
#### Definition of covering space
|
#### Definition of covering space
|
||||||
|
|
||||||
Let $p:E\to B$ be a continuous surjective map.
|
Let $p:E\to B$ be a continuous surjective map.
|
||||||
@@ -199,3 +231,7 @@ Recall from previous lecture, we have unique lift for covering map.
|
|||||||
Let $p: E\to B$ be a covering map, and $e_0\in E$ and $p(e_0)=b_0$. Any path $f:I\to B$ beginning at $b_0$, has a unique lifting to a path starting at $e_0$.
|
Let $p: E\to B$ be a covering map, and $e_0\in E$ and $p(e_0)=b_0$. Any path $f:I\to B$ beginning at $b_0$, has a unique lifting to a path starting at $e_0$.
|
||||||
|
|
||||||
Back to the circle example, it means that there exists a unique correspondence between a loop starting at $(1,0)$ in $S^1$ and a path in $\mathbb{R}$ starting at $0$, ending in $\mathbb{Z}$.
|
Back to the circle example, it means that there exists a unique correspondence between a loop starting at $(1,0)$ in $S^1$ and a path in $\mathbb{R}$ starting at $0$, ending in $\mathbb{Z}$.
|
||||||
|
|
||||||
|
#### Theorem for induced homotopy for fundamental groups
|
||||||
|
|
||||||
|
Suppose $f,g$ are two paths in $B$, and suppose $f$ and $g$ are path homotopy ($f(0)=g(0)=b_0$, and $f(1)=g(1)=b_1$, $b_0,b_1\in B$), then $\hat{f}:\pi_1(B,b_0)\to \pi_1(B,b_1)$ and $\hat{g}:\pi_1(B,b_0)\to \pi_1(B,b_1)$ are path homotopic.
|
||||||
@@ -88,12 +88,12 @@ $\bar{f}_t=\bar{f}(1-ts)$ $s\in[\frac{1}{2},1]$.
|
|||||||
|
|
||||||
> [!CAUTION]
|
> [!CAUTION]
|
||||||
>
|
>
|
||||||
> Homeomorphism does not implies homotopy automatically.
|
> Homeomorphism does not implies homotopy automatically. Homeomorphism doesn’t force a homotopy between that map and the identity (or between two given homeomorphisms).
|
||||||
|
|
||||||
#### Definition for the fundamental group
|
#### Definition for the fundamental group
|
||||||
|
|
||||||
The fundamental group of $X$ at $x$ is defined to be
|
The fundamental group of $X$ at $x$ is defined to be
|
||||||
|
|
||||||
$$
|
$$
|
||||||
(\Pi_1(X,x),*)
|
(pi_1(X,x),*)
|
||||||
$$
|
$$
|
||||||
@@ -8,9 +8,9 @@ The $*$ operation has the following properties:
|
|||||||
|
|
||||||
#### Properties for the path product operation
|
#### Properties for the path product operation
|
||||||
|
|
||||||
Let $[f],[g]\in \Pi_1(X)$, for $[f]\in \Pi_1(X)$, let $s:\Pi_1(X)\to X, [f]\mapsto f(0)$ and $t:\Pi_1(X)\to X, [f]\mapsto f(1)$.
|
Let $[f],[g]\in pi_1(X)$, for $[f]\in pi_1(X)$, let $s:pi_1(X)\to X, [f]\mapsto f(0)$ and $t:pi_1(X)\to X, [f]\mapsto f(1)$.
|
||||||
|
|
||||||
Note that $t([f])=s([g])$, $[f]*[g]=[f*g]\in \Pi_1(X)$.
|
Note that $t([f])=s([g])$, $[f]*[g]=[f*g]\in pi_1(X)$.
|
||||||
|
|
||||||
This also satisfies the associativity. $([f]*[g])*[h]=[f]*([g]*[h])$.
|
This also satisfies the associativity. $([f]*[g])*[h]=[f]*([g]*[h])$.
|
||||||
|
|
||||||
@@ -51,33 +51,33 @@ Let $x_0\in X$. A path starting and ending at $x_0$ is called a loop based at $x
|
|||||||
The fundamental group of $X$ at $x$ is defined to be
|
The fundamental group of $X$ at $x$ is defined to be
|
||||||
|
|
||||||
$$
|
$$
|
||||||
(\Pi_1(X,x),*)
|
(pi_1(X,x),*)
|
||||||
$$
|
$$
|
||||||
|
|
||||||
where $*$ is the product operation, and $\Pi_1(X,x)$ is the set o homotopy classes of loops in $X$ based at $x$.
|
where $*$ is the product operation, and $pi_1(X,x)$ is the set o homotopy classes of loops in $X$ based at $x$.
|
||||||
|
|
||||||
<details>
|
<details>
|
||||||
<summary>Example of fundamental group</summary>
|
<summary>Example of fundamental group</summary>
|
||||||
|
|
||||||
Consider $X=[0,1]$, with subspace topology from standard topology in $\mathbb{R}$.
|
Consider $X=[0,1]$, with subspace topology from standard topology in $\mathbb{R}$.
|
||||||
|
|
||||||
$\Pi_1(X,0)=\{e\}$, (constant function at $0$) since we can build homotopy for all loops based at $0$ as follows $H(s,t)=(1-t)f(s)+t$.
|
$pi_1(X,0)=\{e\}$, (constant function at $0$) since we can build homotopy for all loops based at $0$ as follows $H(s,t)=(1-t)f(s)+t$.
|
||||||
|
|
||||||
And $\Pi_1(X,1)=\{e\}$, (constant function at $1$.)
|
And $pi_1(X,1)=\{e\}$, (constant function at $1$.)
|
||||||
|
|
||||||
---
|
---
|
||||||
|
|
||||||
Let $X=\{1,2\}$ with discrete topology.
|
Let $X=\{1,2\}$ with discrete topology.
|
||||||
|
|
||||||
$\Pi_1(X,1)=\{e\}$, (constant function at $1$.)
|
$pi_1(X,1)=\{e\}$, (constant function at $1$.)
|
||||||
|
|
||||||
$\Pi_1(X,2)=\{e\}$, (constant function at $2$.)
|
$pi_1(X,2)=\{e\}$, (constant function at $2$.)
|
||||||
|
|
||||||
---
|
---
|
||||||
|
|
||||||
Let $X=S^1$ be the circle.
|
Let $X=S^1$ be the circle.
|
||||||
|
|
||||||
$\Pi_1(X,1)=\mathbb{Z}$ (related to winding numbers, prove next week).
|
$pi_1(X,1)=\mathbb{Z}$ (related to winding numbers, prove next week).
|
||||||
|
|
||||||
</details>
|
</details>
|
||||||
|
|
||||||
@@ -85,7 +85,7 @@ A natural question is, will the fundamental group depends on the base point $x$?
|
|||||||
|
|
||||||
#### Definition for $\hat{\alpha}$
|
#### Definition for $\hat{\alpha}$
|
||||||
|
|
||||||
Let $\alpha$ be a path in $X$ from $x_0$ to $x_1$. $\alpha:[0,1]\to X$ such that $\alpha(0)=x_0$ and $\alpha(1)=x_1$. Define $\hat{\alpha}:\Pi_1(X,x_0)\to \Pi_1(X,x_1)$ as follows:
|
Let $\alpha$ be a path in $X$ from $x_0$ to $x_1$. $\alpha:[0,1]\to X$ such that $\alpha(0)=x_0$ and $\alpha(1)=x_1$. Define $\hat{\alpha}:pi_1(X,x_0)\to pi_1(X,x_1)$ as follows:
|
||||||
|
|
||||||
$$
|
$$
|
||||||
\hat{\alpha}(\beta)=[\bar{\alpha}]*[f]*[\alpha]
|
\hat{\alpha}(\beta)=[\bar{\alpha}]*[f]*[\alpha]
|
||||||
@@ -93,12 +93,12 @@ $$
|
|||||||
|
|
||||||
#### $\hat{\alpha}$ is a group homomorphism
|
#### $\hat{\alpha}$ is a group homomorphism
|
||||||
|
|
||||||
$\hat{\alpha}$ is a group homomorphism between $(\Pi_1(X,x_0),*)$ and $(\Pi_1(X,x_1),*)$
|
$\hat{\alpha}$ is a group homomorphism between $(pi_1(X,x_0),*)$ and $(pi_1(X,x_1),*)$
|
||||||
|
|
||||||
<details>
|
<details>
|
||||||
<summary>Proof</summary>
|
<summary>Proof</summary>
|
||||||
|
|
||||||
Let $f,g\in \Pi_1(X,x_0)$, then $\hat{\alpha}(f*g)=\hat{\alpha}(f)\hat{\alpha}(g)$
|
Let $f,g\in pi_1(X,x_0)$, then $\hat{\alpha}(f*g)=\hat{\alpha}(f)\hat{\alpha}(g)$
|
||||||
|
|
||||||
$$
|
$$
|
||||||
\begin{aligned}
|
\begin{aligned}
|
||||||
@@ -129,4 +129,4 @@ The other case is the same
|
|||||||
|
|
||||||
#### Corollary of fundamental group
|
#### Corollary of fundamental group
|
||||||
|
|
||||||
If $X$ is path-connected and $x_0,x_1\in X$, then $\Pi_1(X,x_0)$ is isomorphic to $\Pi_1(X,x_1)$.
|
If $X$ is path-connected and $x_0,x_1\in X$, then $pi_1(X,x_0)$ is isomorphic to $pi_1(X,x_1)$.
|
||||||
|
|||||||
@@ -4,18 +4,18 @@
|
|||||||
|
|
||||||
### Fundamental group
|
### Fundamental group
|
||||||
|
|
||||||
Recall from last lecture, the $(\Pi_1(X,x_0),*)$ is a group, and for any two points $x_0,x_1\in X$, the group $(\Pi_1(X,x_0),*)$ is isomorphic to $(\Pi_1(X,x_1),*)$ if $x_0,x_1$ is path connected.
|
Recall from last lecture, the $(pi_1(X,x_0),*)$ is a group, and for any two points $x_0,x_1\in X$, the group $(pi_1(X,x_0),*)$ is isomorphic to $(pi_1(X,x_1),*)$ if $x_0,x_1$ is path connected.
|
||||||
|
|
||||||
> [!TIP]
|
> [!TIP]
|
||||||
>
|
>
|
||||||
> How does the $\hat{\alpha}$ (isomorphism between $(\Pi_1(X,x_0),*)$ and $(\Pi_1(X,x_1),*)$) depend on the choice of $\alpha$ (path) we choose?
|
> How does the $\hat{\alpha}$ (isomorphism between $(pi_1(X,x_0),*)$ and $(pi_1(X,x_1),*)$) depend on the choice of $\alpha$ (path) we choose?
|
||||||
|
|
||||||
#### Definition of simply connected
|
#### Definition of simply connected
|
||||||
|
|
||||||
A space $X$ is simply connected if
|
A space $X$ is simply connected if
|
||||||
|
|
||||||
- $X$ is [path-connected](https://notenextra.trance-0.com/Math4201/Math4201_L23/#definition-of-path-connected-space) ($\forall x_0,x_1\in X$, there exists a continuous function $\alpha:[0,1]\to X$ such that $\alpha(0)=x_0$ and $\alpha(1)=x_1$)
|
- $X$ is [path-connected](https://notenextra.trance-0.com/Math4201/Math4201_L23/#definition-of-path-connected-space) ($\forall x_0,x_1\in X$, there exists a continuous function $\alpha:[0,1]\to X$ such that $\alpha(0)=x_0$ and $\alpha(1)=x_1$)
|
||||||
- $\Pi_1(X,x_0)$ is the trivial group for some $x_0\in X$
|
- $pi_1(X,x_0)$ is the trivial group for some $x_0\in X$
|
||||||
|
|
||||||
<details>
|
<details>
|
||||||
<summary>Example of simply connected space</summary>
|
<summary>Example of simply connected space</summary>
|
||||||
@@ -59,7 +59,7 @@ $$
|
|||||||
|
|
||||||
#### Definition of group homomorphism induced by continuous map
|
#### Definition of group homomorphism induced by continuous map
|
||||||
|
|
||||||
Let $h:(X,x_0)\to (Y,y_0)$ be a continuous map, define $h_*:\Pi_1(X,x_0)\to \Pi_1(Y,y_0)$ where $h(x_0)=y_0$. by $h_*([f])=[h\circ f]$.
|
Let $h:(X,x_0)\to (Y,y_0)$ be a continuous map, define $h_*:pi_1(X,x_0)\to pi_1(Y,y_0)$ where $h(x_0)=y_0$. by $h_*([f])=[h\circ f]$.
|
||||||
|
|
||||||
$h_*$ is called the group homomorphism induced by $h$ relative to $x_0$.
|
$h_*$ is called the group homomorphism induced by $h$ relative to $x_0$.
|
||||||
|
|
||||||
@@ -80,7 +80,7 @@ $$
|
|||||||
|
|
||||||
#### Theorem composite of group homomorphism
|
#### Theorem composite of group homomorphism
|
||||||
|
|
||||||
If $h:(X,x_0)\to (Y,y_0)$ and $k:(Y,y_0)\to (Z,z_0)$ are continuous maps, then $k_* \circ h_*:\Pi_1(X,x_0)\to \Pi_1(Z,z_0)$ where $h_*:\Pi_1(X,x_0)\to \Pi_1(Y,y_0)$, $k_*:\Pi_1(Y,y_0)\to \Pi_1(Z,z_0)$,is a group homomorphism.
|
If $h:(X,x_0)\to (Y,y_0)$ and $k:(Y,y_0)\to (Z,z_0)$ are continuous maps, then $k_* \circ h_*:pi_1(X,x_0)\to pi_1(Z,z_0)$ where $h_*:pi_1(X,x_0)\to pi_1(Y,y_0)$, $k_*:pi_1(Y,y_0)\to pi_1(Z,z_0)$,is a group homomorphism.
|
||||||
|
|
||||||
<details>
|
<details>
|
||||||
<summary>Proof</summary>
|
<summary>Proof</summary>
|
||||||
@@ -100,7 +100,7 @@ $$
|
|||||||
|
|
||||||
#### Corollary of composite of group homomorphism
|
#### Corollary of composite of group homomorphism
|
||||||
|
|
||||||
Let $\operatorname{id}:(X,x_0)\to (X,x_0)$ be the identity map. This induces $(\operatorname{id})_*:\Pi_1(X,x_0)\to \Pi_1(X,x_0)$.
|
Let $\operatorname{id}:(X,x_0)\to (X,x_0)$ be the identity map. This induces $(\operatorname{id})_*:pi_1(X,x_0)\to pi_1(X,x_0)$.
|
||||||
|
|
||||||
If $h$ is a homeomorphism with the inverse $k$, with
|
If $h$ is a homeomorphism with the inverse $k$, with
|
||||||
|
|
||||||
@@ -108,7 +108,7 @@ $$
|
|||||||
k_*\circ h_*=(k\circ h)_*=(\operatorname{id})_*=I=(\operatorname{id})_*=(h\circ k)_*
|
k_*\circ h_*=(k\circ h)_*=(\operatorname{id})_*=I=(\operatorname{id})_*=(h\circ k)_*
|
||||||
$$
|
$$
|
||||||
|
|
||||||
This induced $h_*: \Pi_1(X,x_0)\to \Pi_1(Y,y_0)$ is an isomorphism.
|
This induced $h_*: pi_1(X,x_0)\to pi_1(Y,y_0)$ is an isomorphism.
|
||||||
|
|
||||||
#### Corollary for homotopy and group homomorphism
|
#### Corollary for homotopy and group homomorphism
|
||||||
|
|
||||||
|
|||||||
67
content/Math4202/Math4202_L21.md
Normal file
67
content/Math4202/Math4202_L21.md
Normal file
@@ -0,0 +1,67 @@
|
|||||||
|
# Math4202 Topology II (Lecture 21)
|
||||||
|
|
||||||
|
## Algebraic Topology
|
||||||
|
|
||||||
|
### Application of fundamental groups
|
||||||
|
|
||||||
|
Recall from last Friday, $j:S^1\to \mathbb{R}^2-\{0\}$ is not null homotopic
|
||||||
|
|
||||||
|
#### Hairy ball theorem
|
||||||
|
|
||||||
|
Given a non-vanishing vector field on $B^2=\{(x,y)\in\mathbb{R}^2:x^2+y^2\leq 1\}$, ($v:B^2\to \mathbb{R}^2$ continuous and $v(x,y)\neq 0$ for all $(x,y)\in B^2$) there exists a point of $S^1$ where the vector field points directly outward, and a point of $S^1$ where the vector field points directly inward.
|
||||||
|
|
||||||
|
<details>
|
||||||
|
<summary>Proof</summary>
|
||||||
|
|
||||||
|
By our assumption, then $v:B^2\to \mathbb{R}^2-\{0\}$ is a continuous vector field on $B^2$.
|
||||||
|
|
||||||
|
$v|_{S^1}:S^1\to \mathbb{R}^2-\{0\}$ is null homotopic.
|
||||||
|
|
||||||
|
We prove by contradiction.
|
||||||
|
|
||||||
|
Suppose $v:B^2\to \mathbb{R}^2-\{0\}$ and $v|_{S^1}:S^1\to \mathbb{R}^2-\{0\}$ is everywhere outward. (for everywhere inward, consider $-v$ must be everywhere outward)
|
||||||
|
|
||||||
|
Because $v|_{S^1}$ extends continuously to $B^2$, then $v|_{S^1}:B^2\to \mathbb{R}^2-\{0\}$ is null homotopic.
|
||||||
|
|
||||||
|
We construct a homotopy for functions between $v|_{S^1}$ and $j$. (Recall $j:S^1\to \mathbb{R}^2-\{0\}$ is not null homotopic)
|
||||||
|
|
||||||
|
Define $H:S^1\times I\to \mathbb{R}^2-\{0\}$ by affine combination
|
||||||
|
|
||||||
|
$$
|
||||||
|
H((x,y),t)=(1-t)v(x,y)+tj(x,y)
|
||||||
|
$$
|
||||||
|
|
||||||
|
we also need to show that $H$ is non zero.
|
||||||
|
|
||||||
|
Since $v$ is everywhere outward, $v(x,y)\cdot j(x,y)$ is positive for all $(x,y)\in S^1$.
|
||||||
|
|
||||||
|
$H((x,y),t)\cdot j(x,y)=(1-t)v(x,y)\cdot j(x,y)+tj(x,y)\cdot j(x,y)=(1-t)(v(x,y)\cdot j(x,y))+t$
|
||||||
|
|
||||||
|
which is positive for all $t\in I$, therefore $H$ is non zero.
|
||||||
|
|
||||||
|
So $H$ is a homotopy between $v|_{S^1}$ and $j$.
|
||||||
|
</details>
|
||||||
|
|
||||||
|
#### Corollary of the hairy ball theorem
|
||||||
|
|
||||||
|
$\forall v:B^2\to \mathbb{R}^2$, if on $S^1$, $v$ is everywhere outward/inward, there is $(x,y)\in B^2$ such that $v(x,y)=0$.
|
||||||
|
|
||||||
|
#### Brouwer's fixed point theorem
|
||||||
|
|
||||||
|
If $f:B^2\to B^2$ is continuous, then there exists a point $x\in B^2$ such that $f(x)=x$.
|
||||||
|
|
||||||
|
<details>
|
||||||
|
<summary>Proof</summary>
|
||||||
|
|
||||||
|
We proceed by contradiction again.
|
||||||
|
|
||||||
|
Suppose $f$ has no fixed point, $f(x)-x\neq 0$ for all $x\in B^2$.
|
||||||
|
|
||||||
|
Now we consider the map $v:B^2\to \mathbb{R}^2$ defined by $v(x,y)=f(x)-x$, this function is continuous since $f$ is continuous.
|
||||||
|
|
||||||
|
$forall x\in S^1$, $v(x)\cdot x=f(x)\cdot x-x\cdot x=f(x)\cdot x-1$.
|
||||||
|
|
||||||
|
Recall the cauchy schwartz theorem, $|f(x)\cdot x|\leq \|f(x)\|\cdot\|x\|\leq 1$, note that $f(x)\neq 0$ for all $x\in B^2$, $v(x)\cdot x<0$. This means that all $v(x)$ points inward.
|
||||||
|
|
||||||
|
This is a contradiction to the hairy ball theorem, so $f$ has a fixed point.
|
||||||
|
</details>
|
||||||
45
content/Math4202/Math4202_L22.md
Normal file
45
content/Math4202/Math4202_L22.md
Normal file
@@ -0,0 +1,45 @@
|
|||||||
|
# Math4202 Topology II (Lecture 22)
|
||||||
|
|
||||||
|
## Final reading, report, presentation
|
||||||
|
|
||||||
|
- Mar 30: Reading topic send email or discuss in OH.
|
||||||
|
- Apr 3: Finalize the plan.
|
||||||
|
- Apr 22,24: Last two lectures: 10 minutes to present.
|
||||||
|
- Final: type a short report, 2-5 pages.
|
||||||
|
|
||||||
|
## Algebraic topology
|
||||||
|
|
||||||
|
### Fundamental theorem of Algebra
|
||||||
|
|
||||||
|
For arbitrary polynomial $f(z)=\sum_{i=0}^n a_i x^i$. Are there roots in $\mathbb{C}$?
|
||||||
|
|
||||||
|
Consider $f(z)=a_nx^n+a_{n-1}x^{n-1}+a_{n-2}x^{n-2}+\cdots+a_0$ is a continuous map from $\mathbb{C}\to\mathbb{C}$.
|
||||||
|
|
||||||
|
If $f(z_0)=0$, then $z_0$ is a root.
|
||||||
|
|
||||||
|
By contradiction, Then $f:\mathbb{C}\to\mathbb{C}-\{0\}\cong \mathbb{R}^2-\{(0,0)\}$.
|
||||||
|
|
||||||
|
#### Theorem for existence of n roots
|
||||||
|
|
||||||
|
A polynomial equation $x^n+a_{n-1}x^{n-1}+a_{n-2}x^{n-2}+\cdots+a_0=0$ of degree $>0$ with complex coefficients has at least one complex root.
|
||||||
|
|
||||||
|
There are $n$ roots by induction.
|
||||||
|
|
||||||
|
#### Lemma
|
||||||
|
|
||||||
|
If $g:S^1\to \mathbb{R}^2-\{(0,0)\}$ is the map $g(z)=z^n$, then $g$ is not nulhomotopic. $n\neq 0$, $n\in \mathbb{Z}$.
|
||||||
|
|
||||||
|
> Recall that we proved that $g(z)=z$ is not nulhomotopic.
|
||||||
|
|
||||||
|
Consider $k:S^1\to S^1$ by $k(z)=z^n$. $k$ is continuous, $k_*:\pi_1(S^1,1)\to \pi_1(S^1,1)$.
|
||||||
|
|
||||||
|
Where $\pi_1(S^1,1)\cong \mathbb{Z}$.
|
||||||
|
|
||||||
|
$k_*(n)=nk_*(1)$.
|
||||||
|
|
||||||
|
Recall that the path in the loop $p:I\to S^1$ where $p:t\mapsto e^{2\pi it}$.
|
||||||
|
|
||||||
|
$k_*(p)=[k(p(t))]$, where $n=\tilde{k\circ p}(1)$.
|
||||||
|
|
||||||
|
$k_*$ is injective.
|
||||||
|
|
||||||
142
content/Math4202/Math4202_L23.md
Normal file
142
content/Math4202/Math4202_L23.md
Normal file
@@ -0,0 +1,142 @@
|
|||||||
|
# Math4202 Topology II (Lecture 23)
|
||||||
|
|
||||||
|
## Algebraic Topology
|
||||||
|
|
||||||
|
### Fundamental Theorem of Algebra
|
||||||
|
|
||||||
|
Recall the lemma $g:S^1\to \mathbb{R}-\{0\}$ is not nulhomotopic.
|
||||||
|
|
||||||
|
$g=h\circ k$ where $k:S^1\to S^1$ by $z\mapsto z^n$, $k_*:\pi_1(S^1)\to \pi_1(S^1)$ is injective. (consider the multiplication of integer is injective)
|
||||||
|
|
||||||
|
and $h:S^1\to \mathbb{R}-\{0\}$ where $z\mapsto z$. $h_*:\pi_1(S^1)\to \pi_1(\mathbb{R}-\{0\})$ is injective. (inclusion map is injective)
|
||||||
|
|
||||||
|
Therefore $g_*:\pi_1(S^1)\to \pi_1(\mathbb{R}-\{0\})$ is injective, therefore $g$ cannot be nulhomotopic. (nulhomotopic cannot be injective)
|
||||||
|
|
||||||
|
#### Theorem
|
||||||
|
|
||||||
|
Consider $x^n+a_{n-1}x^{n-1}+a_{n-2}x^{n-2}+\cdots+a_0=0$ of degree $>0$.
|
||||||
|
|
||||||
|
<details>
|
||||||
|
<summary>Proof: part 1</summary>
|
||||||
|
|
||||||
|
Step 1: if $|a_{n-1}|+|a_{n-2}|+\cdots+|a_0|<1$, then $x^n+a_{n-1}x^{n-1}+a_{n-2}x^{n-2}+\cdots+a_0=0$ has a root in the unit disk $B^2$.
|
||||||
|
|
||||||
|
We proceed by contradiction, suppose there is no root in $B^2$.
|
||||||
|
|
||||||
|
Consider $f(x)=x^n+a_{n-1}x^{n-1}+a_{n-2}x^{n-2}+\cdots+a_0$.
|
||||||
|
|
||||||
|
$f|_{B^2}$ is a continuous map from $B^2\to \mathbb{R}^2-\{0\}$.
|
||||||
|
|
||||||
|
$f|_{S^1=\partial B^2}:S^1\to \mathbb{R}-\{0\}$ **is nulhomotopic**.
|
||||||
|
|
||||||
|
> Recall that: Any map $g:S^1\to Y$ is nulhomotopic whenever it extends to a continuous map $G:B^2\to Y$.
|
||||||
|
|
||||||
|
Construct a homotopy between $f|_{S^1}$ and $g$
|
||||||
|
|
||||||
|
$$
|
||||||
|
H(x,t):S^1\to \mathbb{R}-\{0\}\quad x^n+t(a_{n-1}x^{n-1}+a_{n-2}x^{n-2}+\cdots+a_0)
|
||||||
|
$$
|
||||||
|
|
||||||
|
Observer on $S^1$, $\|x^n\|=1,\forall n\in \mathbb{N}$.
|
||||||
|
|
||||||
|
$$
|
||||||
|
\begin{aligned}
|
||||||
|
\|t(a_{n-1}x^{n-1}+a_{n-2}x^{n-2}+\cdots+a_0)\|&=t\|a_{n-1}x^{n-1}+a_{n-2}x^{n-2}+\cdots+a_0\|\\
|
||||||
|
&\leq 1(\|a_{n-1}x^{n-1}\|+\|a_{n-2}x^{n-2}\|+\cdots+\|a_0\|)\\
|
||||||
|
&=\|a_{n-1}\|+\|a_{n-2}\|+\cdots+\|a_0\|\\
|
||||||
|
&<1
|
||||||
|
\end{aligned}
|
||||||
|
$$
|
||||||
|
|
||||||
|
Therefore $H(s,t)>0\forall 0<t<1$. is a well-defined homotopy between $f|_{S^1}$ and $g$.
|
||||||
|
|
||||||
|
Therefore $f_*=g_*$ is injective, $f$ is not nulhomotopic. This contradicts our previous assumption that $f$ is nulhomotopic.
|
||||||
|
|
||||||
|
Therefore $f$ must have a root in $B^2$.
|
||||||
|
|
||||||
|
</details>
|
||||||
|
|
||||||
|
<details>
|
||||||
|
<summary>Proof: part 2</summary>
|
||||||
|
|
||||||
|
If $\|a_{n-1}\|+\|a_{n-2}\|+\cdots+\|a_0\|< R$ has a root in the disk $B^2_R$. (and $R\geq 1$, otherwise follows part 1)
|
||||||
|
|
||||||
|
Consider $\tilde{f}(x)=f(Rx)$.
|
||||||
|
$$
|
||||||
|
\begin{aligned}
|
||||||
|
\tilde{f}(x)
|
||||||
|
=f(Rx)&=(Rx)^n+a_{n-1}(Rx)^{n-1}+a_{n-2}(Rx)^{n-2}+\cdots+a_0\\
|
||||||
|
&=R^n\left(x^n+\frac{a_{n-1}}{R}x^{n-1}+\frac{a_{n-2}}{R^2}x^{n-2}+\cdots+\frac{a_0}{R^n}\right)
|
||||||
|
\end{aligned}
|
||||||
|
$$
|
||||||
|
|
||||||
|
$$
|
||||||
|
\begin{aligned}
|
||||||
|
\left\|\frac{a_{n-1}}{R}\right\|+\left\|\frac{a_{n-2}}{R^2}\right\|+\cdots+\left\|\frac{a_0}{R^n}\right\|&=\frac{1}{R}\|a_{n-1}\|+\frac{1}{R^2}\|a_{n-2}\|+\cdots+\frac{1}{R^n}\|a_0\|\\
|
||||||
|
&<\frac{1}{R}\left(\|a_{n-1}\|+\|a_{n-2}\|+\cdots+\|a_0\|\right)\\
|
||||||
|
&<\frac{1}{R}<1
|
||||||
|
\end{aligned}
|
||||||
|
$$
|
||||||
|
|
||||||
|
By Step 1, $\tilde{f}$ must have a root $z_0$ inside the unit disk.
|
||||||
|
|
||||||
|
$f(Rz_0)=\tilde{f}(z_0)=0$.
|
||||||
|
|
||||||
|
So $f$ has a root $Rz_0$ in $B^2_R$.
|
||||||
|
|
||||||
|
</details>
|
||||||
|
|
||||||
|
### Deformation Retracts and Homotopy Type
|
||||||
|
|
||||||
|
Recall previous section, $h:S^1\to \mathbb{R}-\{0\}$ gives $h_*:\pi_1(S^1,1)\to \pi_1(\mathbb{R}-\{0\},0)$ is injective.
|
||||||
|
|
||||||
|
For this section, we will show that $h_*$ is an isomorphism.
|
||||||
|
|
||||||
|
#### Lemma for equality of homomorphism
|
||||||
|
|
||||||
|
Let $h,k: (X,x_0)\to (Y,y_0)$ be continuous maps. If $h$ and $k$ are homotopic, and if **the image of $x_0$ under the homotopy remains $y_0$**. The homomorphism $h_*$ and $k_*$ from $\pi_1(X,x_0)$ to $\pi_1(Y,y_0)$ are equal.
|
||||||
|
|
||||||
|
<details>
|
||||||
|
<summary>Proof</summary>
|
||||||
|
|
||||||
|
Let $H:X\times I\to Y$ be a homotopy from $h$ to $k$ such that
|
||||||
|
$$
|
||||||
|
H(x,0)=h(x), \qquad H(x,1)=k(x), \qquad H(x_0,t)=y_0 \text{ for all } t\in I.
|
||||||
|
$$
|
||||||
|
|
||||||
|
To show $h_*=k_*$, let $[f]\in \pi_1(X,x_0)$ be arbitrary, where
|
||||||
|
$f:I\to X$ is a loop based at $x_0$, so $f(0)=f(1)=x_0$.
|
||||||
|
|
||||||
|
Define
|
||||||
|
$$
|
||||||
|
F:I\times I\to Y,\qquad F(s,t)=H(f(s),t).
|
||||||
|
$$
|
||||||
|
Since $H$ and $f$ are continuous, $F$ is continuous. For each fixed $t\in I$, the map
|
||||||
|
$$
|
||||||
|
s\mapsto F(s,t)=H(f(s),t)
|
||||||
|
$$
|
||||||
|
is a loop based at $y_0$, because
|
||||||
|
$$
|
||||||
|
F(0,t)=H(f(0),t)=H(x_0,t)=y_0
|
||||||
|
\quad\text{and}\quad
|
||||||
|
F(1,t)=H(f(1),t)=H(x_0,t)=y_0.
|
||||||
|
$$
|
||||||
|
Thus $F$ is a based homotopy between the loops $h\circ f$ and $k\circ f$, since
|
||||||
|
$$
|
||||||
|
F(s,0)=H(f(s),0)=h(f(s))=(h\circ f)(s),
|
||||||
|
$$
|
||||||
|
and
|
||||||
|
$$
|
||||||
|
F(s,1)=H(f(s),1)=k(f(s))=(k\circ f)(s).
|
||||||
|
$$
|
||||||
|
|
||||||
|
Therefore $h\circ f$ and $k\circ f$ represent the same element of $\pi_1(Y,y_0)$, so
|
||||||
|
$$
|
||||||
|
[h\circ f]=[k\circ f].
|
||||||
|
$$
|
||||||
|
Hence
|
||||||
|
$$
|
||||||
|
h_*([f])=[h\circ f]=[k\circ f]=k_*([f]).
|
||||||
|
$$
|
||||||
|
Since $[f]$ was arbitrary, it follows that $h_*=k_*$.
|
||||||
|
</details>
|
||||||
84
content/Math4202/Math4202_L24.md
Normal file
84
content/Math4202/Math4202_L24.md
Normal file
@@ -0,0 +1,84 @@
|
|||||||
|
# Math4202 Topology II (Lecture 24)
|
||||||
|
|
||||||
|
## Algebraic Topology
|
||||||
|
|
||||||
|
### Deformation Retracts and Homotopy Type
|
||||||
|
|
||||||
|
Recall from last lecture, let $h,k:(X,x_0)\to (Y,y_0)$ be continuous maps. If there exists a homotopy of $h,y$ such that $H:X\times I\to Y$ that $H(x_0,t)=y_0$.
|
||||||
|
|
||||||
|
Then $h_*=k_*:\pi_1(X,x_0)\to \pi_1(Y,y_0)$.
|
||||||
|
|
||||||
|
We can prove this by showing that all the loop $f:I\to X$ based at $x_0$, $h_*([f])=k_*([f])$.
|
||||||
|
|
||||||
|
That is $[h\circ f]=[k\circ f]$.
|
||||||
|
|
||||||
|
This is a function $I\times I \to Y$ by $(s,t)\mapsto H(f(s),t)$.
|
||||||
|
|
||||||
|
We need to show that this is a homotopy between $h\circ f$ and $k\circ f$.
|
||||||
|
|
||||||
|
#### Theorem
|
||||||
|
|
||||||
|
The Inclusion map $j:S^n\to \mathbb{R}^n-\{0\}$ induces on isomorphism of fundamental groups
|
||||||
|
|
||||||
|
$$
|
||||||
|
j_*:\pi_1(S^n)\to \pi_1(\mathbb{R}^n-\{0\})
|
||||||
|
$$
|
||||||
|
|
||||||
|
The function is injective.
|
||||||
|
|
||||||
|
> Recall we showed that $S^1\to \mathbb{R}-\{0\}$ is injective by $x\mapsto \frac{x}{|x|}$.
|
||||||
|
|
||||||
|
We want to show that $j_*\circ r_*=id_{\pi_1(S^n)}\quad r_*\circ j_*=id_{\pi_1(\mathbb{R}^n-\{0\})}$, then $r_*$, $j_*$ are isomorphism.
|
||||||
|
|
||||||
|
<details>
|
||||||
|
<summary>Proof</summary>
|
||||||
|
|
||||||
|
**Homotopy is well defined**.
|
||||||
|
|
||||||
|
Consider $H:(\mathbb{R}^n-\{0\})\times I\to \mathbb{R}^n-\{0\}$.
|
||||||
|
|
||||||
|
Given $(x,t)\mapsto tx+(1-t)\frac{x}{\|x\|}$.
|
||||||
|
|
||||||
|
Note that $(t-\frac{1-t}{\|x\|})x=0\implies t=0\land t=1$.
|
||||||
|
|
||||||
|
So this map is well defined.
|
||||||
|
|
||||||
|
**Base point is fixed**.
|
||||||
|
|
||||||
|
On point $(1,0)$ (or anything on the sphere), $H(x,0)=x$.
|
||||||
|
|
||||||
|
</details>
|
||||||
|
|
||||||
|
#### Definition of deformation retract
|
||||||
|
|
||||||
|
Let $A$ be a subspace of $X$, we say that $A$ is a deformation retract of $X$ if the identity map of $X$ is homotopic to a map that carries all $X$ to $A$ such that each point of $A$ remains fixed during the homotopy.
|
||||||
|
|
||||||
|
Equivalently, there exists a homotopy $H:X\times I\to X$ such that:
|
||||||
|
|
||||||
|
- $H(x,0)=x$ forall $x\in X$
|
||||||
|
- $H(a,t)=a$ for all $a\in A$, $t\in I$
|
||||||
|
- $H(x,1)\in A$ for all $x\in X$
|
||||||
|
|
||||||
|
Equivalently,
|
||||||
|
|
||||||
|
$r:H(x,1):X\to A$ is a retract.
|
||||||
|
|
||||||
|
If we let $j:A\to X$ be the inclusion map, then $r\circ j=id_A$, and $j\circ r\sim id_X$ (with $A$ fixed.)
|
||||||
|
|
||||||
|
<details>
|
||||||
|
<summary>Example of deformation retract</summary>
|
||||||
|
|
||||||
|
$S^1$ is a deformation retract of $\mathbb{R}^2-\{0\}$
|
||||||
|
|
||||||
|
---
|
||||||
|
|
||||||
|
Consider $\mathbb{R}^2-p=q$, the doubly punctured plane. "The figure 8" space is the deformation retract.
|
||||||
|
|
||||||
|
|
||||||
|
|
||||||
|
</details>
|
||||||
|
|
||||||
|
#### Theorem for Deformation Retract
|
||||||
|
|
||||||
|
If $A$ is a deformation retract of $X$, then $A$ and $X$ have the same fundamental group.
|
||||||
|
|
||||||
89
content/Math4202/Math4202_L25.md
Normal file
89
content/Math4202/Math4202_L25.md
Normal file
@@ -0,0 +1,89 @@
|
|||||||
|
# Math4202 Topology II (Lecture 25)
|
||||||
|
|
||||||
|
## Algebraic Topology
|
||||||
|
|
||||||
|
### Deformation Retracts and Homotopy Type
|
||||||
|
|
||||||
|
Recall from last lecture, Let $A\subseteq X$, if there exists a continuous map (deformation retraction) $H:X\times I\to X$ such that
|
||||||
|
|
||||||
|
- $H(x,0)=x$ for all $x\in X$
|
||||||
|
- $H(x,1)\in A$ for all $x\in X$
|
||||||
|
- $H(a,t)=a$ for all $a\in A$, $t\in I$
|
||||||
|
|
||||||
|
then the inclusion map$\pi_1(A,a)\to \pi_1(X,a)$ is an isomorphism.
|
||||||
|
|
||||||
|
<details>
|
||||||
|
<summary>Example for more deformation retract</summary>
|
||||||
|
|
||||||
|
Let $X=\mathbb{R}^3-\{0,(0,0,1)\}$.
|
||||||
|
|
||||||
|
Then the two sphere with one point intersect is a deformation retract of $X$.
|
||||||
|
|
||||||
|
---
|
||||||
|
|
||||||
|
Let $X$ be $\mathbb{R}^3-\{(t,0,0)\mid t\in \mathbb{R}\}$, then the cyclinder is a deformation retract of $X$.
|
||||||
|
|
||||||
|
</details>
|
||||||
|
|
||||||
|
#### Definition of homotopy equivalence
|
||||||
|
|
||||||
|
Let $f:X\to Y$ and $g:Y\to X$ be a continuous maps.
|
||||||
|
|
||||||
|
Suppose
|
||||||
|
|
||||||
|
- the map $g\circ f:X\to X$ is homotopic to the identity map $\operatorname{id}_X$.
|
||||||
|
- the map $f\circ g:Y\to Y$ is homotopic to the identity map $\operatorname{id}_Y$.
|
||||||
|
|
||||||
|
Then $f$ and $g$ are **homotopy equivalences**, and each is said to be the **homotopy inverse** of the other.
|
||||||
|
|
||||||
|
$X$ and $Y$ are said to be **homotopy equivalent**.
|
||||||
|
|
||||||
|
<details>
|
||||||
|
<summary>Example</summary>
|
||||||
|
|
||||||
|
Consider the punctured torus $X=S^1\times S^1-\{(0,0)\}$.
|
||||||
|
|
||||||
|
Then we can do deformation retract of the glued square space to boundary of the square.
|
||||||
|
|
||||||
|
After glueing, we left with the figure 8 space.
|
||||||
|
|
||||||
|
Then $X$ is homotopy equivalent to the figure 8 space.
|
||||||
|
|
||||||
|
</details>
|
||||||
|
|
||||||
|
Recall the lemma, [Lemma for equality of homomorphism](https://notenextra.trance-0.com/Math4202/Math4202_L23/#lemma-for-equality-of-homomorphism)
|
||||||
|
|
||||||
|
Let $f:X\to Y$ and $g:X\to Y$, with homotopy $H:X\times I\to Y$, such that
|
||||||
|
|
||||||
|
- $H(x,0)=f(x)$ for all $x\in X$
|
||||||
|
- $H(x,1)=g(x)$ for all $x\in X$
|
||||||
|
- $H(x,t)=y_0$ for all $t\in I$, and $y_0\in Y$ is fixed.
|
||||||
|
|
||||||
|
Then $f_*=g_*:\pi_1(X,x_0)\to \pi_1(Y,y_0)$ is an isomorphism.
|
||||||
|
|
||||||
|
We wan to know if it is safe to remove the assumption that $y_0$ is fixed.
|
||||||
|
|
||||||
|
<details>
|
||||||
|
<summary>Idea of Proof</summary>
|
||||||
|
|
||||||
|
Let $k$ be any loop in $\pi_1(X,x_0)$.
|
||||||
|
|
||||||
|
We can correlate the two fundamental group $f\cric k$ by the function $\alpha:I\to Y$, and $\hat{\alpha}:\pi_1(Y,y_0)\to \pi_1(Y,y_1)$. (suppose $f(x_0)=y_0, g(x_0)=y_1$), it is sufficient to show that
|
||||||
|
|
||||||
|
$$
|
||||||
|
f\circ k\simeq \alpha *(g\circ k)*\bar{\alpha}
|
||||||
|
$$
|
||||||
|
|
||||||
|
</details>
|
||||||
|
|
||||||
|
#### Lemma of homotopy equivalence
|
||||||
|
|
||||||
|
Let $f,g:X\to Y$ be continuous maps. let $f(x_0)=y_0$ and $g(x_0)=y_1$. If $f$ and $g$ are homotopic, then there is a path $\alpha:I\to Y$ such that $\alpha(0)=y_0$ and $\alpha(1)=y_1$.
|
||||||
|
|
||||||
|
Defined as the restriction of the homotopy to $\{x_0\}\times I$, satisfying $\hat{\alpha}\circ f_*=g_*$.
|
||||||
|
|
||||||
|
Imagine a triangle here:
|
||||||
|
|
||||||
|
- $\pi_1(X,x_0)\to \pi_1(Y,y_0)$ by $f_*$
|
||||||
|
- $\pi_1(Y,y_0)\to \pi_1(Y,y_1)$ by $\hat{\alpha}$
|
||||||
|
- $\pi_1(Y,y_1)\to \pi_1(X,x_0)$ by $g_*$
|
||||||
90
content/Math4202/Math4202_L26.md
Normal file
90
content/Math4202/Math4202_L26.md
Normal file
@@ -0,0 +1,90 @@
|
|||||||
|
# Math4202 Topology II (Lecture 26)
|
||||||
|
|
||||||
|
## Algebraic Topology
|
||||||
|
|
||||||
|
### Deformation Retracts and Homotopy Type
|
||||||
|
|
||||||
|
#### Lemma of homotopy equivalence
|
||||||
|
|
||||||
|
Let $f,g:X\to Y$ be continuous maps. let
|
||||||
|
|
||||||
|
$$
|
||||||
|
f_*=\pi_1(X,f(x_0))\quad\text{and}\quad g_*=\pi_1(Y,g(x_0))
|
||||||
|
$$
|
||||||
|
|
||||||
|
And $H:X\times I\to Y$ is a homotopy from $f$ to $g$ with a path $H(x_0,t)=\alpha(t)$ for all $t\in I$.
|
||||||
|
|
||||||
|
Then $\hat{\alpha}\circ f_*=[\bar{\alpha}*(f\circ \gamma)*\alpha]=[g\circ \gamma]=g_*$. where $\gamma$ is a loop in $X$ based at $x_0$.
|
||||||
|
|
||||||
|
<details>
|
||||||
|
<summary>Proof</summary>
|
||||||
|
$I\times I\xrightarrow{\gamma_{id}} X\times I\xrightarrow{H} Y$
|
||||||
|
|
||||||
|
- $I\times \{0\}\mapsto f\circ\gamma$
|
||||||
|
- $I\times \{1\}\mapsto g\circ\gamma$
|
||||||
|
- $\{0\}\times I\mapsto \alpha$
|
||||||
|
- $\{1\}\times I\mapsto \alpha$
|
||||||
|
|
||||||
|
As $I\times I$ is convex, $I\times \{0\}\simeq (\{0\}\times I)*(I\times \{1\})*(\{1\}\times I)$.
|
||||||
|
|
||||||
|
</details>
|
||||||
|
|
||||||
|
#### Corollary for homotopic continuous maps
|
||||||
|
|
||||||
|
Let $h,k$ be homotopic continuous maps. And let $h(x_0)=y_0,k(x_0)=y_1$. If $h_*:\pi_1(X,x_0)\to \pi_1(Y,y_0)$ is injective, then $k_*:\pi_1(X,x_0)\to \pi_1(Y,y_1)$ is injective.
|
||||||
|
|
||||||
|
<details>
|
||||||
|
<summary>Proof</summary>
|
||||||
|
|
||||||
|
$\hat{\alpha}$ is an isomorphism of $\pi_1(Y,y_0)$ to $\pi_1(Y,y_1)$.
|
||||||
|
|
||||||
|
</details>
|
||||||
|
|
||||||
|
#### Corollary for nulhomotopic maps
|
||||||
|
|
||||||
|
Let $h:X\to Y$ be nulhomotopic. Then $h_*:\pi_1(X,x_0)\to \pi_1(Y,h(x_0))$ is a trivial group homomorphism (mapping to the constant map on $h(x_0)$).
|
||||||
|
|
||||||
|
#### Theorem for fundamental group isomorphism by homotopy equivalence
|
||||||
|
|
||||||
|
Let $f:X\to Y$ be a continuous map. Let $f(x_0)=y_0$. If $f$ is a [homotopy equivalence](https://notenextra.trance-0.com/Math4202/Math4202_L25/#definition-of-homotopy-equivalence) ($\exists g:Y\to X$ such that $fg\simeq id_X$, $gf\simeq id_Y$), then
|
||||||
|
|
||||||
|
$$
|
||||||
|
f_*:\pi_1(X,x_0)\to \pi_1(Y,y_0)
|
||||||
|
$$
|
||||||
|
is an isomorphism.
|
||||||
|
|
||||||
|
<details>
|
||||||
|
<summary>Proof</summary>
|
||||||
|
|
||||||
|
Let $g:Y\to X$ be the homotopy inverse of $f$.
|
||||||
|
|
||||||
|
Then,
|
||||||
|
|
||||||
|
$f_*\circ g_*=\alpha \circ id_{\pi_1(Y,y_0)}=\alpha$
|
||||||
|
|
||||||
|
And $g_*\circ f_*=\bar{\alpha}\circ id_{\pi_1(X,x_0)}=\bar{\alpha}$
|
||||||
|
|
||||||
|
So $f_*\circ (g_*\circ \hat{\alpha}^-1)=id_{\pi_1(X,x_0)}$
|
||||||
|
|
||||||
|
And $g_*\circ (f_*\circ \hat{\alpha}^-1)=id_{\pi_1(Y,y_0)}$
|
||||||
|
|
||||||
|
So $f_*$ is an isomorphism (have left and right inverse).
|
||||||
|
</details>
|
||||||
|
|
||||||
|
### Fundamental group of higher dimensional sphere
|
||||||
|
|
||||||
|
$\pi_1(S^n,x_0)=\{e\}$ for $n\geq 2$.
|
||||||
|
|
||||||
|
We can decompose the sphere to the union of two hemisphere and compute $\pi_1(S^n_+,x_0)=\pi_1(S^n_-,x_0)=\{e\}$
|
||||||
|
|
||||||
|
But for $n\geq 2$, $S^n_+\cap S^n_-=S^{n-1}$, where $S^1_+\cap S^1_-$ is two disjoint points.
|
||||||
|
|
||||||
|
#### Theorem for "gluing" fundamental group
|
||||||
|
|
||||||
|
Suppose $X=U\cup V$, where $U$ and $V$ are open subsets of $X$. Suppose that $U\cap V$ is path connected, and $x\in U\cap V$. Let $i,j$ be the inclusion maps of $U$ and $V$ into $X$, the images of the induced homomorphisms
|
||||||
|
|
||||||
|
$$
|
||||||
|
i_*:\pi_1(U,x_0)\to \pi_1(X,x_0)\quad j_*:\pi_1(V,x_0)\to \pi_1(X,x_0)
|
||||||
|
$$
|
||||||
|
|
||||||
|
The image of the two map generate $\pi_1(X,x_0)$.
|
||||||
69
content/Math4202/Math4202_L27.md
Normal file
69
content/Math4202/Math4202_L27.md
Normal file
@@ -0,0 +1,69 @@
|
|||||||
|
# Math4202 Topology II (Lecture 27)
|
||||||
|
|
||||||
|
## Algebraic Topology
|
||||||
|
|
||||||
|
### Fundamental Groups for Higher Dimensional Sphere
|
||||||
|
|
||||||
|
#### Theorem for "gluing" fundamental group
|
||||||
|
|
||||||
|
Suppose $X=U\cup V$, where $U$ and $V$ are open subsets of $X$. Suppose that $U\cap V$ is path connected, and $x\in U\cap V$. Let $i,j$ be the inclusion maps of $U$ and $V$ into $X$, the images of the induced homomorphisms
|
||||||
|
|
||||||
|
$$
|
||||||
|
i_*:\pi_1(U,x_0)\to \pi_1(X,x_0)\quad j_*:\pi_1(V,x_0)\to \pi_1(X,x_0)
|
||||||
|
$$
|
||||||
|
|
||||||
|
The image of the two map generate $\pi_1(X,x_0)$.
|
||||||
|
|
||||||
|
$G$ is a group, and let $S\subseteq G$, where $G$ is generated by $S$, if $\forall g\in G$, $\exists s_1,s_2,\ldots,s_n\in S$ such that $g=s_1s_2\ldots s_n\in G$. (We can write $G$ as a word of elements in $S$.)
|
||||||
|
|
||||||
|
<details>
|
||||||
|
<summary>Proof</summary>
|
||||||
|
|
||||||
|
Let $f$ be a loop in $X$, $f\simeq g_1*g_2*\ldots*g_n$, where $g_i$ is a loop in $U$ or $V$.
|
||||||
|
|
||||||
|
For example, consider the function, $f=f_1*f_2*f_3*f_4$, where $f_1\in S_+$, $f_2\in S_-$, $f_3\in S_+$, $f_4\in S_-$.
|
||||||
|
|
||||||
|
Take the functions $\bar{\alpha_1}*\alpha_1\simeq e_{x_1}$ where $x_1$ is the intersecting point on $f_1$ and $f_2$.
|
||||||
|
|
||||||
|
Therefore,
|
||||||
|
|
||||||
|
$$
|
||||||
|
\begin{aligned}
|
||||||
|
f&=f_1*f_2*f_3*f_4\\
|
||||||
|
&(f_1*\bar{\alpha})*(\alpha_1*f_2*\bar{\alpha_2})*(\alpha_2*f_3*\bar{\alpha_3})*(\alpha_4*f_4)
|
||||||
|
\end{aligned}
|
||||||
|
$$
|
||||||
|
|
||||||
|
This decompose $f$ into a word of elements in either $S_+$ or $S_-$.
|
||||||
|
|
||||||
|
---
|
||||||
|
|
||||||
|
Note that $f$ is a continuous function $I\to X$, for $t\in I$, $\exists I_t$ being a small neighborhood of $t$ such that $f(I_t)\subseteq U$ or $f(I_t)\subseteq V$.
|
||||||
|
|
||||||
|
Since $U_{t\in I}I_t=I$, then $\{I_t\}_{t\in I}$ is an open cover of $I$.
|
||||||
|
|
||||||
|
By compactness of $I$, there is a finite subcover $\{I_{t_1},\ldots,I_{t_n}\}$.
|
||||||
|
|
||||||
|
Therefore, we can create a partition of $I$ into $[s_i,s_{i+1}]\subseteq I_{t_k}$ for some $k$.
|
||||||
|
|
||||||
|
Then with the definition of $I_{t_k}$, $f([s_i,s_{i+1}])\subseteq U$ or $V$.
|
||||||
|
|
||||||
|
Then we can connect $x_0$ to $f(s_i)$ with a path $\alpha_i\subseteq U\cap V$.
|
||||||
|
|
||||||
|
$$
|
||||||
|
\begin{aligned}
|
||||||
|
f&=f|_{[s_0,s_1]}*f|_{[s_1,s_2]}*\ldots**f|_{[s_{n-1},s_n]}\\
|
||||||
|
&\simeq f|_{[s_0,s_1]}*(\bar{\alpha_1}*\alpha_1)*f|_{[s_1,s_2]}*(\bar{\alpha_2}*\alpha_2)*\ldots*f|_{[s_{n-1},s_n]}*(\bar{\alpha_n}*\alpha_n
|
||||||
|
)\\
|
||||||
|
&=(f|_{[s_0,s_1]}*\bar{\alpha_1})*(\alpha_1*f|_{[s_1,s_2]}*\bar{\alpha_2})*\ldots*(\alpha_{n-1}*f|_{[s_{n-1},s_n]}*\bar{\alpha_n})\\
|
||||||
|
&=g_1*g_2*\ldots*g_n
|
||||||
|
\end{aligned}
|
||||||
|
$$
|
||||||
|
|
||||||
|
</details>
|
||||||
|
|
||||||
|
#### Corollary in higher dimensional sphere
|
||||||
|
|
||||||
|
Since $S^n_+$ and $S^n_-$ are homeomorphic to open balls $B^n$, then $\pi_1(S^n_+,x_0)=\pi_1(S^n_-,x_0)=\pi_1(B^n,x_0)=\{e\}$ for $n\geq 2$.
|
||||||
|
|
||||||
|
> Preview: Van Kampen Theorem
|
||||||
@@ -17,6 +17,7 @@ An $m$-dimensional **manifold** is a topological space $X$ that is
|
|||||||
> Try to find some example that satisfies some of the properties above but not a manifold.
|
> Try to find some example that satisfies some of the properties above but not a manifold.
|
||||||
|
|
||||||
1. Non-Hausdorff
|
1. Non-Hausdorff
|
||||||
|
- Real line with two origin, as discussed in homework problem
|
||||||
2. Non-countable basis
|
2. Non-countable basis
|
||||||
- Consider $\mathbb{R}^\delta$ where the set is $\mathbb{R}$ with discrete topology. The basis must include all singleton sets in $\mathbb{R}$ therefore $\mathbb{R}^\delta$ is not second countable.
|
- Consider $\mathbb{R}^\delta$ where the set is $\mathbb{R}$ with discrete topology. The basis must include all singleton sets in $\mathbb{R}$ therefore $\mathbb{R}^\delta$ is not second countable.
|
||||||
3. Non-local euclidean
|
3. Non-local euclidean
|
||||||
|
|||||||
@@ -7,7 +7,7 @@
|
|||||||
Consider the space of paths up to homotopy equivalence.
|
Consider the space of paths up to homotopy equivalence.
|
||||||
|
|
||||||
$$
|
$$
|
||||||
\operatorname{Path}/\simeq_p(X) =\Pi_1(X)
|
\operatorname{Path}/\simeq_p(X) =pi_1(X)
|
||||||
$$
|
$$
|
||||||
|
|
||||||
We want to impose some group structure on $\operatorname{Path}/\simeq_p(X)$.
|
We want to impose some group structure on $\operatorname{Path}/\simeq_p(X)$.
|
||||||
@@ -33,9 +33,9 @@ Define the product $f*g$ of $f$ and $g$ to be the map $h:[0,1]\to X$.
|
|||||||
|
|
||||||
#### Definition for equivalent classes of paths
|
#### Definition for equivalent classes of paths
|
||||||
|
|
||||||
$\Pi_1(X,x)$ is the equivalent classes of paths starting and ending at $x$.
|
$pi_1(X,x)$ is the equivalent classes of paths starting and ending at $x$.
|
||||||
|
|
||||||
On $\Pi_1(X,x)$,, we define $\forall [f],[g],[f]*[g]=[f*g]$.
|
On $pi_1(X,x)$,, we define $\forall [f],[g],[f]*[g]=[f*g]$.
|
||||||
|
|
||||||
$$
|
$$
|
||||||
[f]\coloneqq \{f_i:[0,1]\to X|f_0(0)=f(0),f_i(1)=f(1)\}
|
[f]\coloneqq \{f_i:[0,1]\to X|f_0(0)=f(0),f_i(1)=f(1)\}
|
||||||
@@ -141,5 +141,5 @@ Continue next time.
|
|||||||
The fundamental group of $X$ at $x$ is defined to be
|
The fundamental group of $X$ at $x$ is defined to be
|
||||||
|
|
||||||
$$
|
$$
|
||||||
(\Pi_1(X,x),*)
|
(pi_1(X,x),*)
|
||||||
$$
|
$$
|
||||||
@@ -1,3 +1,5 @@
|
|||||||
|
import { MathJax } from "nextra/components";
|
||||||
|
|
||||||
export default {
|
export default {
|
||||||
index: "Course Description",
|
index: "Course Description",
|
||||||
"---":{
|
"---":{
|
||||||
@@ -24,4 +26,11 @@ export default {
|
|||||||
Math4202_L18: "Topology II (Lecture 18)",
|
Math4202_L18: "Topology II (Lecture 18)",
|
||||||
Math4202_L19: "Topology II (Lecture 19)",
|
Math4202_L19: "Topology II (Lecture 19)",
|
||||||
Math4202_L20: "Topology II (Lecture 20)",
|
Math4202_L20: "Topology II (Lecture 20)",
|
||||||
|
Math4202_L21: "Topology II (Lecture 21)",
|
||||||
|
Math4202_L22: "Topology II (Lecture 22)",
|
||||||
|
Math4202_L23: "Topology II (Lecture 23)",
|
||||||
|
Math4202_L24: "Topology II (Lecture 24)",
|
||||||
|
Math4202_L25: "Topology II (Lecture 25)",
|
||||||
|
Math4202_L26: "Topology II (Lecture 26)",
|
||||||
|
Math4202_L27: "Topology II (Lecture 27)",
|
||||||
}
|
}
|
||||||
|
|||||||
118
content/Math4302/Math4302_L21.md
Normal file
118
content/Math4302/Math4302_L21.md
Normal file
@@ -0,0 +1,118 @@
|
|||||||
|
# Math4302 Modern Algebra (Lecture 21)
|
||||||
|
|
||||||
|
## Groups
|
||||||
|
|
||||||
|
### Group acting on a set
|
||||||
|
|
||||||
|
#### Definition of orbits
|
||||||
|
|
||||||
|
We define the equivalence relation on $X$
|
||||||
|
|
||||||
|
$$
|
||||||
|
x\sim y\iff y=g\cdot x\text{ for some }g
|
||||||
|
$$
|
||||||
|
|
||||||
|
So we get a partition of $X$ into equivalence classes: orbits
|
||||||
|
|
||||||
|
$$
|
||||||
|
Gx\coloneqq \{g\cdot x|g\in G\}=\{y\in X|x\sim y\}
|
||||||
|
$$
|
||||||
|
|
||||||
|
is the orbit of $X$.
|
||||||
|
|
||||||
|
$x,y\in X$ either $Gx=Gy$ or $Gx\cap Gy=\emptyset$.
|
||||||
|
|
||||||
|
$X=\bigcup_{x\in X}Gx$.
|
||||||
|
|
||||||
|
<details>
|
||||||
|
<summary>Example</summary>
|
||||||
|
|
||||||
|
Let $D_4$ acting on $X=\{1,2,3,4\}$. Let $D_4=\{e,\rho,\rho^2,\rho^3,\mu,\mu\rho,\mu\rho^2,\mu\rho^3\}$.
|
||||||
|
|
||||||
|
define $\phi\in D_4$, $i\in X$, $\phi\cdot i=\phi(i)$
|
||||||
|
|
||||||
|
The orbits are:
|
||||||
|
|
||||||
|
orbit of 1: $D_4\cdot 1=\{1,2,3,4\}$. This is equal to orbit of 2,3,4.
|
||||||
|
|
||||||
|
---
|
||||||
|
|
||||||
|
Let $G=S_3$ acting on $X=S_3$ via conjugation, let $\sigma\in X$ and $\phi\in G$, we define $\phi\cdot\sigma\coloneqq \phi\sigma\phi^{-1}$.
|
||||||
|
|
||||||
|
$S_3=\{e,(1,2,3),(1,3,2),(1,2),(1,3),(2,3)\}$.
|
||||||
|
|
||||||
|
The orbits are:
|
||||||
|
|
||||||
|
orbit of $e$: $G e=\{e\}$. since $geg^{-1}=e$ for all $g\in S_3$.
|
||||||
|
|
||||||
|
orbit of $(1,2,3)$:
|
||||||
|
|
||||||
|
- $e(1,2,3)e^{-1}=(1,2,3)$
|
||||||
|
- $(1,3,2)(1,2,3)(1,3,2)^{-1}=(1,2,3)$
|
||||||
|
- $(1,2,3)(1,2,3)(1,2,3)^{-1}=(1,2,3)$
|
||||||
|
- $(1,2)(1,2,3)(1,2)^{-1}=(2,3)(1,2)=(1,3,2)$
|
||||||
|
- $(1,3)(1,2,3)(1,3)^{-1}=(1,2)(1,3)=(1,3,2)$
|
||||||
|
- $(2,3)(1,2,3)(2,3)^{-1}=(1,3)(2,3)=(1,3,2)$
|
||||||
|
|
||||||
|
So the orbit of $(1,2,3)$ is equal to orbit of $(1,3,2)$. $=\{(1,2,3),(2,3,1)\}$.
|
||||||
|
|
||||||
|
orbit of $(1,2)$:
|
||||||
|
|
||||||
|
- $(1,2,3)(1,2)(1,2,3)^{-1}=(1,3)(1,3,2)=(2,3)$
|
||||||
|
- $(1,3,2)(1,2)(1,3,2)^{-1}=(2,3)(1,2,3)=(1,3)$
|
||||||
|
|
||||||
|
Therefore orbit of $(1,2)$ is equal to orbit of $(2,3)$, $(1,3)$. $=\{(1,2),(2,3),(1,3)\}$
|
||||||
|
|
||||||
|
The orbits may not have the same size.
|
||||||
|
|
||||||
|
</details>
|
||||||
|
|
||||||
|
#### Definition of isotropy subgroup
|
||||||
|
|
||||||
|
Let $X$ be a $G$-set, the stabilizer (or isotropy subgroup) corresponding to $x\in X$ is
|
||||||
|
|
||||||
|
$$
|
||||||
|
G_x=\{g\in G|g\cdot x=x\}
|
||||||
|
$$
|
||||||
|
|
||||||
|
$G_x$ is a subgroup of $G$. $G_x\leq G$.
|
||||||
|
|
||||||
|
- $e\cdot x=x$, so $e\in G_x$
|
||||||
|
- If $g_1,g_2\in G_x$, then $(g_1g_2)\cdot x=g_1\cdot(g_2\cdot x)=g_1 \cdot x$, so $g_1g_2\in G_x$
|
||||||
|
- If $g\in G_x$, then $g^{-1}\cdot g=x=g^{-1}\cdot x$, so $g^{-1}\in G_x$
|
||||||
|
|
||||||
|
<details>
|
||||||
|
<summary>Examples of isotropy subgroups</summary>
|
||||||
|
|
||||||
|
Let $D_4$ acting on $X=\{1,2,3,4\}$, find $G_1$, $G_2$, $G_3$, $G_4$.
|
||||||
|
|
||||||
|
$G_1=G_3=\{e,\mu\}$, $G_2=G_4=\{e,\mu\rho^2\}$.
|
||||||
|
|
||||||
|
---
|
||||||
|
|
||||||
|
Let $S_3$ acting on $X=S_3$. Find $G_{e}$, $G_{(1,2,3)}$, $G_{(1,2)}$.
|
||||||
|
|
||||||
|
$G_{e}=S_3$, $G_{(1,2,3)}=G_{(1,3,2)}=\{e,(1,2,3),(1,3,2)\}$, $G_{(1,2)}=\{e,(1,2)\}$, ($G_{(1,3)}=\{e,(1,3)\}$, $G_{(2,3)}=\{e,(2,3)\}$)
|
||||||
|
|
||||||
|
> The larger the orbit, the smaller the stabilizer.
|
||||||
|
|
||||||
|
</details>
|
||||||
|
|
||||||
|
#### Orbit-stabilizer theorem
|
||||||
|
|
||||||
|
If $X$ is a $G$-set and $x\in X$, then
|
||||||
|
|
||||||
|
$$
|
||||||
|
|Gx|=(G:G_x)=\text{ number of left cosets of }G_x=\frac{|G|}{|G_x|}
|
||||||
|
$$
|
||||||
|
|
||||||
|
<details>
|
||||||
|
<summary>Proof</summary>
|
||||||
|
|
||||||
|
Define $\alpha$ be the function that maps the set of left cosets of $G_x$ to orbit of $x$. $gG_X\mapsto g\cdot x$.
|
||||||
|
|
||||||
|
This function is well defined. And $\alpha$ is a bijection.
|
||||||
|
|
||||||
|
Continue next lecture.
|
||||||
|
|
||||||
|
</details>
|
||||||
109
content/Math4302/Math4302_L22.md
Normal file
109
content/Math4302/Math4302_L22.md
Normal file
@@ -0,0 +1,109 @@
|
|||||||
|
# Math4302 Modern Algebra (Lecture 22)
|
||||||
|
|
||||||
|
## Groups
|
||||||
|
|
||||||
|
### Group acting on a set
|
||||||
|
|
||||||
|
Let $X$ be a $G$-set, recall that the orbit of $x\in X$ is $\{g\cdot x|g\in G\}$.
|
||||||
|
|
||||||
|
#### The orbit-stabilizer theorem
|
||||||
|
|
||||||
|
For any $x\in X$, ,$G_x=\{g\in G|g\cdot x=x\}\leq G$.
|
||||||
|
|
||||||
|
Let $(G:G_x)$ denote the index of $G_x$ in $G$, then $(G:G_x)=\frac{|G|}{|G_x|}$, which equals to the number of left cosets of $G_x$ in $G$.
|
||||||
|
|
||||||
|
<details>
|
||||||
|
<summary>Proof</summary>
|
||||||
|
|
||||||
|
Define $\alpha:gG_x\mapsto g\cdot x$.
|
||||||
|
|
||||||
|
$\alpha$ is well-defined and injective.
|
||||||
|
|
||||||
|
$$
|
||||||
|
gG_x=g'G_x\iff g^{-1}g'\in G_x\iff (g^{-1}g')\cdot x=x\iff g^{-1}\cdot(g'\cdot x)=x\iff g'\cdot x=g\cdot x
|
||||||
|
$$
|
||||||
|
|
||||||
|
$\alpha$ is surjective, therefore $\alpha$ is a bijection.
|
||||||
|
|
||||||
|
</details>
|
||||||
|
|
||||||
|
<details>
|
||||||
|
<summary>Example</summary>
|
||||||
|
|
||||||
|
Number of elements in the orbit of $x$ is $1$ if and only if $g\cdot x=x$ for all $g\in G$.
|
||||||
|
|
||||||
|
if and only if $G_x=G$.
|
||||||
|
|
||||||
|
</details>
|
||||||
|
|
||||||
|
#### Theorem for orbit with prime power groups
|
||||||
|
|
||||||
|
Suppose $X$ is a $G$-set, and $|G|=p^n$ for some prime $p$. Let $X_G$ be the set of all elements in $X$ whose orbit has size $1$. (Recall the orbit divides $X$ into disjoint partitions.) Then $|X|\equiv |X_G|\mod p$.
|
||||||
|
|
||||||
|
<details>
|
||||||
|
<summary>Examples</summary>
|
||||||
|
|
||||||
|
Let $G=D_4$ acting on $\{1,2,3,4\}=X$.
|
||||||
|
|
||||||
|
$X_G=\emptyset$ since there is no element whose orbit has size $1$.
|
||||||
|
|
||||||
|
---
|
||||||
|
|
||||||
|
Let $G=\mathbb{Z}_{11}$ acting on a set with $|X|=20$ if the action is not trivial, then what is $|X_G|$?
|
||||||
|
|
||||||
|
Using the theorem we have $|X_G|\equiv 20\mod 11=9$. Therefore $|X_G|=9$ or $20$, but the action is not trivial, $|X_G|=9$.
|
||||||
|
|
||||||
|
An instance for such $X=\mathbb{Z}_{11}\sqcup\{x_1,x_2,\ldots,x_9\}$, where $\mathbb{Z}_{11}$ acts on $\{x_1,x_2,\ldots,x_9\}$ trivially. and $\mathbb{Z}_{11}$ acts on $x_1$ with addition.
|
||||||
|
|
||||||
|
</details>
|
||||||
|
|
||||||
|
<details>
|
||||||
|
<summary>Proof</summary>
|
||||||
|
|
||||||
|
If $x\in X$ such that $|Gx|\geq 2$, then $\frac{|G|}{|G_x|}=|Gx|\geq 2$.
|
||||||
|
|
||||||
|
So $|G|=|G_x||Gx|\implies |Gx|$ divides $|G|$.
|
||||||
|
|
||||||
|
So $|Gx|=p^m$ for some $m\geq 1$.
|
||||||
|
|
||||||
|
Note that $X$ is the union of subset of elements with orbit of size $1$, and distinct orbits of sizes $\geq 2$. (each of them has size positive power of $p$)
|
||||||
|
|
||||||
|
So $p|(|X|-|X_G|)$.
|
||||||
|
|
||||||
|
this implies that $|X_G|\equiv |X_G|\mod p$.
|
||||||
|
|
||||||
|
</details>
|
||||||
|
|
||||||
|
#### Corollary: Cauchy's theorem
|
||||||
|
|
||||||
|
If $p$ is prime and $p|(|G|)$, then $G$ has a subgroup of order $p$.
|
||||||
|
|
||||||
|
> This does not hold when $p$ is not prime.
|
||||||
|
>
|
||||||
|
> Consider $A_4$ with order $12$, and $A_4$ has no subgroup of order $6$.
|
||||||
|
|
||||||
|
<details>
|
||||||
|
<summary>Proof</summary>
|
||||||
|
|
||||||
|
It is enough to show, there is $a\in G$ which has order $p$: $\{e,a,a^2,\ldots,a^{p-1}\}\leq G$.
|
||||||
|
|
||||||
|
Let $X=\{(g_1,g_2,\ldots,g_p)|g_i\in G,g_1g_2g_3\ldots g_p=e\}$.
|
||||||
|
|
||||||
|
Then $|X|=|G|^{p-1}$ since $g_p$ is determined uniquely by $g_p=(g_1,g_2,\ldots,g_{p-1})^{-1}$.
|
||||||
|
|
||||||
|
Therefore we can define $\mathbb{Z}_p$ acts on $X$ by shifting.
|
||||||
|
|
||||||
|
$i\in \mathbb{Z}_p$ $i\cdot (g_1,g_2,\ldots,g_p)=(g_{i+1},g_2,\ldots,g_p,g_1,\ldots,g_i)$.
|
||||||
|
|
||||||
|
$X$ is a $\mathbb{Z}_p$-set.
|
||||||
|
|
||||||
|
- $0\cdot (g_1,g_2,\ldots,g_p)=(g_1,g_2,\ldots,g_p)$.
|
||||||
|
- $j\cdot (i\cdot (g_1,g_2,\ldots,g_p))=(i+j)\cdot (g_1,g_2,\ldots,g_p)$.
|
||||||
|
|
||||||
|
By the previous theorem, $|X|\equiv |X_G|\mod p$.
|
||||||
|
|
||||||
|
Since $p$ divides $|G|^{p-1}$, $p$ also divides $|X_G|$. Therefore $(e,e,e,\ldots,e)\in X_G$. Therefore $|X_G|\geq 1$.
|
||||||
|
|
||||||
|
So $|X_G|\geq 2$, we have $(a,a,\ldots,a)\in X_G$, $a\neq e$, but $a^p=e$, so $ord(a)=p$.
|
||||||
|
|
||||||
|
</details>
|
||||||
133
content/Math4302/Math4302_L23.md
Normal file
133
content/Math4302/Math4302_L23.md
Normal file
@@ -0,0 +1,133 @@
|
|||||||
|
# Math4302 Modern Algebra (Lecture 23)
|
||||||
|
|
||||||
|
## Group
|
||||||
|
|
||||||
|
### Group acting on a set
|
||||||
|
|
||||||
|
#### Theorem for the orbit of a set with prime power group
|
||||||
|
|
||||||
|
Suppose $X$ is a $G$-set, and $|G|=p^n$ where $p$ is prime, then $|X_G|\equiv |X|\mod p$.
|
||||||
|
|
||||||
|
Where $X_G=\{x\in X|g\cdot x=x\text{ for all }g\in G\}=\{x\in X|\text{orbit of }x\text{ is trivial}\}$
|
||||||
|
|
||||||
|
#### Corollary: Cauchy's theorem
|
||||||
|
|
||||||
|
If $p$, where $p$ is a prime, divides $|G|$, then $G$ has a subgroup of order $p$. (equivalently, $g$ has an element of order $p$)
|
||||||
|
|
||||||
|
> This does not hold when $p$ is not prime.
|
||||||
|
>
|
||||||
|
> Consider $A_4$ with order $12$, and $A_4$ has no subgroup of order $6$.
|
||||||
|
|
||||||
|
#### Corollary: Center of prime power group is non-trivial
|
||||||
|
|
||||||
|
If $|G|=p^m$, then $Z(G)$ is non-trivial. ($Z(G)\neq \{e\}$)
|
||||||
|
|
||||||
|
<details>
|
||||||
|
<summary>Proof</summary>
|
||||||
|
|
||||||
|
Let $G$ act on $G$ via conjugation, then $g\cdot h=ghg^{-1}$. This makes $G$ to a $G$-set.
|
||||||
|
|
||||||
|
Apply the theorem, the set of elements with trivial orbit is; Let $X=G$, then $X_G=\{h\in G|g\cdot h=h\text{ for all }g\in G\}=\{h\in G|ghg^{-1}=h\text{ for all }g\in G\}=Z(G)$.
|
||||||
|
|
||||||
|
Therefore $|Z(G)|\equiv |G|\mod p$.
|
||||||
|
|
||||||
|
So $p$ divides $|Z(G)|$, so $|Z(G)|\neq 1$, therefore $Z(G)$ is non-trivial.
|
||||||
|
</details>
|
||||||
|
|
||||||
|
#### Proposition: Prime square group is abelian
|
||||||
|
|
||||||
|
If $|G|=p^2$, where $p$ is a prime, then $G$ is abelian.
|
||||||
|
|
||||||
|
<details>
|
||||||
|
<summary>Proof</summary>
|
||||||
|
|
||||||
|
Since $Z(G)$ is a subgroup of $G$, $|Z(G)|$ divides $p^2$ so $|Z(G)|=1, p$ or $p^2$.
|
||||||
|
|
||||||
|
By corollary center of prime power group is non-trivial, $Z(G)\neq 1$.
|
||||||
|
|
||||||
|
If $|Z(G)|=p$. If $|Z(G)|=p$, then consider the group $G/Z(G)$ (Note that $Z(G)\trianglelefteq G$). We have $|G/Z(G)|=p$ so $G/Z(G)$ is cyclic (by problem 13.39), therefore $G$ is abelian.
|
||||||
|
|
||||||
|
If $|Z(G)|=p^2$, then $G$ is abelian.
|
||||||
|
|
||||||
|
</details>
|
||||||
|
|
||||||
|
### Classification of small order
|
||||||
|
|
||||||
|
Let $G$ be a group
|
||||||
|
|
||||||
|
- $|G|=1$
|
||||||
|
- $G=\{e\}$
|
||||||
|
- $|G|=2$
|
||||||
|
- $G\simeq\mathbb{Z}_2$ (prime order)
|
||||||
|
- $|G|=3$
|
||||||
|
- $G\simeq\mathbb{Z}_3$ (prime order)
|
||||||
|
- $|G|=4$
|
||||||
|
- $G\simeq\mathbb{Z}_2\times \mathbb{Z}_2$
|
||||||
|
- $G\simeq\mathbb{Z}_4$
|
||||||
|
- $|G|=5$
|
||||||
|
- $G\simeq\mathbb{Z}_5$ (prime order)
|
||||||
|
- $|G|=6$
|
||||||
|
- $G\simeq S_3$
|
||||||
|
- $G\simeq\mathbb{Z}_3\times \mathbb{Z}_2\simeq \mathbb{Z}_6$
|
||||||
|
<details>
|
||||||
|
<summary>Proof</summary>
|
||||||
|
|
||||||
|
$|G|$ has an element of order $2$, namely $b$, and an element of order $3$, namely $a$.
|
||||||
|
|
||||||
|
So $e,a,a^2,b,ba,ba^2$ are distinct.
|
||||||
|
|
||||||
|
Therefore, there are only two possibilities for value of $ab$. ($a,a^2$ are inverse of each other, $b$ is inverse of itself.)
|
||||||
|
|
||||||
|
If $ab=ba$, then $G$ is abelian, then $G\simeq \mathbb{Z}_2\times \mathbb{Z}_3$.
|
||||||
|
|
||||||
|
If $ab=ba^2$, then $G\simeq S_3$.
|
||||||
|
</details>
|
||||||
|
|
||||||
|
- $|G|=7$
|
||||||
|
- $G\simeq\mathbb{Z}_7$ (prime order)
|
||||||
|
- $|G|=8$
|
||||||
|
- $G\simeq\mathbb{Z}_2\times \mathbb{Z}_2\times \mathbb{Z}_2$
|
||||||
|
- $G\simeq\mathbb{Z}_4\times \mathbb{Z}_2$
|
||||||
|
- $G\simeq\mathbb{Z}_8$
|
||||||
|
- $G\simeq D_4$
|
||||||
|
- $G\simeq$ quaternion group $\{e,i,j,k,-1,-i,-j,-k\}$ where $i^2=j^2=k^2=-1$, $(-1)^2=1$. $ij=l$, $jk=i$, $ki=j$, $ji=-k$, $kj=-i$, $ik=-j$.
|
||||||
|
- $|G|=9$
|
||||||
|
- $G\simeq\mathbb{Z}_3\times \mathbb{Z}_3$
|
||||||
|
- $G\simeq\mathbb{Z}_9$ (apply the corollary, $9=3^2$, these are all the possible cases)
|
||||||
|
- $|G|=10$
|
||||||
|
- $G\simeq\mathbb{Z}_5\times \mathbb{Z}_2\simeq \mathbb{Z}_{10}$
|
||||||
|
- $G\simeq D_5$
|
||||||
|
- $|G|=11$
|
||||||
|
- $G\simeq\mathbb{Z}_11$ (prime order)
|
||||||
|
- $|G|=12$
|
||||||
|
- $G\simeq\mathbb{Z}_3\times \mathbb{Z}_4$
|
||||||
|
- $G\simeq\mathbb{Z}_2\times \mathbb{Z}_2\times \mathbb{Z}_3$
|
||||||
|
- $A_4$
|
||||||
|
- $D_6\simeq S_3\times \mathbb{Z}_2$
|
||||||
|
- ??? One more
|
||||||
|
- $|G|=13$
|
||||||
|
- $G\simeq\mathbb{Z}_{13}$ (prime order)
|
||||||
|
- $|G|=14$
|
||||||
|
- $G\simeq\mathbb{Z}_2\times \mathbb{Z}_7$
|
||||||
|
- $G\simeq D_7$
|
||||||
|
|
||||||
|
#### Lemma for group of order $2p$ where $p$ is prime
|
||||||
|
|
||||||
|
If $p$ is prime, $p\neq 2$, and $|G|=2p$, then $G$ is either abelian $\simeq \mathbb{Z}_2\times \mathbb{Z}_p$ or $G\simeq D_p$
|
||||||
|
|
||||||
|
<details>
|
||||||
|
<summary>Proof</summary>
|
||||||
|
|
||||||
|
We know $G$ has an element of order 2, namely $b$, and an element of order $p$, namely $a$.
|
||||||
|
|
||||||
|
So $e,a,a^2,\dots ,a^{p-1},ba,ba^2,\dots,ba^{p-1}$ are distinct elements of $G$.
|
||||||
|
|
||||||
|
Consider $ab$, if $ab=ba$, then $G$ is abelian, then $G\simeq \mathbb{Z}_2\times \mathbb{Z}_p$.
|
||||||
|
|
||||||
|
If $ab=ba^{p-1}$, then $G\simeq D_p$.
|
||||||
|
|
||||||
|
$ab$ cannot be inverse of other elements, if $ab=ba^t$, where $2\leq t\leq p-2$, then $bab=a^t$, then $(bab)^t=a^{t^2}$, then $ba^tb=a^{t^2}$, therefore $a=a^{t^2}$, then $a^{t^2-1}=e$, so $p|(t^2-1)$, therefore $p|t-1$ or $p|t+1$.
|
||||||
|
|
||||||
|
This is not possible since $2\leq t\leq p-2$.
|
||||||
|
|
||||||
|
</details>
|
||||||
147
content/Math4302/Math4302_L24.md
Normal file
147
content/Math4302/Math4302_L24.md
Normal file
@@ -0,0 +1,147 @@
|
|||||||
|
# Math4302 Modern Algebra (Lecture 24)
|
||||||
|
|
||||||
|
## Rings
|
||||||
|
|
||||||
|
### Definition of ring
|
||||||
|
|
||||||
|
A ring is a set $R$ with binary operation $+$ and $\cdot$ such that:
|
||||||
|
|
||||||
|
- $(R,+)$ is an abelian group.
|
||||||
|
- Multiplication is associative: $(a\cdot b)\cdot c=a\cdot (b\cdot c)$.
|
||||||
|
- Distribution property: $a\cdot (b+c)=a\cdot b+a\cdot c$, $(b+c)\cdot a=b\cdot a+c\cdot a$. (Note that $\cdot$ may not be abelian, may not even be a group, therefore we need to distribute on both sides.)
|
||||||
|
|
||||||
|
> [!NOTE]
|
||||||
|
>
|
||||||
|
> $a\cdot b=ab$ will be used for the rest of the sections.
|
||||||
|
|
||||||
|
<details>
|
||||||
|
<summary>Examples of rings</summary>
|
||||||
|
|
||||||
|
$(\mathbb{Z},+,*)$, $(\mathbb{R},+,*)$ are rings.
|
||||||
|
|
||||||
|
---
|
||||||
|
|
||||||
|
$(2\mathbb{Z},+,\cdot)$ is a ring.
|
||||||
|
|
||||||
|
---
|
||||||
|
|
||||||
|
$(M_n(\mathbb{R}),+,\cdot)$ is a ring.
|
||||||
|
|
||||||
|
---
|
||||||
|
|
||||||
|
$(\mathbb{Z}_n,+,\cdot)$ is a ring, where $a\cdot b=a*b\mod n$.
|
||||||
|
|
||||||
|
e.g. in $\mathbb{Z}_{12}, 4\cdot 8=8$.
|
||||||
|
|
||||||
|
</details>
|
||||||
|
|
||||||
|
> [!TIP]
|
||||||
|
>
|
||||||
|
> If $(R+,\cdot)$ is a ring, then $(R,\cdot)$ may not be necessarily a group.
|
||||||
|
|
||||||
|
#### Properties of rings
|
||||||
|
|
||||||
|
Let $0$ denote the identity of addition of $R$. $-a$ denote the additive inverse of $a$.
|
||||||
|
|
||||||
|
- $0\cdot a=a\cdot 0=0$
|
||||||
|
- $(-a)b=a(-b)=-(ab)$, $\forall a,b\in R$
|
||||||
|
- $(-a)(-b)=ab$, $\forall a,b\in R$
|
||||||
|
|
||||||
|
<details>
|
||||||
|
<summary>Proof</summary>
|
||||||
|
|
||||||
|
1) $0\cdot a=(0+0)\cdot a=0\cdot a+0\cdot a$, by cancellation, $0\cdot a=0$.
|
||||||
|
Similarly, $a\cdot 0=0\cdot a=0$.
|
||||||
|
|
||||||
|
2) $(a+(-a))\cdot b=0\cdot b=0$ by (1), So $a\cdot b +(-a)\cdot b=0$, $(-a)\cdot b=-(ab)$. Similarly, $a\cdot (-b)=-(ab)$.
|
||||||
|
|
||||||
|
3) $(-a)(-b)=(a(-b))$ by (2), apply (2) again, $-(-(ab))=ab$.
|
||||||
|
</details>
|
||||||
|
|
||||||
|
#### Definition of commutative ring
|
||||||
|
|
||||||
|
A ring $(R,+,\cdot)$ is commutative if $a\cdot b=b\cdot a$, $\forall a,b\in R$.
|
||||||
|
|
||||||
|
<details>
|
||||||
|
<summary>Example of non commutative ring</summary>
|
||||||
|
|
||||||
|
$(M_n(\mathbb{R}),+,\cdot)$ is not commutative.
|
||||||
|
|
||||||
|
</details>
|
||||||
|
|
||||||
|
#### Definition of unity element
|
||||||
|
|
||||||
|
A ring $R$ has unity element if there is an element $1\in R$ such that $a\cdot 1=1\cdot a=a$, $\forall a\in R$.
|
||||||
|
|
||||||
|
> [!NOTE]
|
||||||
|
>
|
||||||
|
> Unity element is unique.
|
||||||
|
>
|
||||||
|
> Suppose $1,1'$ are unity elements, then $1\cdot 1'=1'\cdot 1=1$, $1=1'$.
|
||||||
|
|
||||||
|
<details>
|
||||||
|
<summary>Example of field have no unity element</summary>
|
||||||
|
|
||||||
|
$(2\mathbb{Z},+,\cdot)$ does not have unity element.
|
||||||
|
</details>
|
||||||
|
|
||||||
|
#### Definition of unit
|
||||||
|
|
||||||
|
Suppose $R$ is a ring with unity element. An element $a\in R$ is called a unit if there is $b\in R$ such that $a\cdot b=b\cdot a=1$.
|
||||||
|
|
||||||
|
In this case $b$ is called the inverse of $a$.
|
||||||
|
|
||||||
|
> [!TIP]
|
||||||
|
>
|
||||||
|
> If $a$ is a unit, then its inverse is unique. If $b,b'$ are inverses of $a$, then $b'=1b'=bab'=b1=b$.
|
||||||
|
|
||||||
|
We use $a^{-1}$ or $\frac{1}{a}$ to represent the inverse of $a$.
|
||||||
|
|
||||||
|
Let $R$ be a ring with unity, then $0$ is not a unit. (identity of addition has no multiplicative inverse)
|
||||||
|
|
||||||
|
If $0b=b0=1$, then $\forall a\in R$, $a=1a=0a=0$.
|
||||||
|
|
||||||
|
#### Definition of division ring
|
||||||
|
|
||||||
|
If every $a\neq 0$ in $R$ has a multiplicative inverse (is a unit), then $R$ is called a division ring.
|
||||||
|
|
||||||
|
#### Definition of field
|
||||||
|
|
||||||
|
A commutative division ring is called a field.
|
||||||
|
|
||||||
|
<details>
|
||||||
|
<summary>Example of field</summary>
|
||||||
|
|
||||||
|
$(\mathbb{R},+,\cdot)$ is a field.
|
||||||
|
|
||||||
|
---
|
||||||
|
|
||||||
|
$(\mathbb{Z}_p,+,\cdot)$ is a field, where $p$ is a prime number.
|
||||||
|
</details>
|
||||||
|
|
||||||
|
#### Lemma $\mathbb{Z}_p$ is a field
|
||||||
|
|
||||||
|
$\mathbb{Z}_p$ is a field if and only if $p$ is prime.
|
||||||
|
|
||||||
|
<details>
|
||||||
|
<summary>Proof</summary>
|
||||||
|
|
||||||
|
If $\mathbb{Z}_n$ is a field, then $n$ is prime.
|
||||||
|
|
||||||
|
<!-- This is equivalent to the statement that: If $\mathbb{Z}_p$ is a field and $1\leq m\leq n-1$, then $\operatorname{gcd}(m,n)=1$.
|
||||||
|
|
||||||
|
We $\operatorname{gcd}(m,n)=d>1$, -->
|
||||||
|
|
||||||
|
We proceed by contradiction. Suppose $n$ is not a prime, then $d|n$ for some $2\leq d\leq n-1$, then $[d]$ does not have inverse.
|
||||||
|
|
||||||
|
If $[d][x]=[1]$, then $dx\equiv 1\mod n$, so $dx-1=ny$ for some $y\in \mathbb{Z}$, but $d|dx$, and $d|ny$, so $d|1$ which is impossible.
|
||||||
|
|
||||||
|
Therefore, $n$ is prime.
|
||||||
|
|
||||||
|
---
|
||||||
|
|
||||||
|
If $p$ is prime, then $\mathbb{Z}_p$ is a field.
|
||||||
|
|
||||||
|
Since $p$ is a prime, then $\operatorname{gcd}(m,n)=1$ for $1\leq m\leq n-1$. So $1=mx+ny$ for some $x,y\in \mathbb{Z}_p$. Then $[x]$ (the remainder of $x$ when divided by $p$) is the multiplicative inverse of $[m]$. $[m][x]=[mx]=[1-ny]=[1]$.
|
||||||
|
|
||||||
|
</details>
|
||||||
141
content/Math4302/Math4302_L25.md
Normal file
141
content/Math4302/Math4302_L25.md
Normal file
@@ -0,0 +1,141 @@
|
|||||||
|
# Math4302 Modern Algebra (Lecture 25)
|
||||||
|
|
||||||
|
Midterm next, next Wednesday
|
||||||
|
|
||||||
|
## Rings
|
||||||
|
|
||||||
|
### Definitions
|
||||||
|
|
||||||
|
- commutative ring: elements $a\cdot b=b\cdot a$, $\forall a,b\in R$
|
||||||
|
- ring with unity: elements $a\cdot 1=1\cdot a=a$, $\forall a\in R$
|
||||||
|
- units: elements such that there is $a\cdot b=1$ for some $b\in R$.
|
||||||
|
- division ring: every element $a\neq 0$ has a multiplicative inverse $a^{-1}$ such that $a\cdot a^{-1}=1$.
|
||||||
|
- field: division ring that is commutative
|
||||||
|
|
||||||
|
<details>
|
||||||
|
<summary>Examples of division ring that is not a field</summary>
|
||||||
|
|
||||||
|
Quaternions
|
||||||
|
|
||||||
|
Let $i^2=-1$, $j^2=-1$, $k^2=-1$, with $ij=k$, $jk=i$, $ki=j$.
|
||||||
|
|
||||||
|
$R=\{a+bi+ci+dj\mid a,b,c,d\in \mathbb{R}\}$
|
||||||
|
|
||||||
|
$R$ is not commutative since $ij\neq ji$, but $R$ is a division ring.
|
||||||
|
|
||||||
|
Let $x=a+bi+cj+dk$ be none zero, then $\bar{x}=a-bi-cj-dk$, $x^{-1}=\frac{\bar{x}}{a^2+b^2+c^2+d^2}$ is also non zero and $xx^{-1}=1$.
|
||||||
|
|
||||||
|
</details>
|
||||||
|
|
||||||
|
Recall from last time $\mathbb{Z}_n$ is a field if and only if $n$ is prime.
|
||||||
|
|
||||||
|
#### Units in $\mathbb{Z}_n$ is coprime to $n$
|
||||||
|
|
||||||
|
More generally, $[m]\in \mathbb{Z}_n$ is a unit if and only if $\operatorname{gcd}(m,n)=1$.
|
||||||
|
|
||||||
|
<details>
|
||||||
|
<summary>Proof</summary>
|
||||||
|
|
||||||
|
Let $d=\operatorname{gcd}(m,n)$ and $[m]$ is a unit, then $\exists [x]\in \mathbb{Z}_n$ with $[m][z]=[1]$, so $mz\equiv 1\mod n$. so $mz-1=nt$ for some $t\in \mathbb{Z}$, but $d|m$, $d|t$, so $d|1$ implies $d=1$.
|
||||||
|
|
||||||
|
If $d=1$, so $1=mr+ns$ for some $r,s\in \mathbb{Z}_n$. If $x=r\mod n$, then $[x]$ is the inverse of $[m]$. $mr\equiv 1\mod n\implies [m][x]=[1]$.
|
||||||
|
|
||||||
|
</details>
|
||||||
|
|
||||||
|
### Integral Domains
|
||||||
|
|
||||||
|
#### Definition of zero divisors
|
||||||
|
|
||||||
|
If $a,b\in R$ with $a,b\neq 0$ and $ab=0$, then $a,b$ are called zero divisors.
|
||||||
|
|
||||||
|
<details>
|
||||||
|
<summary>Example of zero divisors</summary>
|
||||||
|
|
||||||
|
Consider $\mathbb{Z}_6$, then $2\cdot 3=0$, so $2$ and $3$ are zero divisors.
|
||||||
|
|
||||||
|
And $4\cdot 3=0$, so $4$ and $3$ are zero divisors.
|
||||||
|
|
||||||
|
> If $a$ is a unit, then $a$ is not a zero divisor.
|
||||||
|
|
||||||
|
$ab=0\implies a^{-1}ab=0\implies 1b=0\implies b=0$.
|
||||||
|
|
||||||
|
</details>
|
||||||
|
|
||||||
|
> [!NOTE]
|
||||||
|
>
|
||||||
|
> If an element is not unit, it may not be a zero divisor.
|
||||||
|
>
|
||||||
|
> Consider $R=\mathbb{Z}$ and $2$ is not a unit, but $2$ is not a zero divisor.
|
||||||
|
|
||||||
|
#### Zero divisors in $\mathbb{Z}_n$
|
||||||
|
|
||||||
|
$[m]\in \mathbb{Z}_n$ is a zero divisor if and only if $\operatorname{gcd}(m,n)>1$ ($m$ is not a unit).
|
||||||
|
|
||||||
|
<details>
|
||||||
|
<summary>Proof</summary>
|
||||||
|
|
||||||
|
If $d=\operatorname{gcd}(m,n)=1$, then $[m]$ is a unit, so $[m]$ is not a zero divisor.
|
||||||
|
|
||||||
|
Therefore $[m]$ is a zero divisor if $\operatorname{gcd}(m,n)>1$.
|
||||||
|
|
||||||
|
---
|
||||||
|
|
||||||
|
If $d=\operatorname{gcd}(m,n)>1$, then $n=n_1d,m=m_1d, 1\leq n_1<n$.
|
||||||
|
|
||||||
|
Then $mn_1=m_1dn_1=m_1n$, $n|mn_1$ $[m][n_1]=[0]$, $n_1\neq 0$, $[m]$ is a zero divisor.
|
||||||
|
|
||||||
|
</details>
|
||||||
|
|
||||||
|
#### Definition of integral domain
|
||||||
|
|
||||||
|
A commutative ring with unity is called a integral domain (or just a domain) if it has no zero divisors.
|
||||||
|
|
||||||
|
<details>
|
||||||
|
<summary>Example of integral domain</summary>
|
||||||
|
|
||||||
|
$\mathbb{Z}$ is a integral domain.
|
||||||
|
|
||||||
|
---
|
||||||
|
|
||||||
|
Any field is a integral domain.
|
||||||
|
</details>
|
||||||
|
|
||||||
|
#### Corollaries of integral domain
|
||||||
|
|
||||||
|
If $R$ is a integral domain, then we have cancellation property $ab=ac,a\neq 0\implies b=c$.
|
||||||
|
|
||||||
|
#### Units with multiplication forms a group
|
||||||
|
|
||||||
|
If $R$ is a ring with unity, then the units in $R$ forms a group under multiplication.
|
||||||
|
|
||||||
|
<details>
|
||||||
|
<summary>Proof</summary>
|
||||||
|
|
||||||
|
if $a,b$ are units, then $ab$ is a unit $(ab)^{-1}=b^{-1}a^{-1}$.
|
||||||
|
|
||||||
|
</details>
|
||||||
|
|
||||||
|
In particular, non-zero elements of any field form an abelian group under multiplication.
|
||||||
|
|
||||||
|
<details>
|
||||||
|
<summary>Example</summary>
|
||||||
|
|
||||||
|
Consider $\mathbb{Z}_p$ field, then $(\{1,2,\cdots,p-1\},\cdot)$ forms an abelian group of size $p-1$.
|
||||||
|
|
||||||
|
---
|
||||||
|
|
||||||
|
Consider $\mathbb{Z}_5$, then we have a group of size $4$ under multiplication.
|
||||||
|
|
||||||
|
- $1$ has order 1
|
||||||
|
- $2$ has order 4 $2,4,3,1$.
|
||||||
|
- $3$ has order 4 $3,4,2,1$.
|
||||||
|
- $4$ has order 2 $4,1$.
|
||||||
|
|
||||||
|
Therefore $\mathbb{Z}_5\simeq \mathbb{Z}_4$.
|
||||||
|
|
||||||
|
---
|
||||||
|
|
||||||
|
Therefore in $R=\mathbb{Z}_p$, $\mathbb{Z}_p^*=\{[1],[2],\cdots,[p-1]\}$ is a group of order $p-1$.
|
||||||
|
|
||||||
|
Therefore, for every $a\in \mathbb{Z}_p$, $[a]^{p-1}=[1]$, then $a^{p-1}\equiv 1\mod p$ (Fermat's little theorem).
|
||||||
|
</details>
|
||||||
111
content/Math4302/Math4302_L26.md
Normal file
111
content/Math4302/Math4302_L26.md
Normal file
@@ -0,0 +1,111 @@
|
|||||||
|
# Math4302 Modern Algebra (Lecture 26)
|
||||||
|
|
||||||
|
## Rings
|
||||||
|
|
||||||
|
### Fermat’s and Euler’s Theorems
|
||||||
|
|
||||||
|
Recall from last lecture, we consider $\mathbb{Z}_p$ and $\mathbb{Z}_p^*$ denote the group of units in $\mathbb{Z}_p$ with multiplication.
|
||||||
|
|
||||||
|
$$
|
||||||
|
\mathbb{Z}_p^* = \{1,2,\cdots,p-1\}, \quad |\mathbb{Z}_p^*| = p-1
|
||||||
|
$$
|
||||||
|
|
||||||
|
Let $[a]\in \mathbb{Z}_p^*$, then $[a]^{p-1}=[1]$, this implies that $a^{p-1}\mod p=1$.
|
||||||
|
|
||||||
|
Now if $m\in \mathbb{Z}$ and $a=$ remainder of $m$ by $p$, $[a]\in \mathbb{Z}_p$, implies $m\equiv a\mod p$.
|
||||||
|
|
||||||
|
Then $m^{p-1}\equiv a^{p-1}\mod p$.
|
||||||
|
|
||||||
|
So
|
||||||
|
|
||||||
|
#### Fermat’s little theorem
|
||||||
|
|
||||||
|
If $p$ is not a divisor of $m$, then $m^{p-1}\equiv 1\mod p$.
|
||||||
|
|
||||||
|
#### Corollary of Fermat’s little theorem
|
||||||
|
|
||||||
|
If $m\in \mathbb{Z}$, then $m^p\equiv m\mod p$.
|
||||||
|
|
||||||
|
<details>
|
||||||
|
<summary>Proof</summary>
|
||||||
|
|
||||||
|
If $p|m$, then $m^{p-1}\equiv 0\equiv m\mod p$.
|
||||||
|
|
||||||
|
If $p\not|m$, then by Fermat’s little theorem, $m^{p-1}\equiv 1\equiv m\mod p$, so $m^p\equiv m\mod p$.
|
||||||
|
|
||||||
|
</details>
|
||||||
|
|
||||||
|
<details>
|
||||||
|
<summary>Example</summary>
|
||||||
|
|
||||||
|
Find the remainder of $40^{100}$ by $19$.
|
||||||
|
|
||||||
|
$40^{100}\equiv 2^{100}\mod 19$
|
||||||
|
|
||||||
|
$2^{100}\equiv 2^{10}\mod 19$ (Fermat’s little theorem $2^18\equiv 1\mod 19, 2^{90}\equiv 1\mod 19$)
|
||||||
|
|
||||||
|
$2^10\equiv (-6)^2\mod 19\equiv 36\mod 19\equiv 17\mod 19$
|
||||||
|
|
||||||
|
---
|
||||||
|
|
||||||
|
For every integer $n$, $15|(n^{33}-n)$.
|
||||||
|
|
||||||
|
$15=3\cdot 5$, therefore enough to show that $3|(n^{33}-n)$ and $5|(n^{33}-n)$.
|
||||||
|
|
||||||
|
Apply the corollary of Fermat’s little theorem to $p=3$: $n^3\equiv n\mod 3$, $(n^3)^11\equiv n^{11}\equiv (n^3)^3 n^2=n^3 n^2\equiv n^3\mod 3\equiv n\mod 3$.
|
||||||
|
|
||||||
|
Therefore $3|(n^{33}-n)$.
|
||||||
|
|
||||||
|
Apply the corollary of Fermat’s little theorem to $p=5$: $n^5\equiv n\mod 5$, $n^30 n^3\equiv (n^5)^6 n^3\equiv n^6 n^3\equiv n^5\mod 5\equiv n\mod 5$.
|
||||||
|
|
||||||
|
Therefore $5|(n^{33}-n)$.
|
||||||
|
|
||||||
|
</details>
|
||||||
|
|
||||||
|
#### Euler’s totient function
|
||||||
|
|
||||||
|
Consider $\mathbb{Z}_6$, by definition for the group of units, $\mathbb{Z}_6^*=\{1,5\}$.
|
||||||
|
|
||||||
|
$$
|
||||||
|
\phi(n)=|\mathbb{Z}_n^*|=|\{1\leq x\leq n:gcd(x,n)=1\}|
|
||||||
|
$$
|
||||||
|
|
||||||
|
<details>
|
||||||
|
<summary>Example</summary>
|
||||||
|
|
||||||
|
$\phi(8)=|\{1,3,5,7\}|=4$
|
||||||
|
|
||||||
|
</details>
|
||||||
|
|
||||||
|
If $[a]\in \mathbb{Z}_n^*$, then $[a]^{\phi(n)}=[1]$. So $a^{\phi(n)}\equiv 1\mod n$.
|
||||||
|
|
||||||
|
#### Theorem
|
||||||
|
|
||||||
|
If $m\in \mathbb{Z}$, and $gcd(m,n)=1$, then $m^{\phi(n)}\equiv 1\mod n$.
|
||||||
|
|
||||||
|
<details>
|
||||||
|
<summary>Proof</summary>
|
||||||
|
|
||||||
|
If $a$ is the remainder of $m$ by $n$, then $m\equiv a\mod n$, and $\operatorname{gcd}(a,n)=1$, so $m^{\phi(n)}\equiv a^{\phi(n)}\equiv 1\mod n$.
|
||||||
|
|
||||||
|
</details>
|
||||||
|
|
||||||
|
#### Applications on solving modular equations
|
||||||
|
|
||||||
|
Solving equations of the form $ax\equiv b\mod n$.
|
||||||
|
|
||||||
|
Not always have solution, $2x\equiv 1\mod 4$ has no solution since $1$ is odd.
|
||||||
|
|
||||||
|
Solution for $2x\equiv 1\mod 3$
|
||||||
|
|
||||||
|
- $x\equiv 0\implies 2x\equiv 0\mod 3$
|
||||||
|
- $x\equiv 1\implies 2x\equiv 2\mod 3$
|
||||||
|
- $x\equiv 2\implies 2x\equiv 1\mod 3$
|
||||||
|
|
||||||
|
So solution for $2x\equiv 1\mod 3$ is $\{3k+2|k\in \mathbb{Z}\}$.
|
||||||
|
|
||||||
|
#### Theorem for exsistence of solution of modular equations
|
||||||
|
|
||||||
|
$ax\equiv b\mod n$ has a solution if and only if $\operatorname{gcd}(a,n)|b$ and in that case the equation has $d$ solutions in $\mathbb{Z}_n$.
|
||||||
|
|
||||||
|
Proof on next lecture.
|
||||||
126
content/Math4302/Math4302_L27.md
Normal file
126
content/Math4302/Math4302_L27.md
Normal file
@@ -0,0 +1,126 @@
|
|||||||
|
# Math4302 Modern Algebra (Lecture 27)
|
||||||
|
|
||||||
|
## Rings
|
||||||
|
|
||||||
|
### Fermat’s and Euler’s Theorems
|
||||||
|
|
||||||
|
Recall from last lecture, $ax\equiv b \mod n$, if $x\equiv y\mod n$, then $x$ is a solution if and only if $y$ is a solution.
|
||||||
|
|
||||||
|
#### Theorem for existence of solution of modular equations
|
||||||
|
|
||||||
|
$ax\equiv b\mod n$ has a solution if and only if $d=\operatorname{gcd}(a,n)|b$ And if there is a solution, then there are exactly $d$ solutions in $\mathbb{Z}_n$.
|
||||||
|
|
||||||
|
<details>
|
||||||
|
<summary>Proof</summary>
|
||||||
|
|
||||||
|
For the forward direction, we proved if $ax\equiv b\mod n$ then $ax-b=ny$, $y\in\mathbb{Z}$.
|
||||||
|
|
||||||
|
then $b=ax-ny$, $d|(ax-ny)$ implies that $d|b$.
|
||||||
|
|
||||||
|
---
|
||||||
|
|
||||||
|
For the backward direction, assume $d=\operatorname{gcd}(a,n)=1$. Then we need to show, there is exactly $1$ solution between $0$ and $n-1$.
|
||||||
|
|
||||||
|
If $ax\equiv b\mod n$, then in $\mathbb{Z}_n$, $[a][x]=[b]$. (where $[a]$ denotes the remainder of $a$ by $n$ and $[b]$ denotes the remainder of $b$ by $n$)
|
||||||
|
|
||||||
|
Since $\operatorname{gcd}(a,n)=1$, then $[a]$ is a unit in $\mathbb{Z}_n$, so we can multiply the above equation by the inverse of $[a]$. and get $[x]=[a]^{-1}[b]$.
|
||||||
|
|
||||||
|
Now assume $d=\operatorname{gcd}(a,n)$ where $n$ is arbitrary. Then $a=a'd$, then $n=n'd$, with $\operatorname{gcd}(a',n')=1$.
|
||||||
|
|
||||||
|
Also $d|b$ so $b=b'd$. So
|
||||||
|
|
||||||
|
$$
|
||||||
|
\begin{aligned}
|
||||||
|
ax\equiv b \mod n&\iff n|(ax-b)\\
|
||||||
|
&\iff n'd|(a'dx-b'd)\\
|
||||||
|
&\iff n'|(a'x-b')\\
|
||||||
|
&\iff a'x\equiv b'\mod n'
|
||||||
|
\end{aligned}
|
||||||
|
$$.
|
||||||
|
|
||||||
|
Since $\operatorname{gcd}(a',n')=1$, there is a unique solution $x_0\in \mathbb{Z}_{n'}$. $0\leq x_0\leq n'+1$. Other solution in $\mathbb{Z}$ are of the form $x_0+kn'$ for $k\in \mathbb{Z}$.
|
||||||
|
|
||||||
|
And there will be $d$ solutions in $\mathbb{Z}_n$,
|
||||||
|
|
||||||
|
</details>
|
||||||
|
|
||||||
|
<details>
|
||||||
|
<summary>Examples</summary>
|
||||||
|
|
||||||
|
Solve $12x\equiv 25\mod 7$.
|
||||||
|
|
||||||
|
$12\equiv 5\mod 7$, $25\equiv 4\mod 7$. So the equation becomes $5x\equiv 4\mod 7$.
|
||||||
|
|
||||||
|
$[5]^{-1}=3\in \mathbb{Z}_7$, so $[5][x]\equiv [4]$ implies $[x]\equiv [3][4]\equiv [5]\mod 7$.
|
||||||
|
|
||||||
|
So solution in $\mathbb{Z}$ is $\{5+7k:k\in \mathbb{Z}\}$.
|
||||||
|
|
||||||
|
---
|
||||||
|
|
||||||
|
Solve $6x\equiv 32\mod 20$.
|
||||||
|
|
||||||
|
$\operatorname{gcd}(6,20)=2$, so $6x\equiv 12\mod 20$ if and only if $3x\equiv 6\mod 10$.
|
||||||
|
|
||||||
|
$[3]^{-1}=[7]\in \mathbb{Z}_{10}$, so $[3][x]\equiv [6]$ implies $[x]\equiv [7][6]\equiv [2]\mod 10$.
|
||||||
|
|
||||||
|
So solution in $\mathbb{Z}_{20}$ is $[2]$ and $[12]$
|
||||||
|
|
||||||
|
So solution in $\mathbb{Z}$ is $\{2+10k:k\in \mathbb{Z}\}$
|
||||||
|
|
||||||
|
</details>
|
||||||
|
|
||||||
|
### Ring homomorphisms
|
||||||
|
|
||||||
|
#### Definition of ring homomorphism
|
||||||
|
|
||||||
|
Let $R,S$ be two rings, $f:R\to S$ is a ring homomorphism if $\forall a,b\in R$,
|
||||||
|
|
||||||
|
- $f(a+b)=f(a)+f(b)\implies f(0)=0, f(-a)=-f(a)$
|
||||||
|
- $f(ab)=f(a)f(b)$
|
||||||
|
|
||||||
|
#### Definition of ring isomorphism
|
||||||
|
|
||||||
|
If $f$ is a ring homomorphism and a bijection, then $f$ is called a ring isomorphism.
|
||||||
|
|
||||||
|
<details>
|
||||||
|
<summary>Example</summary>
|
||||||
|
Let $f:(\mathbb{Z},+,\times)\to(2\mathbb{Z},+,\times)$ by $f(a)=2a$.
|
||||||
|
|
||||||
|
Is not a ring homomorphism since $f(ab)\neq f(a)f(b)$ in general.
|
||||||
|
|
||||||
|
---
|
||||||
|
|
||||||
|
Let $f:(\mathbb{Z},+,\times)\to(\mathbb{Z}_n,+,\times)$ by $f(a)=a\mod n$
|
||||||
|
|
||||||
|
Is a ring homomorphism.
|
||||||
|
|
||||||
|
</details>
|
||||||
|
|
||||||
|
### Integral domains and their file fo fractions.
|
||||||
|
|
||||||
|
Let $R$ be an integral domain: (i.e. $R$ is commutative with unity and no zero divisors).
|
||||||
|
|
||||||
|
#### Definition of field of fractions
|
||||||
|
|
||||||
|
If $R$ is an integral domain, we can construct a field containing $R$ called the field of fractions (or called field of quotients) of $R$.
|
||||||
|
|
||||||
|
$$
|
||||||
|
S=\{(a,b)|a,b\in R, b\neq 0\}
|
||||||
|
$$
|
||||||
|
|
||||||
|
a relation on $S$ is defined as follows:
|
||||||
|
|
||||||
|
$(a,b)\sim (c,d)$ if and only if $ad=bc$.
|
||||||
|
|
||||||
|
<details>
|
||||||
|
<summary>This equivalence relation is well defined</summary>
|
||||||
|
|
||||||
|
- Reflectivity: $(a,b)\sim (a,b)$ $ab=ab$
|
||||||
|
- Symmetry: $(a,b)\sim (c,d)\Rightarrow (c,d)\sim (a,b)$
|
||||||
|
- Transitivity: $(a,b)\sim (c,d)$ and $(c,d)\sim (e,f)\Rightarrow (a,b)\sim (e,f)$
|
||||||
|
- $ad=bc$, and $cf=ed$, we want to conclude that $af=be$. since $ad=bc$, then $adf=bcf$, since $cf=ed$, then $cfb=edb$, therefore $adf=edb$.
|
||||||
|
- Then $d(af-be)=0$ since $d\neq 0$ then $af=be$.
|
||||||
|
|
||||||
|
</details>
|
||||||
|
|
||||||
|
Then $S/\sim$ is a field.
|
||||||
153
content/Math4302/Math4302_L28.md
Normal file
153
content/Math4302/Math4302_L28.md
Normal file
@@ -0,0 +1,153 @@
|
|||||||
|
# Math4302 Modern Algebra (Lecture 28)
|
||||||
|
|
||||||
|
## Rings
|
||||||
|
|
||||||
|
### Field of quotients
|
||||||
|
|
||||||
|
Let $R$ be an integral domain ($R$ has unity and commutative with no zero divisors).
|
||||||
|
|
||||||
|
Consider the pair $S=\{(a,b)|a,b\in R, b\neq 0\}$.
|
||||||
|
|
||||||
|
And define the equivalence relation on $S$ as follows:
|
||||||
|
|
||||||
|
$(a,b)\sim (c,d)$ if and only if $ad=bc$.
|
||||||
|
|
||||||
|
We denote $[(a,b)]$ as set of all elements in $S$ equivalent to $(a,b)$.
|
||||||
|
|
||||||
|
Let $F$ be the set of all equivalent classes. We define addition and multiplication on $F$ as follows:
|
||||||
|
|
||||||
|
$$
|
||||||
|
[(a,b)]+[(c,d)]=[(ad+bc,bd)]
|
||||||
|
$$
|
||||||
|
|
||||||
|
$$
|
||||||
|
[(a,b)]\cdot[(c,d)]=[(ac,bd)]
|
||||||
|
$$
|
||||||
|
|
||||||
|
<details>
|
||||||
|
<summary>The multiplication and addition is well defined </summary>
|
||||||
|
|
||||||
|
Addition:
|
||||||
|
|
||||||
|
If $(a,b)\sim (a',b')$, and $(c,d)\sim (c',d')$, then we want to show that $(ad+bc,bd)\sim (a'd+c'd,b'd)$.
|
||||||
|
|
||||||
|
Since $(a,b)\sim (a',b')$, then $ab'=a'b$; $(c,d)\sim (c',d')$, then $cd'=dc'$,
|
||||||
|
|
||||||
|
So $ab'dd'=a'bdd'$, and $cd'bb'=dc'bb'$.
|
||||||
|
|
||||||
|
$adb'd'+bcb'd'=a'd'bd+b'c'bd$, therefore $(ad+bc,bd)\sim (a'd+c'd,b'd)$.
|
||||||
|
|
||||||
|
---
|
||||||
|
|
||||||
|
Multiplication:
|
||||||
|
|
||||||
|
If $(a,b)\sim (a',b')$, and $(c,d)\sim (c',d')$, then we want to show that $(ac,bd)\sim (a'c',b'd')$.
|
||||||
|
|
||||||
|
Since $(a,b)\sim (a',b')$, then $ab'=a'b$; $(c,d)\sim (c',d')$, then $cd'=dc'$, so $(ac,bd)\sim (a'c',b'd')$
|
||||||
|
|
||||||
|
</details>
|
||||||
|
|
||||||
|
#### Claim (F,+,*) is a field
|
||||||
|
|
||||||
|
- additive identity: $(0,1)\in F$
|
||||||
|
- additive inverse: $(a,b)\in F$, then $(-a,b)\in F$ and $(-a,b)+(a,b)=(0,1)\in F$
|
||||||
|
- additive associativity: bit long.
|
||||||
|
|
||||||
|
- multiplicative identity: $(1,1)\in F$
|
||||||
|
- multiplicative inverse: $[(a,b)]$ is non zero if and only if $a\neq 0$, then $a^{-1}=[(b,a)]\in F$.
|
||||||
|
- multiplicative associativity: bit long
|
||||||
|
|
||||||
|
- distributivity: skip, too long.
|
||||||
|
|
||||||
|
Such field is called a quotient field of $R$.
|
||||||
|
|
||||||
|
And $F$ contains $R$ by $\phi:R\to F$, $\phi(a)=[(a,1)]$.
|
||||||
|
|
||||||
|
This is a ring homomorphism.
|
||||||
|
|
||||||
|
- $\phi(a+b)=[(a+b,1)]=[(a,1)][(b,1)]\phi(a)+\phi(b)$
|
||||||
|
- $\phi(ab)=[(ab,1)]=[(a,1)][(b,1)]\phi(a)\phi(b)$
|
||||||
|
|
||||||
|
and $\phi$ is injective.
|
||||||
|
|
||||||
|
If $\phi(a)=\phi(b)$, then $a=b$.
|
||||||
|
|
||||||
|
<details>
|
||||||
|
<summary>Example</summary>
|
||||||
|
|
||||||
|
Let $D\subset \mathbb R$ and
|
||||||
|
|
||||||
|
$$
|
||||||
|
\mathbb Z \subset D\coloneqq \{a+b\sqrt{2}:a,b\in \mathbb Z\}
|
||||||
|
$$
|
||||||
|
|
||||||
|
Then $D$ is a subring of $\mathbb R$, and integral domain, with usual addition and multiplication.
|
||||||
|
|
||||||
|
$$
|
||||||
|
(a+b\sqrt{2})(c+d\sqrt{2})=(ac+2bd)+(ad+bc)\sqrt{2}
|
||||||
|
$$
|
||||||
|
|
||||||
|
$$
|
||||||
|
-(a+b\sqrt{2})=(-a)+(-b)\sqrt{2})
|
||||||
|
$$
|
||||||
|
|
||||||
|
...
|
||||||
|
|
||||||
|
$D$ is a integral domain since $\mathbb R$ has no zero divisors, therefore $D$ has no zero divisors.
|
||||||
|
|
||||||
|
Consider the field of quotients of $D$. $[(a+b\sqrt{2},c+d\sqrt{2})]$. This is isomorphic to $\mathbb Q(\sqrt2)=\{r+s\sqrt{2}:r,s\in \mathbb Q\}$
|
||||||
|
|
||||||
|
$$
|
||||||
|
m+n\sqrt{2}=\frac{m}{n}+\frac{m'}{n'}\sqrt{2}\mapsto [(mn'+nm'\sqrt{2},nn')]
|
||||||
|
$$
|
||||||
|
|
||||||
|
And use rationalization on the forward direction.
|
||||||
|
|
||||||
|
</details>
|
||||||
|
|
||||||
|
#### Polynomial rings
|
||||||
|
|
||||||
|
Let $R$ be a ring, a polynomial with coefficients in $R$ is a sum
|
||||||
|
|
||||||
|
$$
|
||||||
|
a_0+a_1x+\cdots+a_nx^n
|
||||||
|
$$
|
||||||
|
|
||||||
|
where $a_i\in R$. $x$ is indeterminate, $a_0,a_1,\cdots,a_n$ are called coefficients. $a_0$ is the constant term.
|
||||||
|
|
||||||
|
If $f$ is a non-zero polynomial, then the degree of $f$ is defined as the largest $n$ such that $a_n\neq 0$.
|
||||||
|
|
||||||
|
<details>
|
||||||
|
<summary>Example</summary>
|
||||||
|
|
||||||
|
Let $f=1+2x+0x^2-1x^3+0x^4$, then $deg f=3$
|
||||||
|
|
||||||
|
</details>
|
||||||
|
|
||||||
|
If $R$ has a unity $1$, then we write $x^m$ instead of $1x^m$.
|
||||||
|
|
||||||
|
Let $R[x]$ denote the set of all polynomials with coefficients in $R$.
|
||||||
|
|
||||||
|
We define multiplication and addition on $R[x]$.
|
||||||
|
|
||||||
|
$f:a_0+a_1x+\cdots+a_nx^n$
|
||||||
|
|
||||||
|
$g:b_0+b_1x+\cdots+b_mx^m$
|
||||||
|
|
||||||
|
Define,
|
||||||
|
|
||||||
|
$$
|
||||||
|
f+g=a_0+b_0+a_1x+b_1x+\cdots+a_nx^n+b_mx^m
|
||||||
|
$$
|
||||||
|
|
||||||
|
$$
|
||||||
|
fg=(a_0b_0)+(a_1b_0)x+\cdots+(a_nb_m)x^m
|
||||||
|
$$
|
||||||
|
|
||||||
|
In general, the coefficient of $x^m=\sum_{i=0}^{m}a_ix^{m-i}$.
|
||||||
|
|
||||||
|
> [!CAUTION]
|
||||||
|
>
|
||||||
|
> The field $R$ may not be commutative, follow the order of computation matters.
|
||||||
|
|
||||||
|
We will show that this is a ring and explore additional properties.
|
||||||
@@ -23,4 +23,12 @@ export default {
|
|||||||
Math4302_L18: "Modern Algebra (Lecture 18)",
|
Math4302_L18: "Modern Algebra (Lecture 18)",
|
||||||
Math4302_L19: "Modern Algebra (Lecture 19)",
|
Math4302_L19: "Modern Algebra (Lecture 19)",
|
||||||
Math4302_L20: "Modern Algebra (Lecture 20)",
|
Math4302_L20: "Modern Algebra (Lecture 20)",
|
||||||
|
Math4302_L21: "Modern Algebra (Lecture 21)",
|
||||||
|
Math4302_L22: "Modern Algebra (Lecture 22)",
|
||||||
|
Math4302_L23: "Modern Algebra (Lecture 23)",
|
||||||
|
Math4302_L24: "Modern Algebra (Lecture 24)",
|
||||||
|
Math4302_L25: "Modern Algebra (Lecture 25)",
|
||||||
|
Math4302_L26: "Modern Algebra (Lecture 26)",
|
||||||
|
Math4302_L27: "Modern Algebra (Lecture 27)",
|
||||||
|
Math4302_L28: "Modern Algebra (Lecture 28)",
|
||||||
}
|
}
|
||||||
|
|||||||
207
mcp-server.mjs
Normal file
207
mcp-server.mjs
Normal file
@@ -0,0 +1,207 @@
|
|||||||
|
import fs from 'node:fs/promises'
|
||||||
|
import path from 'node:path'
|
||||||
|
import process from 'node:process'
|
||||||
|
|
||||||
|
import { Server } from '@modelcontextprotocol/sdk/server/index.js'
|
||||||
|
import { StdioServerTransport } from '@modelcontextprotocol/sdk/server/stdio.js'
|
||||||
|
import {
|
||||||
|
CallToolRequestSchema,
|
||||||
|
ListToolsRequestSchema
|
||||||
|
} from '@modelcontextprotocol/sdk/types.js'
|
||||||
|
|
||||||
|
const CONTENT_ROOT = path.join(process.cwd(), 'content')
|
||||||
|
const NOTE_EXTENSIONS = new Set(['.md', '.mdx'])
|
||||||
|
const MAX_SEARCH_RESULTS = 10
|
||||||
|
const SNIPPET_RADIUS = 220
|
||||||
|
|
||||||
|
async function walkNotes(dir = CONTENT_ROOT) {
|
||||||
|
const entries = await fs.readdir(dir, { withFileTypes: true })
|
||||||
|
const notes = await Promise.all(entries.map(async (entry) => {
|
||||||
|
const fullPath = path.join(dir, entry.name)
|
||||||
|
if (entry.isDirectory()) {
|
||||||
|
return walkNotes(fullPath)
|
||||||
|
}
|
||||||
|
|
||||||
|
if (!entry.isFile() || !NOTE_EXTENSIONS.has(path.extname(entry.name))) {
|
||||||
|
return []
|
||||||
|
}
|
||||||
|
|
||||||
|
const relativePath = path.relative(CONTENT_ROOT, fullPath).replaceAll('\\', '/')
|
||||||
|
const slug = relativePath.replace(/\.(md|mdx)$/i, '')
|
||||||
|
return [{
|
||||||
|
fullPath,
|
||||||
|
relativePath,
|
||||||
|
slug,
|
||||||
|
title: path.basename(slug)
|
||||||
|
}]
|
||||||
|
}))
|
||||||
|
|
||||||
|
return notes.flat().sort((a, b) => a.relativePath.localeCompare(b.relativePath))
|
||||||
|
}
|
||||||
|
|
||||||
|
function normalizeNoteId(noteId = '') {
|
||||||
|
const normalized = String(noteId).trim().replaceAll('\\', '/').replace(/^\/+|\/+$/g, '')
|
||||||
|
if (!normalized || normalized.includes('..')) {
|
||||||
|
return null
|
||||||
|
}
|
||||||
|
|
||||||
|
return normalized
|
||||||
|
}
|
||||||
|
|
||||||
|
async function resolveNote(noteId) {
|
||||||
|
const normalized = normalizeNoteId(noteId)
|
||||||
|
if (!normalized) {
|
||||||
|
return null
|
||||||
|
}
|
||||||
|
|
||||||
|
const notes = await walkNotes()
|
||||||
|
return notes.find((note) =>
|
||||||
|
note.slug === normalized ||
|
||||||
|
note.relativePath === normalized ||
|
||||||
|
note.relativePath.replace(/\.(md|mdx)$/i, '') === normalized
|
||||||
|
) ?? null
|
||||||
|
}
|
||||||
|
|
||||||
|
function buildSnippet(content, index, query) {
|
||||||
|
const start = Math.max(0, index - SNIPPET_RADIUS)
|
||||||
|
const end = Math.min(content.length, index + query.length + SNIPPET_RADIUS)
|
||||||
|
return content
|
||||||
|
.slice(start, end)
|
||||||
|
.replace(/\s+/g, ' ')
|
||||||
|
.trim()
|
||||||
|
}
|
||||||
|
|
||||||
|
function textResponse(text) {
|
||||||
|
return {
|
||||||
|
content: [{ type: 'text', text }]
|
||||||
|
}
|
||||||
|
}
|
||||||
|
|
||||||
|
const server = new Server(
|
||||||
|
{
|
||||||
|
name: 'notenextra-notes',
|
||||||
|
version: '1.0.0'
|
||||||
|
},
|
||||||
|
{
|
||||||
|
capabilities: {
|
||||||
|
tools: {}
|
||||||
|
}
|
||||||
|
}
|
||||||
|
)
|
||||||
|
|
||||||
|
server.setRequestHandler(ListToolsRequestSchema, async () => ({
|
||||||
|
tools: [
|
||||||
|
{
|
||||||
|
name: 'list_notes',
|
||||||
|
description: 'List available notes from the Next.js content directory.',
|
||||||
|
inputSchema: {
|
||||||
|
type: 'object',
|
||||||
|
properties: {
|
||||||
|
course: {
|
||||||
|
type: 'string',
|
||||||
|
description: 'Optional course or directory prefix, for example CSE442T or Math4201.'
|
||||||
|
}
|
||||||
|
}
|
||||||
|
}
|
||||||
|
},
|
||||||
|
{
|
||||||
|
name: 'read_note',
|
||||||
|
description: 'Read a note by slug or relative path, for example CSE442T/CSE442T_L1.',
|
||||||
|
inputSchema: {
|
||||||
|
type: 'object',
|
||||||
|
properties: {
|
||||||
|
noteId: {
|
||||||
|
type: 'string',
|
||||||
|
description: 'Note slug or relative path inside content/.'
|
||||||
|
}
|
||||||
|
},
|
||||||
|
required: ['noteId']
|
||||||
|
}
|
||||||
|
},
|
||||||
|
{
|
||||||
|
name: 'search_notes',
|
||||||
|
description: 'Search the notes knowledge base using a simple text match over all markdown content.',
|
||||||
|
inputSchema: {
|
||||||
|
type: 'object',
|
||||||
|
properties: {
|
||||||
|
query: {
|
||||||
|
type: 'string',
|
||||||
|
description: 'Search term or phrase.'
|
||||||
|
},
|
||||||
|
limit: {
|
||||||
|
type: 'number',
|
||||||
|
description: `Maximum results to return, capped at ${MAX_SEARCH_RESULTS}.`
|
||||||
|
}
|
||||||
|
},
|
||||||
|
required: ['query']
|
||||||
|
}
|
||||||
|
}
|
||||||
|
]
|
||||||
|
}))
|
||||||
|
|
||||||
|
server.setRequestHandler(CallToolRequestSchema, async (request) => {
|
||||||
|
const { name, arguments: args = {} } = request.params
|
||||||
|
|
||||||
|
if (name === 'list_notes') {
|
||||||
|
const notes = await walkNotes()
|
||||||
|
const course = typeof args.course === 'string'
|
||||||
|
? args.course.trim().toLowerCase()
|
||||||
|
: ''
|
||||||
|
const filtered = course
|
||||||
|
? notes.filter((note) => note.relativePath.toLowerCase().startsWith(`${course}/`))
|
||||||
|
: notes
|
||||||
|
|
||||||
|
return textResponse(filtered.map((note) => note.slug).join('\n') || 'No notes found.')
|
||||||
|
}
|
||||||
|
|
||||||
|
if (name === 'read_note') {
|
||||||
|
const note = await resolveNote(args.noteId)
|
||||||
|
if (!note) {
|
||||||
|
return textResponse('Note not found.')
|
||||||
|
}
|
||||||
|
|
||||||
|
const content = await fs.readFile(note.fullPath, 'utf8')
|
||||||
|
return textResponse(`# ${note.slug}\n\n${content}`)
|
||||||
|
}
|
||||||
|
|
||||||
|
if (name === 'search_notes') {
|
||||||
|
const query = typeof args.query === 'string' ? args.query.trim() : ''
|
||||||
|
if (!query) {
|
||||||
|
return textResponse('Query must be a non-empty string.')
|
||||||
|
}
|
||||||
|
|
||||||
|
const limit = Math.max(1, Math.min(Number(args.limit) || 5, MAX_SEARCH_RESULTS))
|
||||||
|
const queryLower = query.toLowerCase()
|
||||||
|
const notes = await walkNotes()
|
||||||
|
const matches = []
|
||||||
|
|
||||||
|
for (const note of notes) {
|
||||||
|
const content = await fs.readFile(note.fullPath, 'utf8')
|
||||||
|
const haystack = `${note.slug}\n${content}`
|
||||||
|
const index = haystack.toLowerCase().indexOf(queryLower)
|
||||||
|
if (index === -1) {
|
||||||
|
continue
|
||||||
|
}
|
||||||
|
|
||||||
|
matches.push({
|
||||||
|
note,
|
||||||
|
index,
|
||||||
|
snippet: buildSnippet(haystack, index, query)
|
||||||
|
})
|
||||||
|
}
|
||||||
|
|
||||||
|
matches.sort((a, b) => a.index - b.index || a.note.slug.localeCompare(b.note.slug))
|
||||||
|
|
||||||
|
return textResponse(
|
||||||
|
matches
|
||||||
|
.slice(0, limit)
|
||||||
|
.map(({ note, snippet }) => `- ${note.slug}\n${snippet}`)
|
||||||
|
.join('\n\n') || 'No matches found.'
|
||||||
|
)
|
||||||
|
}
|
||||||
|
|
||||||
|
throw new Error(`Unknown tool: ${name}`)
|
||||||
|
})
|
||||||
|
|
||||||
|
const transport = new StdioServerTransport()
|
||||||
|
await server.connect(transport)
|
||||||
227
mcp-worker/src/index.mjs
Normal file
227
mcp-worker/src/index.mjs
Normal file
@@ -0,0 +1,227 @@
|
|||||||
|
import { Server } from '@modelcontextprotocol/sdk/server/index.js'
|
||||||
|
import { WebStandardStreamableHTTPServerTransport } from '@modelcontextprotocol/sdk/server/webStandardStreamableHttp.js'
|
||||||
|
import {
|
||||||
|
CallToolRequestSchema,
|
||||||
|
ListToolsRequestSchema
|
||||||
|
} from '@modelcontextprotocol/sdk/types.js'
|
||||||
|
|
||||||
|
import { notesData } from '../generated/notes-data.mjs'
|
||||||
|
|
||||||
|
const MAX_SEARCH_RESULTS = 10
|
||||||
|
const SNIPPET_RADIUS = 220
|
||||||
|
const transports = new Map()
|
||||||
|
|
||||||
|
function normalizeNoteId(noteId = '') {
|
||||||
|
const normalized = String(noteId).trim().replaceAll('\\', '/').replace(/^\/+|\/+$/g, '')
|
||||||
|
if (!normalized || normalized.includes('..')) {
|
||||||
|
return null
|
||||||
|
}
|
||||||
|
|
||||||
|
return normalized
|
||||||
|
}
|
||||||
|
|
||||||
|
function resolveNote(noteId) {
|
||||||
|
const normalized = normalizeNoteId(noteId)
|
||||||
|
if (!normalized) {
|
||||||
|
return null
|
||||||
|
}
|
||||||
|
|
||||||
|
return notesData.find((note) =>
|
||||||
|
note.slug === normalized ||
|
||||||
|
note.relativePath === normalized ||
|
||||||
|
note.relativePath.replace(/\.(md|mdx)$/i, '') === normalized
|
||||||
|
) ?? null
|
||||||
|
}
|
||||||
|
|
||||||
|
function buildSnippet(content, index, query) {
|
||||||
|
const start = Math.max(0, index - SNIPPET_RADIUS)
|
||||||
|
const end = Math.min(content.length, index + query.length + SNIPPET_RADIUS)
|
||||||
|
return content
|
||||||
|
.slice(start, end)
|
||||||
|
.replace(/\s+/g, ' ')
|
||||||
|
.trim()
|
||||||
|
}
|
||||||
|
|
||||||
|
function textResponse(text) {
|
||||||
|
return {
|
||||||
|
content: [{ type: 'text', text }]
|
||||||
|
}
|
||||||
|
}
|
||||||
|
|
||||||
|
function createServer() {
|
||||||
|
const server = new Server(
|
||||||
|
{
|
||||||
|
name: 'notenextra-notes-worker',
|
||||||
|
version: '1.0.0'
|
||||||
|
},
|
||||||
|
{
|
||||||
|
capabilities: {
|
||||||
|
tools: {}
|
||||||
|
}
|
||||||
|
}
|
||||||
|
)
|
||||||
|
|
||||||
|
server.setRequestHandler(ListToolsRequestSchema, async () => ({
|
||||||
|
tools: [
|
||||||
|
{
|
||||||
|
name: 'list_notes',
|
||||||
|
description: 'List available notes from the generated notes knowledge base.',
|
||||||
|
inputSchema: {
|
||||||
|
type: 'object',
|
||||||
|
properties: {
|
||||||
|
course: {
|
||||||
|
type: 'string',
|
||||||
|
description: 'Optional course or directory prefix, for example CSE442T or Math4201.'
|
||||||
|
}
|
||||||
|
}
|
||||||
|
}
|
||||||
|
},
|
||||||
|
{
|
||||||
|
name: 'read_note',
|
||||||
|
description: 'Read a note by slug or relative path, for example CSE442T/CSE442T_L1.',
|
||||||
|
inputSchema: {
|
||||||
|
type: 'object',
|
||||||
|
properties: {
|
||||||
|
noteId: {
|
||||||
|
type: 'string',
|
||||||
|
description: 'Note slug or relative path inside content/.'
|
||||||
|
}
|
||||||
|
},
|
||||||
|
required: ['noteId']
|
||||||
|
}
|
||||||
|
},
|
||||||
|
{
|
||||||
|
name: 'search_notes',
|
||||||
|
description: 'Search the notes knowledge base using a simple text match over all markdown content.',
|
||||||
|
inputSchema: {
|
||||||
|
type: 'object',
|
||||||
|
properties: {
|
||||||
|
query: {
|
||||||
|
type: 'string',
|
||||||
|
description: 'Search term or phrase.'
|
||||||
|
},
|
||||||
|
limit: {
|
||||||
|
type: 'number',
|
||||||
|
description: `Maximum results to return, capped at ${MAX_SEARCH_RESULTS}.`
|
||||||
|
}
|
||||||
|
},
|
||||||
|
required: ['query']
|
||||||
|
}
|
||||||
|
}
|
||||||
|
]
|
||||||
|
}))
|
||||||
|
|
||||||
|
server.setRequestHandler(CallToolRequestSchema, async (request) => {
|
||||||
|
const { name, arguments: args = {} } = request.params
|
||||||
|
|
||||||
|
if (name === 'list_notes') {
|
||||||
|
const course = typeof args.course === 'string'
|
||||||
|
? args.course.trim().toLowerCase()
|
||||||
|
: ''
|
||||||
|
const filtered = course
|
||||||
|
? notesData.filter((note) => note.relativePath.toLowerCase().startsWith(`${course}/`))
|
||||||
|
: notesData
|
||||||
|
|
||||||
|
return textResponse(filtered.map((note) => note.slug).join('\n') || 'No notes found.')
|
||||||
|
}
|
||||||
|
|
||||||
|
if (name === 'read_note') {
|
||||||
|
const note = resolveNote(args.noteId)
|
||||||
|
if (!note) {
|
||||||
|
return textResponse('Note not found.')
|
||||||
|
}
|
||||||
|
|
||||||
|
return textResponse(`# ${note.slug}\n\n${note.content}`)
|
||||||
|
}
|
||||||
|
|
||||||
|
if (name === 'search_notes') {
|
||||||
|
const query = typeof args.query === 'string' ? args.query.trim() : ''
|
||||||
|
if (!query) {
|
||||||
|
return textResponse('Query must be a non-empty string.')
|
||||||
|
}
|
||||||
|
|
||||||
|
const limit = Math.max(1, Math.min(Number(args.limit) || 5, MAX_SEARCH_RESULTS))
|
||||||
|
const queryLower = query.toLowerCase()
|
||||||
|
const matches = []
|
||||||
|
|
||||||
|
for (const note of notesData) {
|
||||||
|
const haystack = `${note.slug}\n${note.content}`
|
||||||
|
const index = haystack.toLowerCase().indexOf(queryLower)
|
||||||
|
if (index === -1) {
|
||||||
|
continue
|
||||||
|
}
|
||||||
|
|
||||||
|
matches.push({
|
||||||
|
note,
|
||||||
|
index,
|
||||||
|
snippet: buildSnippet(haystack, index, query)
|
||||||
|
})
|
||||||
|
}
|
||||||
|
|
||||||
|
matches.sort((a, b) => a.index - b.index || a.note.slug.localeCompare(b.note.slug))
|
||||||
|
|
||||||
|
return textResponse(
|
||||||
|
matches
|
||||||
|
.slice(0, limit)
|
||||||
|
.map(({ note, snippet }) => `- ${note.slug}\n${snippet}`)
|
||||||
|
.join('\n\n') || 'No matches found.'
|
||||||
|
)
|
||||||
|
}
|
||||||
|
|
||||||
|
throw new Error(`Unknown tool: ${name}`)
|
||||||
|
})
|
||||||
|
|
||||||
|
return server
|
||||||
|
}
|
||||||
|
|
||||||
|
async function handleMcpRequest(request) {
|
||||||
|
const sessionId = request.headers.get('mcp-session-id')
|
||||||
|
let transport = sessionId ? transports.get(sessionId) : undefined
|
||||||
|
|
||||||
|
if (!transport && request.method === 'POST') {
|
||||||
|
transport = new WebStandardStreamableHTTPServerTransport({
|
||||||
|
sessionIdGenerator: () => crypto.randomUUID(),
|
||||||
|
enableJsonResponse: true,
|
||||||
|
onsessioninitialized: (newSessionId) => {
|
||||||
|
transports.set(newSessionId, transport)
|
||||||
|
},
|
||||||
|
onsessionclosed: (closedSessionId) => {
|
||||||
|
transports.delete(closedSessionId)
|
||||||
|
}
|
||||||
|
})
|
||||||
|
|
||||||
|
transport.onclose = () => {
|
||||||
|
if (transport.sessionId) {
|
||||||
|
transports.delete(transport.sessionId)
|
||||||
|
}
|
||||||
|
}
|
||||||
|
|
||||||
|
const server = createServer()
|
||||||
|
await server.connect(transport)
|
||||||
|
}
|
||||||
|
|
||||||
|
if (!transport) {
|
||||||
|
return new Response('Invalid or missing MCP session.', { status: 400 })
|
||||||
|
}
|
||||||
|
|
||||||
|
return transport.handleRequest(request)
|
||||||
|
}
|
||||||
|
|
||||||
|
export default {
|
||||||
|
async fetch(request) {
|
||||||
|
const url = new URL(request.url)
|
||||||
|
|
||||||
|
if (url.pathname === '/health') {
|
||||||
|
return Response.json({
|
||||||
|
status: 'ok',
|
||||||
|
notes: notesData.length
|
||||||
|
})
|
||||||
|
}
|
||||||
|
|
||||||
|
if (url.pathname === '/mcp') {
|
||||||
|
return handleMcpRequest(request)
|
||||||
|
}
|
||||||
|
|
||||||
|
return new Response('Not found.', { status: 404 })
|
||||||
|
}
|
||||||
|
}
|
||||||
4
mcp-worker/wrangler.toml
Normal file
4
mcp-worker/wrangler.toml
Normal file
@@ -0,0 +1,4 @@
|
|||||||
|
name = "notenextra-mcp"
|
||||||
|
main = "src/index.mjs"
|
||||||
|
compatibility_date = "2025-02-13"
|
||||||
|
compatibility_flags = ["nodejs_compat"]
|
||||||
11
package.json
11
package.json
@@ -7,9 +7,16 @@
|
|||||||
"build:test": "cross-env ANALYZE=true NODE_OPTIONS='--inspect --max-old-space-size=4096' next build",
|
"build:test": "cross-env ANALYZE=true NODE_OPTIONS='--inspect --max-old-space-size=4096' next build",
|
||||||
"build:analyze": "cross-env ANALYZE=true NODE_OPTIONS='--max-old-space-size=16384' next build",
|
"build:analyze": "cross-env ANALYZE=true NODE_OPTIONS='--max-old-space-size=16384' next build",
|
||||||
"postbuild": "next-sitemap && pagefind --site .next/server/app --output-path out/_pagefind",
|
"postbuild": "next-sitemap && pagefind --site .next/server/app --output-path out/_pagefind",
|
||||||
"start": "next start"
|
"start": "next start",
|
||||||
|
"mcp:notes": "node ./mcp-server.mjs",
|
||||||
|
"mcp:worker:build-data": "node ./scripts/generate-mcp-worker-data.mjs",
|
||||||
|
"mcp:worker:deploy": "npm run mcp:worker:build-data && npx wrangler deploy --config mcp-worker/wrangler.toml",
|
||||||
|
"mcp:worker:deploy:dry-run": "npm run mcp:worker:build-data && npx wrangler deploy --dry-run --config mcp-worker/wrangler.toml",
|
||||||
|
"test:mcp": "node ./test/test-mcp-server.mjs",
|
||||||
|
"test:mcp:worker": "node ./test/test-mcp-worker.mjs"
|
||||||
},
|
},
|
||||||
"dependencies": {
|
"dependencies": {
|
||||||
|
"@modelcontextprotocol/sdk": "^1.18.1",
|
||||||
"@docsearch/css": "^4.3.1",
|
"@docsearch/css": "^4.3.1",
|
||||||
"@docsearch/react": "^4.3.1",
|
"@docsearch/react": "^4.3.1",
|
||||||
"@napi-rs/simple-git": "^0.1.22",
|
"@napi-rs/simple-git": "^0.1.22",
|
||||||
@@ -31,4 +38,4 @@
|
|||||||
"@types/node": "24.10.0",
|
"@types/node": "24.10.0",
|
||||||
"@types/react": "19.2.2"
|
"@types/react": "19.2.2"
|
||||||
}
|
}
|
||||||
}
|
}
|
||||||
|
|||||||
BIN
public/CSE4303/Feistel_network.png
Normal file
BIN
public/CSE4303/Feistel_network.png
Normal file
Binary file not shown.
|
After Width: | Height: | Size: 38 KiB |
BIN
public/CSE4303/Intel_SGX.png
Normal file
BIN
public/CSE4303/Intel_SGX.png
Normal file
Binary file not shown.
|
After Width: | Height: | Size: 456 KiB |
BIN
public/Math4202/Retraction_of_doubly_punctured_plane.jpg
Normal file
BIN
public/Math4202/Retraction_of_doubly_punctured_plane.jpg
Normal file
Binary file not shown.
|
After Width: | Height: | Size: 79 KiB |
47
scripts/generate-mcp-worker-data.mjs
Normal file
47
scripts/generate-mcp-worker-data.mjs
Normal file
@@ -0,0 +1,47 @@
|
|||||||
|
import fs from 'node:fs/promises'
|
||||||
|
import path from 'node:path'
|
||||||
|
import process from 'node:process'
|
||||||
|
|
||||||
|
const CONTENT_ROOT = path.join(process.cwd(), 'content')
|
||||||
|
const OUTPUT_DIR = path.join(process.cwd(), 'mcp-worker', 'generated')
|
||||||
|
const OUTPUT_FILE = path.join(OUTPUT_DIR, 'notes-data.mjs')
|
||||||
|
const NOTE_EXTENSIONS = new Set(['.md', '.mdx'])
|
||||||
|
|
||||||
|
async function walkNotes(dir = CONTENT_ROOT) {
|
||||||
|
const entries = await fs.readdir(dir, { withFileTypes: true })
|
||||||
|
const notes = await Promise.all(entries.map(async (entry) => {
|
||||||
|
const fullPath = path.join(dir, entry.name)
|
||||||
|
|
||||||
|
if (entry.isDirectory()) {
|
||||||
|
return walkNotes(fullPath)
|
||||||
|
}
|
||||||
|
|
||||||
|
if (!entry.isFile() || !NOTE_EXTENSIONS.has(path.extname(entry.name))) {
|
||||||
|
return []
|
||||||
|
}
|
||||||
|
|
||||||
|
const relativePath = path.relative(CONTENT_ROOT, fullPath).replaceAll('\\', '/')
|
||||||
|
const slug = relativePath.replace(/\.(md|mdx)$/i, '')
|
||||||
|
const content = await fs.readFile(fullPath, 'utf8')
|
||||||
|
|
||||||
|
return [{
|
||||||
|
slug,
|
||||||
|
relativePath,
|
||||||
|
title: path.basename(slug),
|
||||||
|
content
|
||||||
|
}]
|
||||||
|
}))
|
||||||
|
|
||||||
|
return notes.flat().sort((a, b) => a.relativePath.localeCompare(b.relativePath))
|
||||||
|
}
|
||||||
|
|
||||||
|
const notes = await walkNotes()
|
||||||
|
|
||||||
|
await fs.mkdir(OUTPUT_DIR, { recursive: true })
|
||||||
|
await fs.writeFile(
|
||||||
|
OUTPUT_FILE,
|
||||||
|
`export const notesData = ${JSON.stringify(notes, null, 2)};\n`,
|
||||||
|
'utf8'
|
||||||
|
)
|
||||||
|
|
||||||
|
process.stdout.write(`Generated ${notes.length} notes for MCP worker.\n`)
|
||||||
74
test/test-mcp-server.mjs
Normal file
74
test/test-mcp-server.mjs
Normal file
@@ -0,0 +1,74 @@
|
|||||||
|
import assert from 'node:assert/strict'
|
||||||
|
import path from 'node:path'
|
||||||
|
import process from 'node:process'
|
||||||
|
|
||||||
|
import { Client } from '@modelcontextprotocol/sdk/client/index.js'
|
||||||
|
import { StdioClientTransport } from '@modelcontextprotocol/sdk/client/stdio.js'
|
||||||
|
|
||||||
|
const transport = new StdioClientTransport({
|
||||||
|
command: process.execPath,
|
||||||
|
args: [path.join(process.cwd(), 'mcp-server.mjs')],
|
||||||
|
cwd: process.cwd(),
|
||||||
|
stderr: 'pipe'
|
||||||
|
})
|
||||||
|
|
||||||
|
let stderrOutput = ''
|
||||||
|
transport.stderr?.setEncoding('utf8')
|
||||||
|
transport.stderr?.on('data', (chunk) => {
|
||||||
|
stderrOutput += chunk
|
||||||
|
})
|
||||||
|
|
||||||
|
const client = new Client({
|
||||||
|
name: 'notenextra-mcp-test',
|
||||||
|
version: '1.0.0'
|
||||||
|
})
|
||||||
|
|
||||||
|
async function main() {
|
||||||
|
await client.connect(transport)
|
||||||
|
|
||||||
|
const toolListResponse = await client.listTools()
|
||||||
|
const toolNames = toolListResponse.tools.map((tool) => tool.name).sort()
|
||||||
|
assert.deepEqual(toolNames, ['list_notes', 'read_note', 'search_notes'])
|
||||||
|
|
||||||
|
const listNotesResponse = await client.callTool({
|
||||||
|
name: 'list_notes',
|
||||||
|
arguments: {
|
||||||
|
course: 'CSE442T'
|
||||||
|
}
|
||||||
|
})
|
||||||
|
const listedNotes = listNotesResponse.content[0].text
|
||||||
|
assert.match(listedNotes, /CSE442T\/CSE442T_L1/, 'list_notes should include CSE442T lecture notes')
|
||||||
|
|
||||||
|
const readNoteResponse = await client.callTool({
|
||||||
|
name: 'read_note',
|
||||||
|
arguments: {
|
||||||
|
noteId: 'about'
|
||||||
|
}
|
||||||
|
})
|
||||||
|
const aboutText = readNoteResponse.content[0].text
|
||||||
|
assert.match(aboutText, /# about/i)
|
||||||
|
assert.match(aboutText, /This is a static server for me to share my notes/i)
|
||||||
|
|
||||||
|
const searchResponse = await client.callTool({
|
||||||
|
name: 'search_notes',
|
||||||
|
arguments: {
|
||||||
|
query: "Kerckhoffs' principle",
|
||||||
|
limit: 3
|
||||||
|
}
|
||||||
|
})
|
||||||
|
const searchText = searchResponse.content[0].text
|
||||||
|
assert.match(searchText, /CSE442T\/CSE442T_L1/, 'search_notes should find the cryptography lecture')
|
||||||
|
assert.match(searchText, /Kerckhoffs/i)
|
||||||
|
}
|
||||||
|
|
||||||
|
try {
|
||||||
|
await main()
|
||||||
|
process.stdout.write('MCP server test passed.\n')
|
||||||
|
} catch (error) {
|
||||||
|
const suffix = stderrOutput ? `\nServer stderr:\n${stderrOutput}` : ''
|
||||||
|
process.stderr.write(`${error.stack || error}${suffix}\n`)
|
||||||
|
process.exitCode = 1
|
||||||
|
} finally {
|
||||||
|
await client.close().catch(() => {})
|
||||||
|
await transport.close().catch(() => {})
|
||||||
|
}
|
||||||
121
test/test-mcp-worker.mjs
Normal file
121
test/test-mcp-worker.mjs
Normal file
@@ -0,0 +1,121 @@
|
|||||||
|
import assert from 'node:assert/strict'
|
||||||
|
import process from 'node:process'
|
||||||
|
|
||||||
|
import worker from '../mcp-worker/src/index.mjs'
|
||||||
|
import { LATEST_PROTOCOL_VERSION } from '@modelcontextprotocol/sdk/types.js'
|
||||||
|
|
||||||
|
function makeJsonRequest(url, body, headers = {}) {
|
||||||
|
return new Request(url, {
|
||||||
|
method: 'POST',
|
||||||
|
headers: {
|
||||||
|
accept: 'application/json, text/event-stream',
|
||||||
|
'content-type': 'application/json',
|
||||||
|
...headers
|
||||||
|
},
|
||||||
|
body: JSON.stringify(body)
|
||||||
|
})
|
||||||
|
}
|
||||||
|
|
||||||
|
const baseUrl = 'https://example.com'
|
||||||
|
|
||||||
|
const healthResponse = await worker.fetch(new Request(`${baseUrl}/health`))
|
||||||
|
assert.equal(healthResponse.status, 200)
|
||||||
|
const healthJson = await healthResponse.json()
|
||||||
|
assert.equal(healthJson.status, 'ok')
|
||||||
|
assert.ok(healthJson.notes > 0)
|
||||||
|
|
||||||
|
const initializeResponse = await worker.fetch(makeJsonRequest(`${baseUrl}/mcp`, {
|
||||||
|
jsonrpc: '2.0',
|
||||||
|
id: 1,
|
||||||
|
method: 'initialize',
|
||||||
|
params: {
|
||||||
|
protocolVersion: LATEST_PROTOCOL_VERSION,
|
||||||
|
capabilities: {},
|
||||||
|
clientInfo: {
|
||||||
|
name: 'notenextra-worker-test',
|
||||||
|
version: '1.0.0'
|
||||||
|
}
|
||||||
|
}
|
||||||
|
}))
|
||||||
|
|
||||||
|
assert.equal(initializeResponse.status, 200)
|
||||||
|
const sessionId = initializeResponse.headers.get('mcp-session-id')
|
||||||
|
assert.ok(sessionId, 'initialize should return an MCP session ID')
|
||||||
|
const protocolVersion = initializeResponse.headers.get('mcp-protocol-version') || LATEST_PROTOCOL_VERSION
|
||||||
|
const initializeJson = await initializeResponse.json()
|
||||||
|
assert.ok(initializeJson.result, 'initialize should return a result payload')
|
||||||
|
|
||||||
|
const toolListResponse = await worker.fetch(makeJsonRequest(`${baseUrl}/mcp`, {
|
||||||
|
jsonrpc: '2.0',
|
||||||
|
id: 2,
|
||||||
|
method: 'tools/list',
|
||||||
|
params: {}
|
||||||
|
}, {
|
||||||
|
'mcp-protocol-version': protocolVersion,
|
||||||
|
'mcp-session-id': sessionId
|
||||||
|
}))
|
||||||
|
|
||||||
|
assert.equal(toolListResponse.status, 200)
|
||||||
|
const toolListJson = await toolListResponse.json()
|
||||||
|
const toolNames = toolListJson.result.tools.map((tool) => tool.name).sort()
|
||||||
|
assert.deepEqual(toolNames, ['list_notes', 'read_note', 'search_notes'])
|
||||||
|
|
||||||
|
const listNotesResponse = await worker.fetch(makeJsonRequest(`${baseUrl}/mcp`, {
|
||||||
|
jsonrpc: '2.0',
|
||||||
|
id: 3,
|
||||||
|
method: 'tools/call',
|
||||||
|
params: {
|
||||||
|
name: 'list_notes',
|
||||||
|
arguments: {
|
||||||
|
course: 'CSE442T'
|
||||||
|
}
|
||||||
|
}
|
||||||
|
}, {
|
||||||
|
'mcp-protocol-version': protocolVersion,
|
||||||
|
'mcp-session-id': sessionId
|
||||||
|
}))
|
||||||
|
|
||||||
|
assert.equal(listNotesResponse.status, 200)
|
||||||
|
const listNotesJson = await listNotesResponse.json()
|
||||||
|
assert.match(listNotesJson.result.content[0].text, /CSE442T\/CSE442T_L1/)
|
||||||
|
|
||||||
|
const readNoteResponse = await worker.fetch(makeJsonRequest(`${baseUrl}/mcp`, {
|
||||||
|
jsonrpc: '2.0',
|
||||||
|
id: 4,
|
||||||
|
method: 'tools/call',
|
||||||
|
params: {
|
||||||
|
name: 'read_note',
|
||||||
|
arguments: {
|
||||||
|
noteId: 'about'
|
||||||
|
}
|
||||||
|
}
|
||||||
|
}, {
|
||||||
|
'mcp-protocol-version': protocolVersion,
|
||||||
|
'mcp-session-id': sessionId
|
||||||
|
}))
|
||||||
|
|
||||||
|
assert.equal(readNoteResponse.status, 200)
|
||||||
|
const readNoteJson = await readNoteResponse.json()
|
||||||
|
assert.match(readNoteJson.result.content[0].text, /This is a static server for me to share my notes/i)
|
||||||
|
|
||||||
|
const searchResponse = await worker.fetch(makeJsonRequest(`${baseUrl}/mcp`, {
|
||||||
|
jsonrpc: '2.0',
|
||||||
|
id: 5,
|
||||||
|
method: 'tools/call',
|
||||||
|
params: {
|
||||||
|
name: 'search_notes',
|
||||||
|
arguments: {
|
||||||
|
query: "Kerckhoffs' principle",
|
||||||
|
limit: 3
|
||||||
|
}
|
||||||
|
}
|
||||||
|
}, {
|
||||||
|
'mcp-protocol-version': protocolVersion,
|
||||||
|
'mcp-session-id': sessionId
|
||||||
|
}))
|
||||||
|
|
||||||
|
assert.equal(searchResponse.status, 200)
|
||||||
|
const searchJson = await searchResponse.json()
|
||||||
|
assert.match(searchJson.result.content[0].text, /CSE442T\/CSE442T_L1/)
|
||||||
|
|
||||||
|
process.stdout.write('MCP worker test passed.\n')
|
||||||
Reference in New Issue
Block a user